RedAlert mobile espionage campaign targets civilians with a trojanized rocket alert app
Attackers have spread a fake Android emergency alert app through SMS messages that impersonate Israel’s Home Front Command, according to CloudSEK. The malicious APK presents a working “red alert” style interface, but it also collects sensitive data like SMS messages, contacts, and precise location, then sends it to attacker infrastructure.
This campaign relies on one simple trick: it pushes victims to install an APK outside Google Play. The official Home Front Command app is distributed through Google Play, and Israel’s official Home Front Command website directs users to download the app from official sources. If a message asks you to “update” by installing an APK file, treat it as hostile.
CloudSEK says the malware uses staged payload loading and evasion tactics to hide what it is doing. That matters because the app can look legitimate while it runs surveillance in the background.
What CloudSEK says the malware does
CloudSEK reports that the trojanized app requests high-risk permissions and activates collection modules once the user grants them. It says the malware steals SMS content, contacts, and GPS location, then transmits the data to an attacker-controlled endpoint.
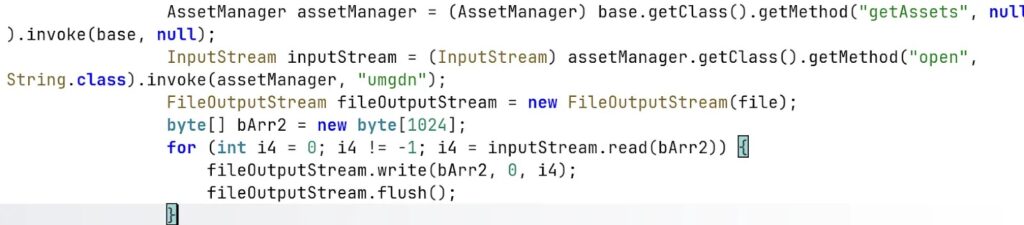
CloudSEK also describes a multi-stage execution flow that includes dynamic loading of additional code from the APK assets, which can reduce the effectiveness of basic static scanning.
Key details at a glance
| Item | Details |
|---|---|
| Campaign name used by researchers | RedAlert |
| Target platform | Android |
| Delivery method | SMS phishing (smishing) that impersonates Home Front Command |
| Main trick | Forces sideloading outside Google Play |
| Data at risk | SMS, contacts, location (per CloudSEK) |
| Reported exfil domain | api.ra-backup.com (per CloudSEK) |
How the infection chain works
CloudSEK’s analysis describes a staged approach:
- Stage 1: A convincing app shell that looks like a real alert app and attempts to mask its origin.
- Stage 2: Extraction and in-memory loading of hidden content from the APK assets.
- Stage 3: Activation of spyware modules and command-and-control communication.
CloudSEK says the app aims to look like a normal emergency alert utility while it silently pulls sensitive device data.
Why this matters in a conflict zone
Emergency alert apps run on devices people carry everywhere. That makes them valuable surveillance targets because location and SMS access can reveal movement patterns and account recovery codes.
This also shows why sideloading bans exist in many organizations. A single “urgent update” message can bypass normal caution when people feel pressure to act quickly.
What individuals should do right now
- Do not install “updates” from SMS links, especially APK downloads.
- Download the official Home Front Command app only through official channels.
- If you already installed a suspicious APK, disconnect the phone from the network, remove the app, then consider a factory reset if you cannot confirm device integrity. CloudSEK explicitly recommends factory reset and avoiding restoring backups created after infection.
- Re-check app permissions. Treat any alert app that requests SMS, contacts, and precise location as suspicious unless you can validate its publisher.
What security teams should do
- Block outbound DNS and HTTPS access to the reported exfil domain and related indicators from mobile networks where possible.
- Enforce MDM policies that disable “Install unknown apps” and prevent sideloading on managed devices.
- Alert on apps that request high-risk permission combinations such as:
- READ_SMS or RECEIVE_SMS
- READ_CONTACTS
- ACCESS_FINE_LOCATION
- Publish an internal advisory that warns staff about conflict-themed smishing and urges manual verification through official sources.
Detection checklist
| Signal | What to look for |
|---|---|
| Installation source | App installed from outside Google Play |
| Permissions | SMS + contacts + precise location requested together |
| Network | HTTPS posts to unusual domains, including api.ra-backup.com |
| User reports | “Home Front Command update” SMS with a download link |
FAQ
CloudSEK says it is an Android espionage campaign that spreads a fake emergency alert app via SMS spoofing that impersonates Israel’s Home Front Command.
Yes. The Home Front Command publishes an official Android app on Google Play.
Do not sideload APKs from SMS links. Use official app store listings and official government guidance pages to download emergency apps.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages