Qilin ransomware uses malicious DLL to disable EDR before encryption

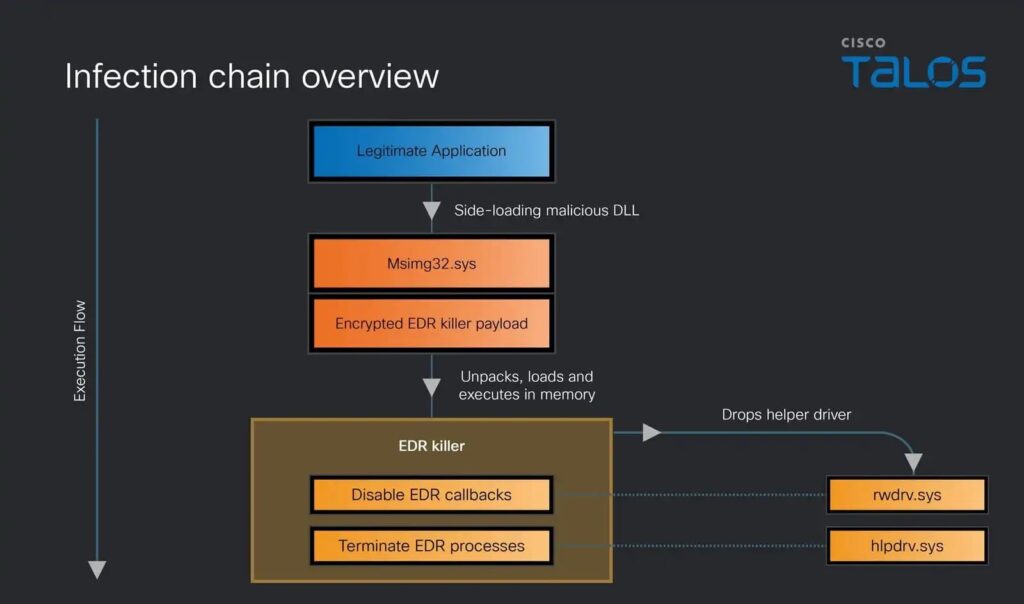
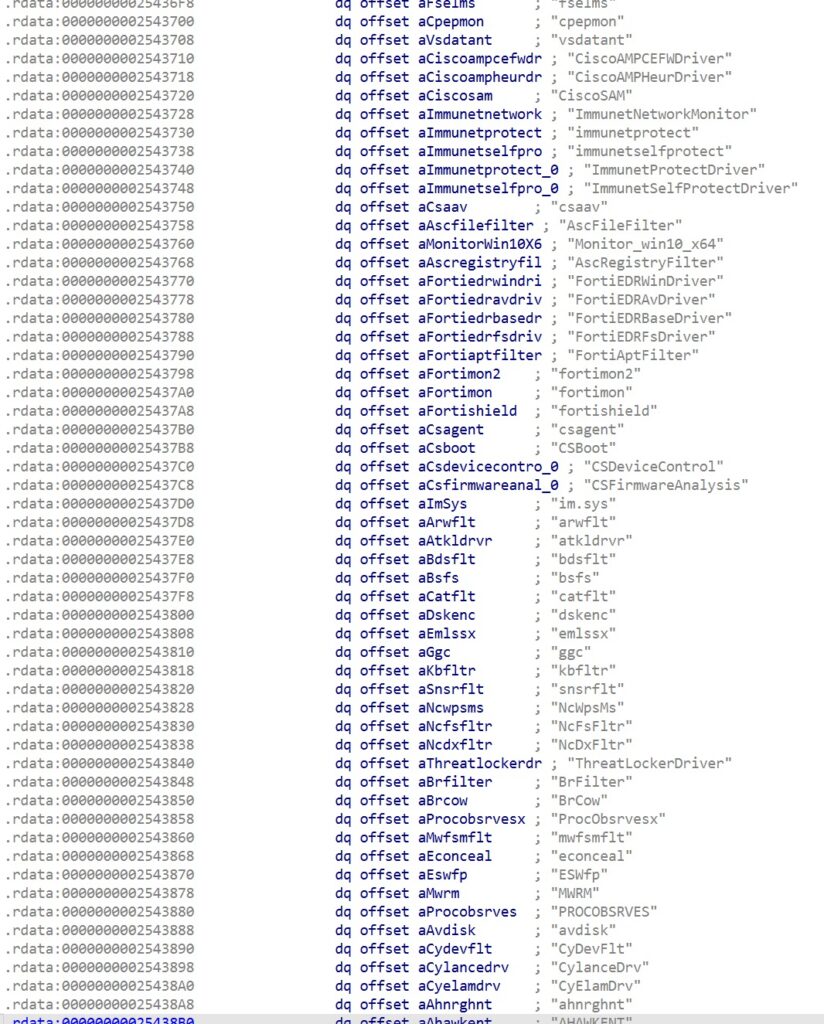
Qilin ransomware operators are using a malicious DLL called msimg32.dll to launch a multi-stage attack that disables endpoint detection and response tools before the ransomware stage begins. Cisco Talos said the infection chain can terminate or impair more than 300 EDR drivers across a wide range of vendors.
This matters because EDR products sit at the center of modern Windows defense. If attackers can blind those tools early, they get a much cleaner path to move, execute payloads, and prepare encryption without triggering the same level of telemetry defenders expect. Talos said the malware uses several evasion methods, including SEH and VEH-based obfuscation, kernel object manipulation, and API and system call bypass techniques.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Talos observed the malicious DLL in Qilin attacks and described it as the first stage of a sophisticated infection chain built to disable local EDR protections on compromised systems. The researchers said the loader decrypts and runs an embedded payload fully in memory, which helps the malware avoid detection on disk.
How the attack chain starts
The attack starts with a trojanized msimg32.dll that gets loaded by a legitimate application which imports functions from the real Windows library. To avoid breaking normal behavior, the malicious DLL forwards expected API calls to the legitimate msimg32.dll in C:\Windows\System32 while still running its own code from DllMain.
Talos said the first three stages act as a custom PE loader. They prepare the execution environment, unpack the later stages, and load the final EDR-killer component directly into memory. The researchers also said the malware suppresses Event Tracing for Windows at runtime and works to evade user-mode hooks before the final payload launches.
The loader also includes anti-debugging and geo-fencing checks. Talos said it looks for breakpoints on KiUserExceptionDispatcher and crashes the process if it finds one, and it exits on systems configured for languages commonly used in post-Soviet countries.
What the EDR killer does next
Once active, the payload loads two helper drivers. Talos said rwdrv.sys gives the malware access to physical memory, while hlpdrv.sys helps terminate EDR processes after the malware unregisters monitoring callbacks that would otherwise interfere.
Talos identified rwdrv.sys as a renamed version of ThrottleStop.sys, a legitimately signed driver originally distributed by TechPowerUp and used by tools such as GPU-Z and ThrottleStop. The researchers said the driver exposes powerful low-level hardware access functions without meaningful security checks, which makes it attractive for abuse.
The final stage uses hlpdrv.sys to terminate protected EDR processes through a driver IOCTL. Talos also said the malware temporarily overwrites the CiValidateImageHeader callback with a function that always returns true, then restores the original callback later to reduce traces and re-enable the normal code integrity check.
Why Qilin keeps drawing attention
Qilin, also known as Agenda, has become one of the most active ransomware operations in recent years. Cisco Talos said the group posted more than 40 victims per month in 2025 except for January, with peaks that showed a sustained pace of operations.
MITRE ATT&CK tracks Water Galura as the operators of the Qilin ransomware-as-a-service operation and says they have been active since at least 2022. MITRE also links Water Galura directly to the Qilin ransomware family in its threat group and software entries.
This latest Talos research shows that Qilin does not rely only on classic ransomware execution. It invests in defense evasion first, then uses that advantage to make later stages more effective. That pattern matches the broader ransomware trend Cisco described in its recent reporting, where attackers blend in, disable protections, and use legitimate components to stay hidden longer.
Key technical details
| Item | Verified detail |
|---|---|
| Initial malware component | Malicious msimg32.dll |
| Primary goal | Disable local EDR protections before later stages |
| Scale of impact | Can disable over 300 EDR drivers |
| Stage 4 helper drivers | rwdrv.sys and hlpdrv.sys |
| Driver abuse | rwdrv.sys is a renamed ThrottleStop.sys signed by TechPowerUp |
| Evasion methods | SEH/VEH obfuscation, ETW suppression, API and syscall bypass methods |
| Anti-analysis behavior | Breakpoint checks and geo-fencing for post-Soviet locales |
| Code integrity trick | Temporarily overwrites CiValidateImageHeader callback, then restores it |
What defenders should watch for
- Suspicious DLL sideloading involving msimg32.dll.
- Unexpected loading of rwdrv.sys or hlpdrv.sys.
- Attempts by user-mode processes to access physical memory through unusual driver activity.
- Sudden loss of EDR telemetry or protected process termination.
- ETW suppression or signs of hook bypass behavior in ntdll-related execution flow.
- Administrative execution paired with stealthy, memory-only payload loading.
FAQ
The malware does not rush straight to encryption. Cisco Talos said it begins with a malicious DLL that prepares the system, evades detection, and disables EDR protections before the ransomware stage becomes visible.
Talos said the EDR killer can disable over 300 different EDR drivers from almost every vendor in the market. That claim comes directly from the researchers’ technical write-up.
They give the malware deeper system access than normal user-mode code would have. Talos said rwdrv.sys exposes physical memory access, while hlpdrv.sys helps terminate protected EDR processes after the malware removes monitoring callbacks.
No. Cisco Talos and MITRE both describe Qilin as a significant ransomware operation. Talos said the group kept a pace of more than 40 posted victims per month through most of 2025, and MITRE tracks the operators as Water Galura in a ransomware-as-a-service model.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages