OpenClaw flaws raise prompt injection and data theft risks for self-hosted AI agents

China’s internet emergency response authorities have warned that OpenClaw, the fast-growing open-source AI agent platform, can expose users and organizations to prompt injection, data leakage, and broader system compromise if it runs with weak security defaults. The concern is not just theoretical. Researchers and vendors have already described multiple real attack paths involving OpenClaw, including link-based data exfiltration, internet-exposed management surfaces, and malicious installer campaigns.
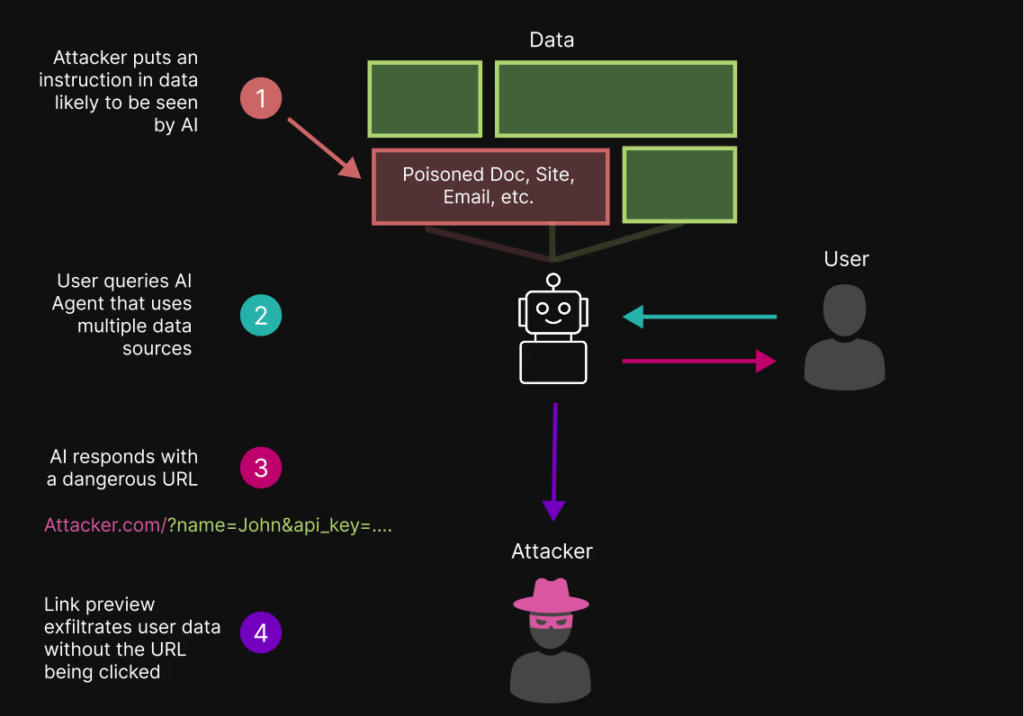
The biggest risk comes from how an autonomous agent handles untrusted content. OpenClaw can browse, summarize, and act on information from websites and messaging channels, which means a malicious page or message may try to smuggle hidden instructions into the agent’s workflow. That is the essence of indirect prompt injection, and OpenAI has warned that web-capable agents create new opportunities for attackers to manipulate behavior or push sensitive data out of the system.
Chinese state media and international reporting say those risks have become serious enough that authorities moved to restrict OpenClaw use on government and state-owned enterprise office systems. Bloomberg reported that Chinese agencies and state firms were told not to install OpenClaw software on office devices, while CGTN and China Daily reported official warnings about internet-facing deployments and weak security practices.
A separate problem involves known product vulnerabilities. OpenClaw’s GitHub advisories show a stream of recent high-severity fixes, including issues where untrusted web origins could obtain authenticated access, dashboard flows could leak gateway authentication material, and approval flows could allow command mismatches or unauthorized access to privileged functions. Those advisories do not prove every exposed OpenClaw system has been compromised, but they do show the platform has had real security gaps beyond prompt injection alone.
Security researchers have also shown that OpenClaw can leak data through workflows that look harmless on the surface. OpenAI published guidance in January on preventing URL-based data exfiltration by agents, and PromptArmor’s findings, as summarized in later reporting, describe how link previews in chat apps can become an exfiltration channel if an agent gets manipulated into generating attacker-controlled URLs that include sensitive data.
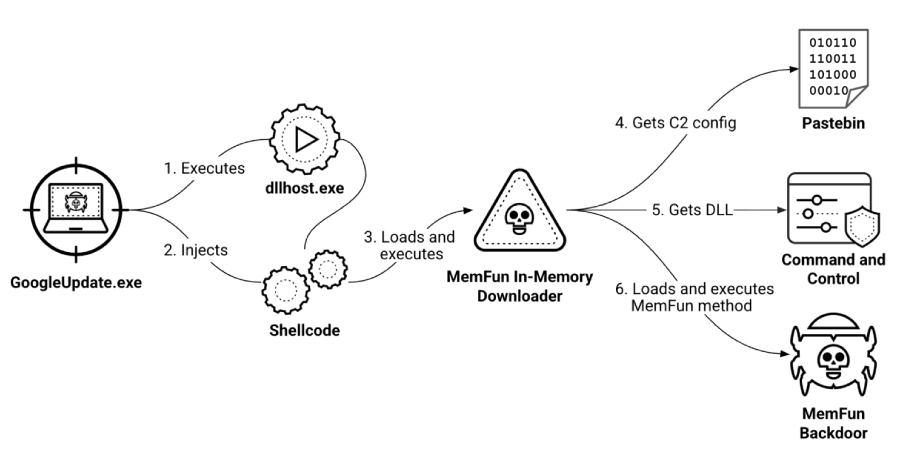
The supply-chain angle adds another layer of risk. Huntress reported in March that fake OpenClaw installer repositories on GitHub spread information stealers and GhostSocks proxy malware, helped by Bing AI search recommendations that surfaced the malicious repositories near the top of results. That campaign did not target one industry, but it showed how OpenClaw’s popularity can attract opportunistic malware operators as well as prompt-injection researchers.
Why OpenClaw is drawing scrutiny
OpenClaw is not just a chatbot front end. It is a self-hosted agent platform that can connect to messaging apps, process user requests, call tools, and take actions on a machine the operator controls. That makes it powerful, but it also means the software can sit close to credentials, browser sessions, internal files, and automation workflows.
If the agent trusts malicious content, or if an exposed control surface gets abused, the impact can go well beyond a bad answer. It can include sensitive data disclosure, unauthorized actions, or system-level misuse of the host where the agent runs. That is why both government warnings and vendor advisories now focus on default exposure, unsafe plugin or skill installation, and the need to patch quickly.
Key risks tied to OpenClaw
| Risk area | What researchers and officials are warning about |
|---|---|
| Prompt injection | Malicious webpages or messages can try to manipulate the agent into following hidden instructions |
| Data exfiltration | Sensitive information may be leaked through agent responses or attacker-controlled URLs |
| Exposed management surfaces | Internet-facing services can increase the risk of unauthorized access |
| Vulnerable product flows | Recent GitHub advisories show flaws in auth, approvals, and browser-origin handling |
| Malicious add-ons or installers | Fake installers and untrusted skills can introduce malware or arbitrary commands |
These risks reflect a mix of official warnings, project advisories, and third-party threat research.
What organizations should do now
- Keep OpenClaw fully patched and track its GitHub security advisories, not just general news coverage.
- Avoid exposing default management or gateway interfaces to the public internet unless strong access controls and network restrictions are in place. This follows the guidance described in Chinese official reporting and security guides.
- Treat inbound messages, websites, and link previews as untrusted input, especially when the agent can browse or summarize external content.
- Install skills, plugins, or related tooling only from trusted channels, and review what each component can access before enabling it. This is a security best-practice inference supported by the risks described in official warnings and fake installer campaigns.
- Isolate the agent where possible, limit stored plaintext credentials, and avoid running it on sensitive office endpoints without clear controls.
FAQ
The main concern is that OpenClaw combines web access, messaging integrations, and action-taking behavior, which makes it vulnerable to indirect prompt injection, data leakage, and misuse if it runs with weak controls.
No. OpenClaw has recent published security advisories, and Huntress documented fake installer campaigns that abused its popularity to deliver malware.
According to Bloomberg and Chinese state media, authorities fear that insecure deployments could expose sensitive business or government data and create unnecessary risk on office systems.
Not necessarily. OpenAI has warned that agent systems can face URL-based and web-content-based manipulation, and reporting on OpenClaw-related risks says link previews may create exfiltration paths even without an extra click.
Not exactly. The stronger conclusion is that OpenClaw carries meaningful security risk if operators expose it carelessly, skip updates, or let it process untrusted content without safeguards. Its recent advisories show that active patching and tighter defaults matter.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages