OCRFix Botnet Uses ClickFix Phishing and Blockchain C2
OCRFix botnet trojan spreads through fake CAPTCHA tricks and blockchain-stored commands. It impersonates Tesseract OCR software to infect Windows machines. Cyjax researchers uncovered this campaign blending social engineering with EtherHiding techniques.
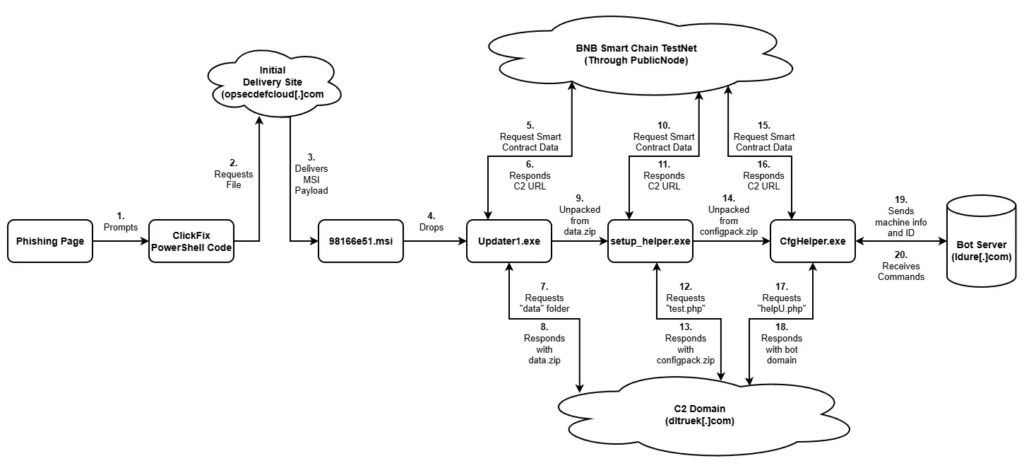
Attackers created a typosquatted site mimicking tesseract-ocr.com. The real Tesseract lives only on GitHub with no official domain. Victims hit a fake CAPTCHA. Clicking “verify” copies obfuscated PowerShell to the clipboard. The page urges pasting it into PowerShell.
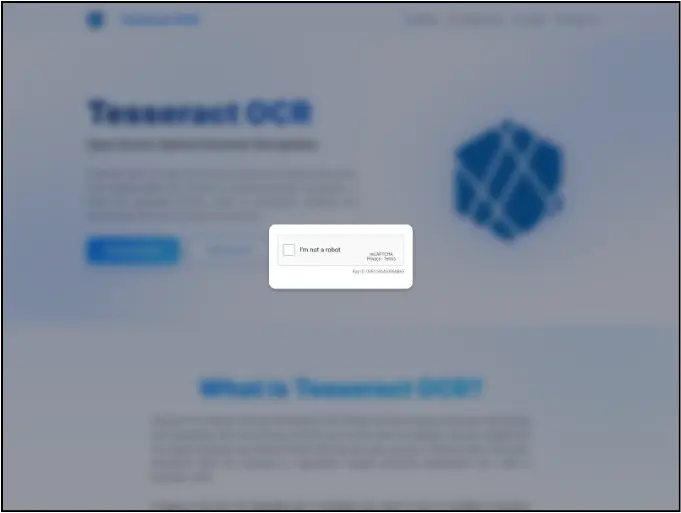
The command fetches an MSI file from opsecdefcloud.com. Execution redirects users to legit GitHub afterward. No alarms trigger. Victims stay blind to the breach.
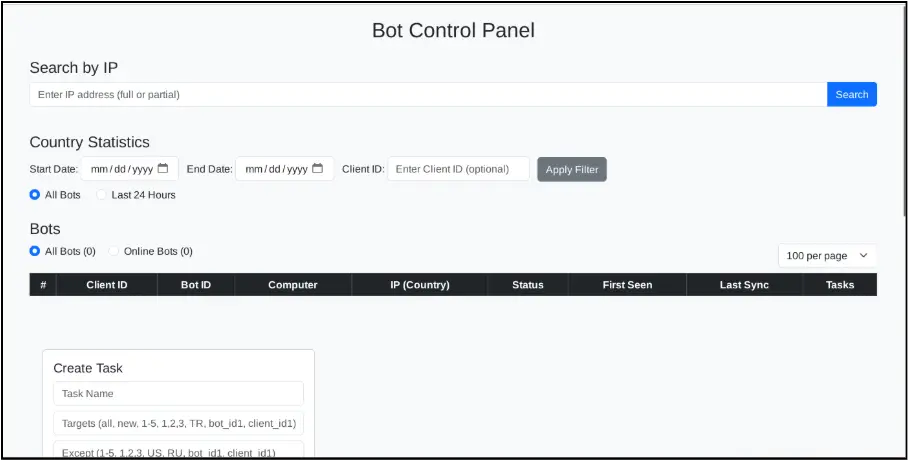
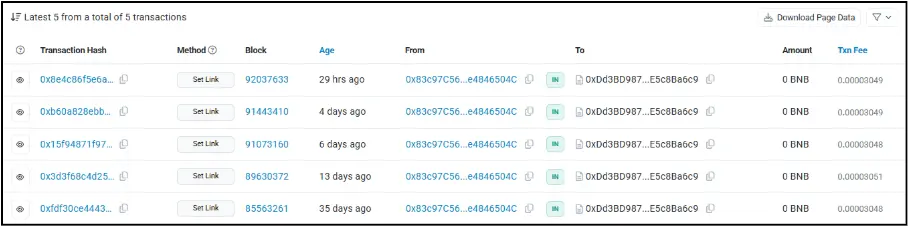
MSI unpacks in three stages. Update1.exe queries BNB TestNet smart contracts for next steps. It grabs data.zip from attacker servers. setup_helper.exe sets persistence via scheduled tasks running every minute at max privileges. It dodges Windows Defender exclusions.
CfgHelper.exe phones home to ldture.com with system details: IP, OS, hostname, unique IDs. Cyrillic code hints at Russian operators, but stays unconfirmed.
Infection Chain
| Stage | File | Action |
|---|---|---|
| 1 | Update1.exe | Queries BNB blockchain for C2, downloads data.zip |
| 2 | setup_helper.exe | Creates scheduled task, Defender bypass |
| 3 | CfgHelper.exe | Sends telemetry to ldture.com bot panel |
EtherHiding stores C2 URLs in BNB Smart Chain TestNet contracts. Malware reads from bsc-testnet.publicnode.com. Attackers update commands anytime without server seizures. North Korean groups used this before; now others adopt it.
Campaign poisons SEO and LLMs like ChatGPT. It pushes the fake site in responses. YouTube tutorials spread the phishing too.
Stealth keeps bots alive long-term. Clipboard tricks fool users. Blockchain defies takedowns. Bot panel tracks thousands quietly.
Key Indicators
- Phishing domain: tesseract-ocr[.]com
- MSI hash: 98166e51.msi
- C2: ldture[.]com, opsecdefcloud[.]com
- Blockchain: BNB TestNet contracts
- Task: Runs CfgHelper.exe every 60 seconds
Block PowerShell for non-admins. Log script blocks. Train on ClickFix CAPTCHAs. Flag WMI queries and odd tasks. Watch blockchain node traffic.
FAQ
Fake CAPTCHA on typosquatted Tesseract site copies PowerShell payload.
C2 URLs hide in BNB TestNet smart contracts, read at runtime.
Sets scheduled task for persistence, skips Defender scans.
Cyjax during threat monitoring
Domains: ldture.com, opsecdefcloud.com; BNB TestNet nodes.
Restrict PowerShell, monitor tasks, train on phishing CAPTCHAs.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages