Ransomware gangs now use more EDR killers that do not rely on vulnerable drivers, ESET says

Ransomware groups are using a wider range of tools to shut down security products before they launch encryption, and ESET says the trend now goes well beyond the familiar Bring Your Own Vulnerable Driver, or BYOVD, technique. In a new deep dive published in March 2026, ESET said affiliates increasingly mix vulnerable drivers with scripts, anti-rootkit tools, and newer driverless methods that can block or freeze endpoint defenses.
That matters because attackers do not need to make ransomware itself stealthier if they can simply blind the EDR first. ESET says affiliates prefer a short, reliable window to run an encryptor rather than constantly rewriting payloads to dodge detection.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
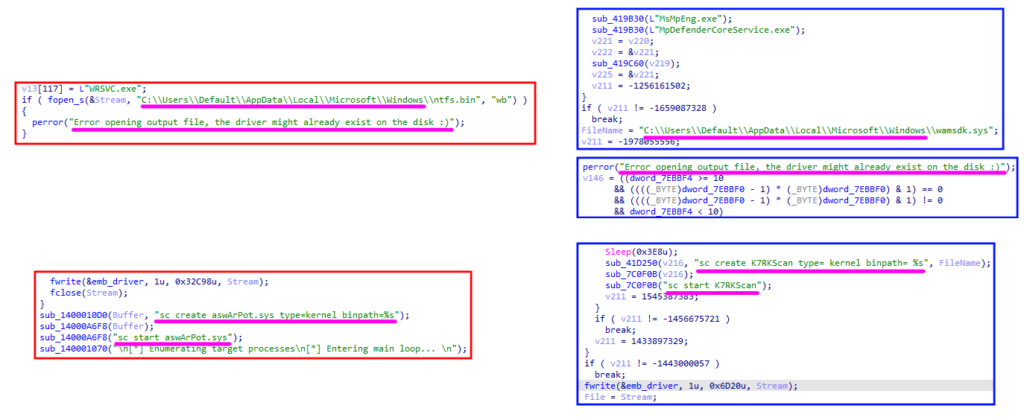
The report shows how broad the ecosystem has become. ESET says it tracks almost 90 EDR killers used in real attacks, including 54 BYOVD-based tools abusing 35 vulnerable drivers, seven script-based tools, and 15 anti-rootkits or other freely available programs.
Why attackers keep using them
ESET says EDR killers have become a predictable stage in modern ransomware operations because they work. Instead of taking risks with a noisy encryptor that may trigger alerts, affiliates can first disable or weaken the security stack and then run the final payload with much better odds of success.
The company also says affiliates, not the core ransomware operators, usually choose the EDR killer used in a breach. That creates far more variety in the wild, because different affiliates bring their own tools, code forks, and preferred methods into the same ransomware ecosystem.
This is one reason attribution gets messy. ESET says the same vulnerable driver can appear across unrelated tools, while the same tool can switch to different drivers over time, which makes driver-only attribution unreliable.
The shift beyond BYOVD
BYOVD still dominates, but ESET says defenders should stop treating it as the whole story. Some lower-skill attackers use simple scripts to kill services or boot systems into Safe Mode, while others abuse legitimate anti-rootkit utilities that already have the privileges needed to tamper with security tools.
ESET also highlights a growing class of driverless EDR killers. These tools do not need to load a vulnerable kernel driver at all. Instead, they may block communication between the endpoint agent and its backend or freeze the EDR process in place, which can make them harder to catch with defenses focused only on driver abuse.
The researchers say this broader landscape makes defense harder because attackers can quickly swap tactics when one path fails. If a vulnerable driver gets blocked, they can try another tool or switch to a script or driverless option.
ESET’s numbers and key findings
| Finding | ESET’s reported figure |
|---|---|
| EDR killers tracked in the wild | Almost 90 |
| BYOVD-based tools | 54 |
| Vulnerable drivers abused | 35 |
| Script-based tools | 7 |
| Anti-rootkits or other freely available tools | 15 |
The numbers above come from ESET’s March 2026 research into the EDR killer ecosystem.
Some of the examples in the report show why driver-based tracking can mislead analysts. ESET says the Baidu Antivirus driver BdApiUtil.sys appears in several independent projects, while the TfSysMon.sys driver shows up in distinct codebases such as TfSysMon-Killer, Susanoo, and EDRKillShifter.
In other words, seeing a known driver in one intrusion does not automatically point to one ransomware gang. ESET says unrelated tools can share the same driver, and a single actor can move across multiple drivers as the market evolves.
Commercialization is making the problem worse
ESET says the market for these tools has matured fast. The company points to commercial EDR killers sold on dark web forums, packer services, and hardened offerings that lower the barrier to entry for ransomware affiliates.

That commercial layer matters because it reduces development costs and spreads working techniques faster. A less skilled affiliate no longer needs deep kernel expertise if it can buy or adapt a product that already knows how to interfere with popular security software.
ESET also says some code it observed in tools used by the Warlock gang shows signs that suggest AI-assisted development. The researchers stress that direct proof is difficult, but they say one sample included traits that strongly suggest AI-generated boilerplate and trial-and-error logic.
What defenders should focus on now
- Do not rely only on blocking vulnerable drivers. ESET says that step often comes very late in the intrusion chain.
- Watch for behavior that suggests security tampering, such as service termination attempts, Safe Mode abuse, driver installation, and EDR communication disruption.
- Strengthen layered controls like application control, anti-tamper features, patching, and threat intelligence support.
- Treat EDR-killer activity as an immediate sign that ransomware may follow within minutes. ESET says attackers often deploy these tools right before the encryptor.
ESET’s main warning is simple: if defenders focus only on the driver, they may miss the broader playbook. The company says organizations need a prevention-first strategy that stops EDR killers before execution, not just at the final point where a malicious or abused driver tries to load.
FAQ
It is a tool or malware component that disables, freezes, or disrupts endpoint detection and response software so attackers can continue an intrusion without being stopped.
ESET says encryptors are noisy and easy to spot, so affiliates often prefer to blind security tools first and then launch ransomware with a better chance of success.
BYOVD stands for Bring Your Own Vulnerable Driver. Attackers load a legitimately signed but flawed driver to gain kernel-level access and tamper with system protections.
They remain a major problem, but ESET says attackers now also use scripts, legitimate anti-rootkits, and driverless techniques, so driver-focused detection alone is no longer enough.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages