Philippine banking phishing campaign hides behind trusted platforms to steal credentials and OTPs

A long-running phishing campaign has targeted online banking users in the Philippines since early 2024, and it is still active in 2026. Group-IB says the operation uses compromised email accounts, trusted web platforms, and real-time credential theft to capture usernames, passwords, and one-time passwords, then enable fraudulent transfers.
The campaign does not target banks directly. It targets ordinary customers through phishing emails that claim a payment needs to be canceled, a suspicious device accessed the account, or contact details must be verified for security reasons. Group-IB says those themes changed over time, which helped the attackers keep the campaign effective.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
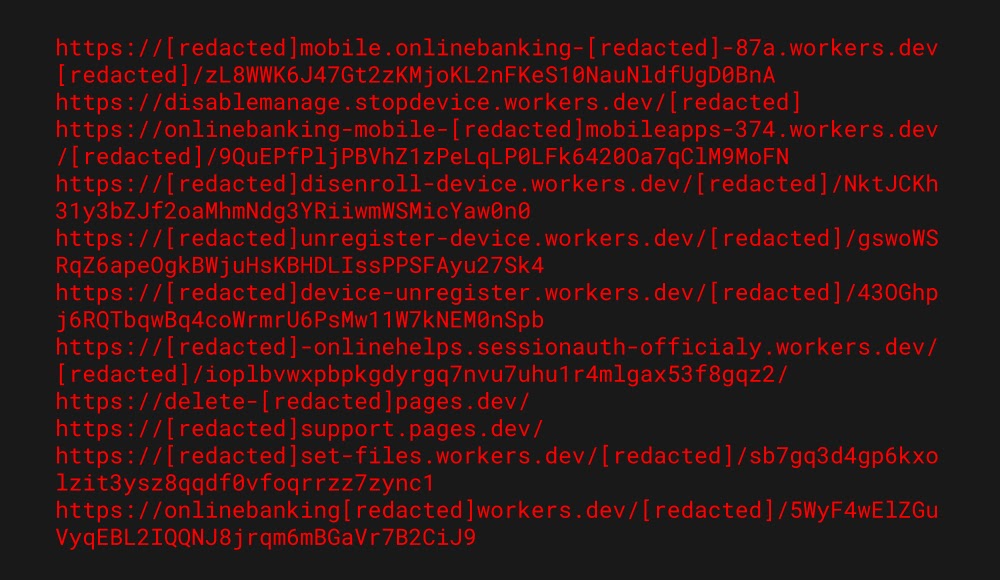
The scale is serious. Group-IB says more than 900 malicious links were distributed from January 2024 onward, at least three major Philippine banks were impersonated, and more than 400 victims were affected between January 2024 and January 2026. The researchers track the activity under the name PHISLES.
How the phishing emails gain trust
One reason this campaign works is the sender infrastructure. Group-IB says many phishing emails came from legitimate but compromised accounts rather than fake addresses, which made the messages look more trustworthy and helped some of them slip through email defenses.
The researchers say those accounts likely came from combolists, which are databases of stolen username and password pairs circulated in cybercrime channels. In this campaign, the attackers appear to have used already-compromised accounts to deliver phishing lures from real domains.
The wording inside the emails also did the heavy lifting. Some messages pushed victims to click a “Cancel Payment” button, while later waves warned about logins from suspicious devices or asked users to confirm their phone number or email address. Group-IB says that narrative evolution helped the actors keep the lures believable.
Why trusted platforms made the campaign harder to stop
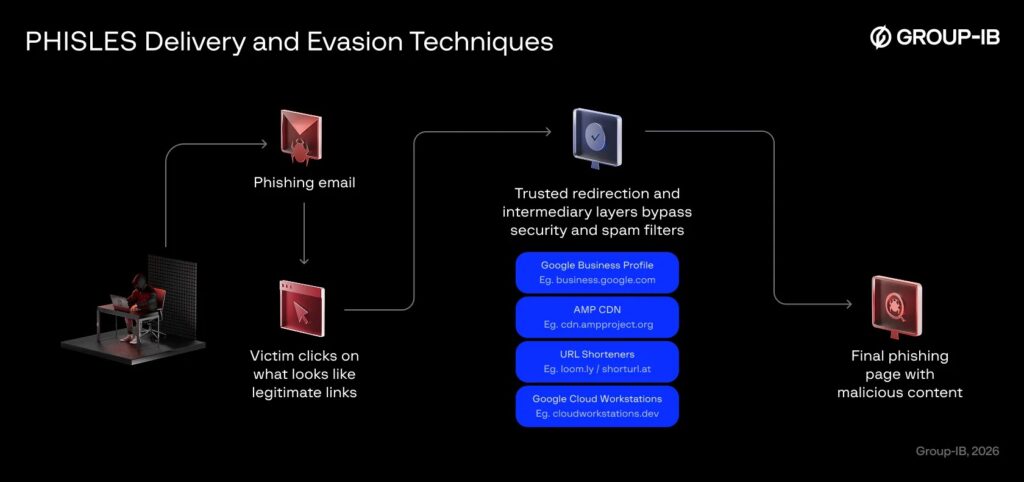
Around mid-2025, the attackers changed how they handled links. Instead of placing direct phishing links in emails, they increasingly routed victims through well-known services so the visible links looked safer and carried stronger domain reputation. Group-IB says this likely helped them evade secure email gateways and spam filters.
The report names several abused platforms, including Google Business Profile, Google AMP CDN, Google Cloud Workstations, URL shorteners such as loom.ly and shorturl.at, and Cloudflare-managed domains such as workers.dev and pages.dev. Each gave the attackers a trusted-looking layer between the email and the final phishing page.
Group-IB also found a more serious escalation. The attackers hijacked a legitimate educational domain in the Philippines, created subdomains under that real domain, obtained valid SSL certificates, and pointed the traffic to infrastructure they controlled. That let the phishing content operate under the cover of a real .ph institution.
How victims lose money in real time
Once a victim reaches the fake banking site, the goal is immediate fraud. Group-IB says the phishing flow captures the victim’s login details, then asks for the OTP sent to the victim’s phone, allowing the attackers to bypass multi-factor authentication in real time.
The phishing kit reportedly uses a session-based workflow so the attackers can track each victim step by step. Group-IB says the stolen data gets exfiltrated through Telegram bots, which lets the operators process credentials and OTPs quickly enough to support unauthorized transfers while the session remains valid.
To make the fake pages look convincing, the attackers also used a hotlinking technique. According to Group-IB, the phishing pages pulled scripts and other visual assets directly from the real bank infrastructure, which made the pages look more authentic and reduced suspicion for victims.
What security teams should watch for
| Indicator | What Group-IB observed |
|---|---|
| Initial delivery | Phishing emails from compromised legitimate accounts |
| Main targets | Online banking users in the Philippines |
| Themes used | Unauthorized transaction alerts, suspicious device logins, contact verification |
| Platforms abused | Google Business Profile, AMP CDN, Google Cloud Workstations, URL shorteners, Cloudflare workers.dev/pages.dev |
| Infrastructure escalation | Hijacked educational .ph domain with valid SSL certificates |
| Data theft method | Real-time credential and OTP exfiltration via Telegram bots |
| Impact | Fast account takeover and unauthorized fund transfers |
Source: Group-IB campaign analysis.
Steps banks and defenders should take
- Warn customers about active phishing emails that use transaction, device-login, and account-update themes.
- Hunt for traffic that loads bank assets from unexpected referrers, especially cloud subdomains or third-party infrastructure. Group-IB says the phishing kit hotlinked legitimate bank resources, which can expose suspicious Referer headers.
- Monitor for abuse involving trusted redirectors and cloud-hosted phishing pages rather than focusing only on newly registered malicious domains.
- Review DNS records for unauthorized subdomains and enforce MFA on registrar accounts, especially in schools and other organizations with public-facing domains.
- Treat OTP phishing as a live fraud event, not just a credential theft issue, because the campaign aims to complete transactions immediately.
FAQ
PHISLES is the name Group-IB uses for the threat actor or scheme behind this phishing campaign targeting banking users in the Philippines.
The targets are banking customers, not the banks themselves. Group-IB says at least three major Philippine banks were impersonated, but ordinary users were the victims.
They trick victims into entering the one-time password on a fake banking page, then use that code right away to authorize fraudulent activity.
The attackers hid behind reputable services and a hijacked educational domain, which made links look safer and harder for automated tools to block.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages