Phishers abuse LiveChat support tools to steal sensitive data in new SaaS-based tactic

A newly documented phishing campaign is abusing LiveChat-hosted pages to trick victims into handing over personal, financial, and authentication data through what looks like a legitimate support session. Cofense says the attacks use refund and order-confirmation lures, then move victims into live chat windows hosted under the lc.chat domain, where attackers harvest details in stages.
The tactic matters because it changes how phishing feels to the victim. Instead of sending users straight to a fake login page, the attackers place them inside a support-style conversation that looks more personal and more trustworthy. Cofense says that real-time interaction lowers suspicion and increases the chance that victims will share sensitive information.
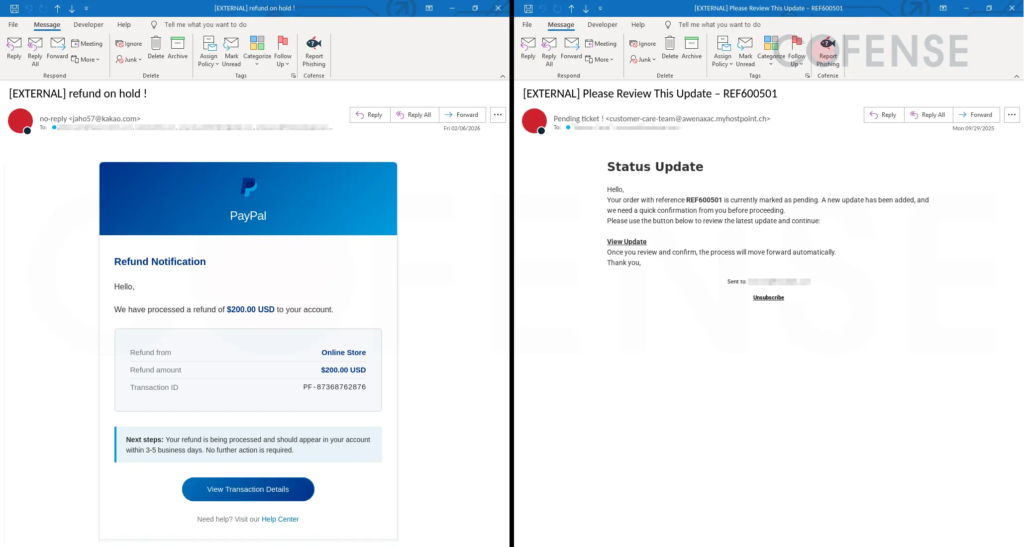
Cofense documented two variants. One spoofed PayPal and promised a $200 refund through a “View Transaction Details” button. The other used a generic order-confirmation lure with a “View Update” link and no visible brand until the victim clicked through. Both routes ended on LiveChat-hosted pages impersonating well-known brands.
How the attack works
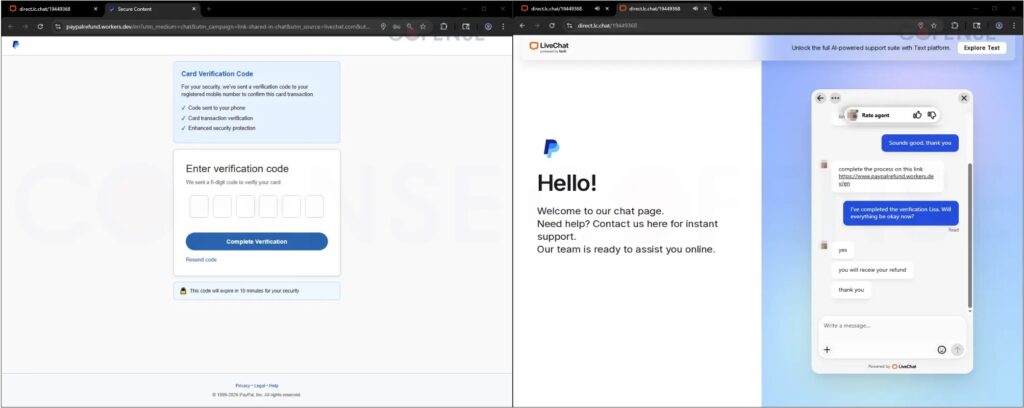
In the PayPal-themed version, the victim lands in a LiveChat session that quickly pushes them toward a fake PayPal login page. Cofense says the victim enters login credentials, then submits a multi-factor authentication code sent to their phone. After that, the phishing flow asks for billing details, including payment card information and date of birth, before returning the victim to the LiveChat window with a fake refund confirmation.
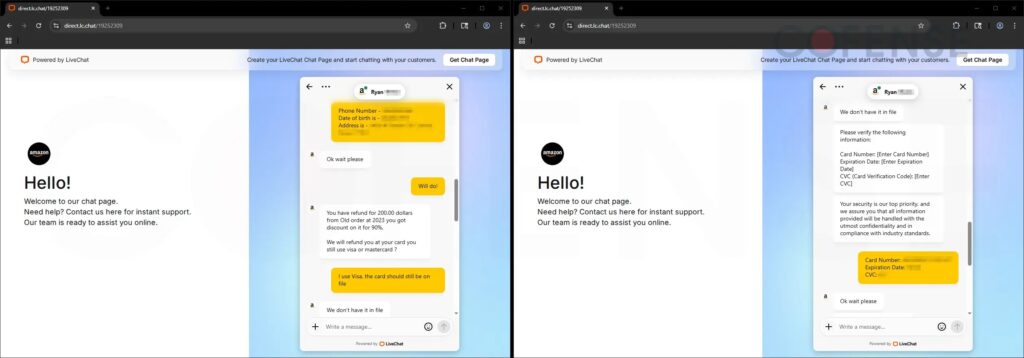
The Amazon-themed version uses a slightly different flow. Cofense says the page first requests the user’s email address before a supposed live agent appears. From there, the attacker asks for identity details such as a phone number, date of birth, home address, and then full payment card data, including the card number, expiration date, and CVC.
Cofense notes that the attacker language in at least one chat included misspellings and awkward phrasing, which suggests a human operator working from a script rather than a polished automated chatbot. That roughness did not stop the scam from progressing through multiple data collection stages.
Why this tactic is more dangerous than it looks
The biggest advantage for the attackers is trust transfer. Because the links use a legitimate SaaS support environment, the domain and interface may feel safer than a typical phishing page on a random site. That can make victims less cautious, especially when the lure involves a refund or a suspicious order they want to resolve quickly.
The tactic also helps phishers collect more than one kind of data in one session. Instead of grabbing only credentials, they can move from identity details to card data to MFA codes in a single guided conversation. That gives them a fuller victim profile and increases the chance of account takeover or payment fraud. This is an inference from Cofense’s documented multi-stage collection flow.
Key details at a glance
| Item | Detail |
|---|---|
| Platform abused | LiveChat |
| Hosted domain used in lure flow | lc.chat |
| Main lure themes | Refund notice, order confirmation |
| Brands impersonated | PayPal, Amazon |
| Data targeted | Credentials, MFA codes, personal details, payment card data |
| Collection method | Live chat interaction plus fake login and billing forms |
The details in this table come from Cofense’s March 2026 analysis.
What users and security teams should watch for
- Be suspicious of unsolicited refund or order-confirmation emails that push you into chat instead of the brand’s official website or app.
- Never share MFA codes, full card details, or date of birth inside a support chat opened from an email link. This advice follows directly from the collection steps Cofense observed.
- Verify transactions by going to the official PayPal, Amazon, or merchant site yourself rather than clicking through an email.
- Monitor for traffic to suspicious
lc.chatURLs and review email security controls for SaaS-hosted phishing links. This recommendation is based on the use of LiveChat-hosted infrastructure in the campaign.
FAQ
It uses a legitimate live support platform to make the phishing flow feel like a real customer service conversation instead of a standard fake login trap.
Cofense documented PayPal-themed and Amazon-themed phishing pages in the campaign.
The campaign targeted email addresses, phone numbers, dates of birth, home addresses, account credentials, MFA codes, and full payment card details.
lc.chat domain matter? Because it belongs to LiveChat infrastructure, which can make phishing links look more legitimate to victims and sometimes less suspicious to basic filters. This is an inference from Cofense’s description of the tactic.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages