Palo Alto links CL-STA-1087 to long-running espionage campaign against Southeast Asian militaries
A long-running cyber espionage campaign tied with moderate confidence to China has targeted military organizations in Southeast Asia since at least 2020, according to Palo Alto Networks Unit 42. The researchers say the cluster, tracked as CL-STA-1087, focused on quiet intelligence collection rather than smash-and-grab theft, with a strong interest in military files, organizational structures, and collaboration with Western armed forces.
Palo Alto says the operators showed unusual patience. In some cases, they kept access for months, moved laterally across victim environments, and deployed custom malware only after building a foothold. The company says the campaign came to light after Cortex XDR detected suspicious PowerShell activity that slept for six hours before opening reverse shells to attacker-controlled infrastructure.
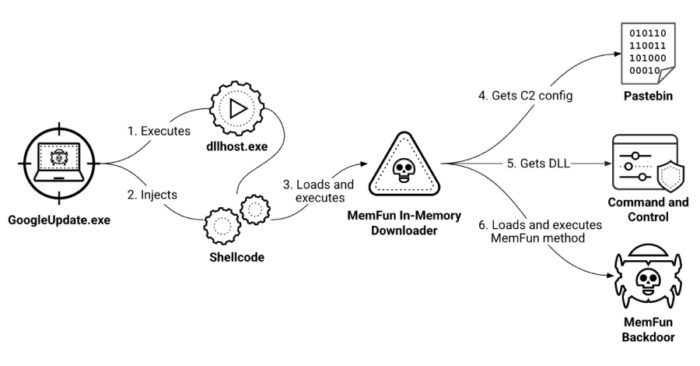
The malware set includes two custom backdoors, AppleChris and MemFun, plus a credential-harvesting tool called Getpass. Unit 42 says AppleChris supports file upload and download, directory listing, drive enumeration, process listing, remote shell execution, and silent process creation. MemFun is more modular and can fetch additional payloads at runtime, which gives the attackers flexibility without changing the initial loader.
The targeting also looks highly selective. Palo Alto says the attackers searched for files related to military capabilities, C4I systems, command structures, official meeting records, and joint exercises or partnerships with Western forces. That focus suggests a classic intelligence-gathering campaign aimed at defense planning and regional military visibility, not routine cybercrime.
One of the more interesting technical details is how the malware finds its real command server. Unit 42 says both AppleChris and MemFun use Pastebin as a dead drop resolver to retrieve the actual C2 address in Base64-decoded form. Some AppleChris variants also use Dropbox to pull the same information, with Pastebin acting as a fallback. Palo Alto says the Pastebin artifacts tied to the campaign date back to September 2020, which helps anchor the operation’s long timeline.
The delivery chain remains partly unresolved. Palo Alto says it does not know the exact initial access vector. What it does know is that AppleChris can arrive through DLL hijacking, while MemFun uses a multi-stage chain that includes shellcode, an in-memory downloader, and process hollowing into dllhost.exe. The malware also uses sandbox evasion through delayed execution, with some variants sleeping long enough to outlast common automated analysis windows.
Getpass rounds out the toolset. According to Unit 42, it is a custom Mimikatz variant that attempts to pull plaintext passwords, NTLM hashes, and other authentication data from lsass.exe. That fits the broader pattern of the campaign, where the attackers seem to value durable access and credential depth as much as document collection.
Palo Alto’s attribution language is careful. The company describes CL-STA-1087 as a suspected China-based, state-backed cluster rather than naming a known APT group. That wording matters because cybersecurity firms have become more cautious about public attributions, especially when evidence points to geography and tradecraft without a clean one-to-one match to an already labeled actor.
What Palo Alto says the malware can do
| Tool | Role in the campaign | Reported capabilities |
|---|---|---|
| AppleChris | Backdoor | Drive and process enumeration, file upload/download, directory listing, remote shell, silent process creation |
| MemFun | Modular backdoor platform | Fetches C2 config, loads DLLs at runtime, supports payload flexibility and in-memory execution |
| Getpass | Credential harvester | Extracts plaintext passwords, NTLM hashes, and authentication data from lsass.exe |
These capabilities come directly from Palo Alto Networks Unit 42’s report on CL-STA-1087.
Why this campaign matters
- The operation appears built for long-term intelligence collection, not quick monetization.
- The targets include military organizations in a strategically sensitive region.
- The malware uses dead drop resolvers on Pastebin and Dropbox to make infrastructure more resilient.
- The attackers searched for military planning, C4I, and Western cooperation files, which points to defense intelligence priorities.
- The tooling supports persistence, lateral movement, credential theft, and stealthy modular payload delivery.
What defenders should watch for
- Long sleep timers in PowerShell or loader activity, especially six-hour delays or staged reverse shell behavior.
- Access to Pastebin or Dropbox used as dead drop resolvers for C2 lookups.
- DLL hijacking patterns and process hollowing into
dllhost.exe. - Attempts to read
lsass.exememory or deploy custom Mimikatz-like tools. - Focused searches for defense, C4I, meeting, and joint-operation documents. This last point is an inference based on the file interests Palo Alto documented.
FAQ
Palo Alto Networks says the activity cluster, CL-STA-1087, is suspected to be China-based and state-backed. The company does not map it publicly to a named APT group.
Palo Alto says they sought highly specific files about military capabilities, structures, C4I systems, and collaboration with Western armed forces.
Unit 42 says AppleChris variants use Pastebin, and in some cases Dropbox, as dead drop resolvers to obtain the real C2 server address.
Palo Alto describes MemFun as more modular because it retrieves a DLL from the C2 at runtime, which lets operators swap payloads more easily.
No. The company says the exact initial access vector remains unknown.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages