Pay2Key Linux ransomware is targeting servers, virtualization hosts, and cloud workloads

Pay2Key’s Linux variant shows that ransomware operators are no longer focused mainly on desktop systems. Morphisec says the malware, tracked as Pay2Key.I2, targets the infrastructure layer instead, including servers, virtualization hosts, and cloud workloads that many organizations depend on every day. The company says the Linux build was first detected in the wild in late August 2025.
What makes this strain important is its design. Morphisec says the malware is configuration-driven, requires root privileges to run, and was built to move across a wide filesystem scope while encrypting data with ChaCha20 in either full or partial modes. In other words, this is not a stripped-down Linux copy of a Windows ransomware tool. It was built specifically for Linux environments and the systems that sit behind business operations.
The broader shift matters because Linux systems often run the workloads organizations cannot easily afford to lose. Application servers, databases, virtual machine hosts, and cloud instances can all become high-value targets. Morphisec argues that Linux ransomware remains under-documented in public research, which leaves many defenders less prepared than they should be.
What Pay2Key.I2 does once it gets root access
Morphisec says the ransomware requires root-level privileges before it can execute successfully. That means the operators are not depending on post-launch privilege escalation inside the malware itself. They expect to arrive with full access already in hand, which gives the payload control over the filesystem and major operating system functions from the start.
Once active, the malware prepares the environment before encryption begins. Your sample correctly noted that the ransomware disables SELinux and AppArmor, kills processes, and stops services that could interfere with file encryption. Those behaviors match Morphisec’s description of the Linux variant’s pre-encryption setup and defense suppression logic.
Morphisec also says the ransomware installs persistence through cron so it can resume after a reboot. That gives the malware a practical recovery path if an administrator restarts the server while the attack is underway.
How the ransomware selects what to encrypt
The Linux variant does not simply try to encrypt everything at once. Morphisec says Pay2Key.I2 parses /proc/mounts to map the system’s mounted filesystems, then classifies them and filters out pseudo-filesystems. It skips read-only mounts and processes the rest based on its internal configuration.
The malware also tries to avoid destabilizing the host too early. According to Morphisec, it skips ELF binaries, MZ binaries, and zero-length files during per-file processing. That behavior helps keep the system functional enough to continue the attack and eventually present the ransom demand.
This is one of the more important technical details in the campaign. The goal is not just destruction. It is controlled disruption that hurts the victim while preserving enough system function for the attacker to maintain leverage.
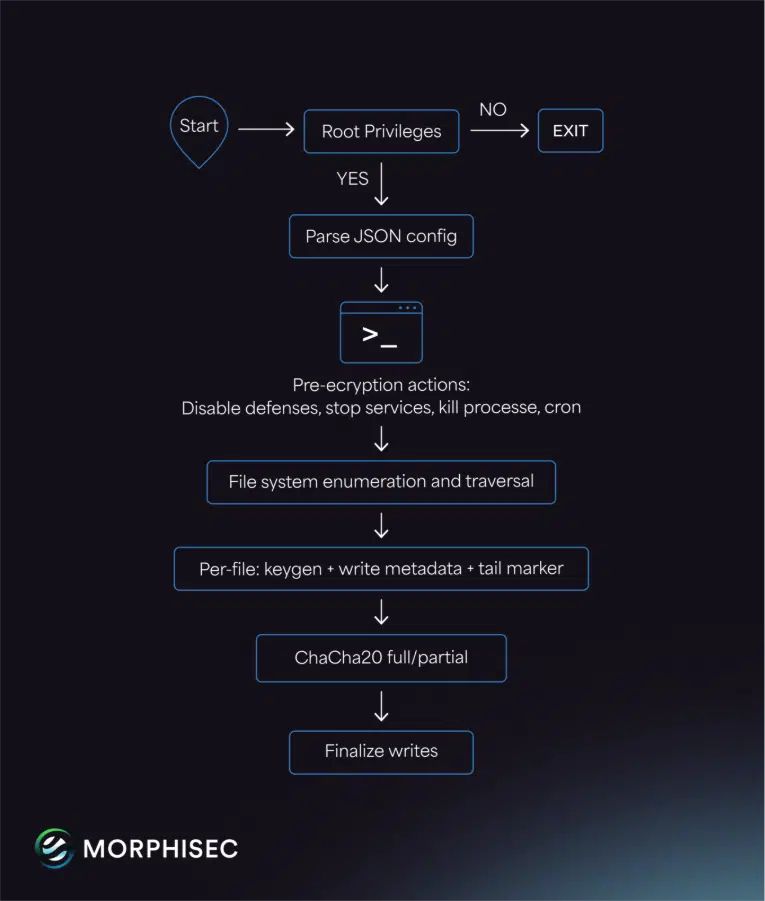
Encryption and evasion details
Morphisec says Pay2Key.I2 uses ChaCha20 for encryption. Depending on the configuration, it can run in full-file mode or partial mode, which lets the operators balance speed and impact based on the environment they hit.
The same report says a hardcoded string, DontDecompileMePlease, plays a role in metadata key derivation and metadata layout validation. Per-file keys are then generated and stored in an obfuscated metadata block, which complicates recovery without the attacker’s decryption material.
Those details matter because they show the Linux build was not thrown together quickly. It has an internal encryption scheme, environment preparation steps, persistence, and filesystem-aware targeting logic aimed at real infrastructure.
Why Linux defenders should pay attention
Linux has a reputation for being more resilient than Windows in some enterprise settings, but that does not make Linux infrastructure a weak target for ransomware. It often makes it a better one. Virtualization hosts, backend servers, and cloud workloads can create more operational pain than a fleet of locked employee laptops.
That is the real lesson in the Pay2Key.I2 research. The attackers are going after the systems that hold uptime together. If they already have root, they do not need fancy stealth to cause major disruption. They need reliability, speed, and an encryption routine that knows what to touch and what to avoid.
Key technical points
- Pay2Key.I2 is a Linux ransomware variant analyzed by Morphisec
- Morphisec says it was first seen in the wild in late August 2025
- The malware requires root privileges to execute
- It disables SELinux and AppArmor before encryption
- It creates cron-based persistence
- It enumerates
/proc/mountsto classify filesystems - It skips read-only mounts, ELF binaries, MZ binaries, and zero-length files
- It uses ChaCha20 in full or partial encryption mode
- It targets Linux infrastructure such as servers, virtualization hosts, and cloud workloads
Pay2Key.I2 attack chain at a glance
| Stage | What happens |
|---|---|
| Initial access | Attacker reaches the target with root-level privileges already available |
| Environment prep | Malware stops services, kills processes, and disables SELinux and AppArmor |
| Persistence | Cron entry is added so execution can resume after reboot |
| Filesystem mapping | /proc/mounts is parsed and mount points are classified |
| Target filtering | Read-only mounts and selected binary formats are skipped |
| Encryption | ChaCha20 encrypts files in full or partial mode based on configuration |
The structure above reflects the technical flow described by Morphisec and matches the core logic in the sample you shared.
What organizations should do now
- Restrict and audit root-level access aggressively
- Monitor for unexpected SELinux or AppArmor disablement
- Watch for suspicious cron creation or modification
- Audit access to virtualization hosts and cloud control paths
- Maintain offline and immutable backups
- Monitor Linux servers for unusual process killing and service stoppage
- Review which accounts can reach critical workloads with elevated privileges
These recommendations align with Morphisec’s technical findings and the defensive implications of a root-dependent Linux ransomware payload.
FAQ
It is a Linux ransomware variant analyzed by Morphisec. The company says it was first detected in the wild in late August 2025 and was built to target Linux infrastructure.
Morphisec says the Linux build is aimed at servers, virtualization hosts, and cloud workloads rather than traditional desktop-focused ransomware targets.
The ransomware requires root privileges to run. That gives it direct control over filesystems, services, and security settings such as SELinux and AppArmor.
Morphisec says the malware uses ChaCha20 and can encrypt files in either full or partial mode depending on its configuration.
The report says it installs a cron entry so it can continue running even if the victim reboots the host.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages