RMM tools keep IT running, but attackers now use them as stealthy entry points
Remote Monitoring and Management tools remain essential for modern IT teams. They help administrators patch systems, troubleshoot endpoints, and support distributed workforces from anywhere. But the same remote access, automation, and visibility that make RMM platforms useful now make them attractive to attackers who want quiet, trusted access inside a target network.
Huntress says abuse of RMM tools jumped 277% year over year in 2025, making the trend too large for defenders to treat as a niche problem. The company says RMM abuse accounted for 24% of all observed incidents in its 2026 Cyber Threat Report, a sign that attackers increasingly prefer legitimate admin tools over noisier malware or commodity remote access implants.
That shift changes the defender’s problem. A malicious PowerShell script or a known trojan often leaves obvious clues. A trusted RMM binary does not. Huntress says attackers increasingly use legitimate, pre-installed remote management software for hands-on-keyboard access because it blends into ordinary IT activity and often slips past security controls designed to catch clearly malicious tools.
Why RMM abuse keeps growing
Attackers do not need to build custom remote access infrastructure when ready-made tools already offer persistence, remote control, command execution, file transfer, and lateral movement. Huntress says this “use what is already trusted” approach has helped drive a drop in older attack methods, with use of traditional hacking tools down 53%, remote access trojans down 20%, and malicious scripts down 11.7% in the same reporting period.
RMM abuse also fits broader living-off-the-land tactics. Huntress says attackers increasingly hide behind signed, legitimate software instead of dropping binaries that antivirus tools may catch quickly. In its ransomware trends guidance, the company specifically names RMM tools alongside PowerShell and WMI as examples of trusted administration components that attackers can weaponize to avoid standing out.
How intrusions usually start
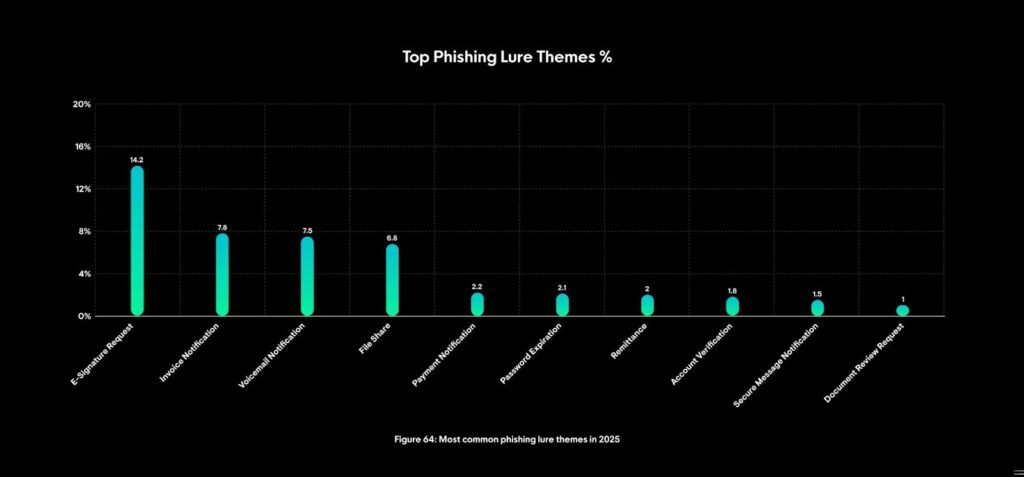
In many cases, the entry point is still human behavior. Huntress says users often get phished or socially engineered into installing a rogue RMM agent through lures such as e-signature requests, invoice notifications, voicemail notices, or file-share messages. Once the agent installs, the attacker can gain immediate interactive access to the machine.
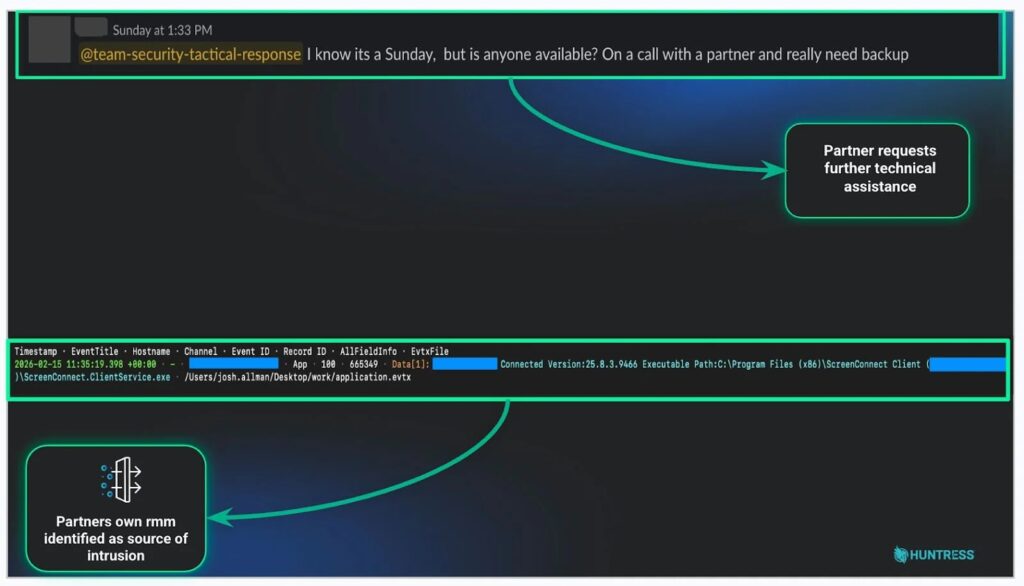
Huntress also says RMM abuse does not always begin with a fake installer. In some cases, attackers use stolen credentials for an already approved RMM platform. That gives them access through a tool the victim organization already trusts, which can turn a normal administrative channel into a fast-moving intrusion path.
Why defenders miss it
The main challenge is over-trust. Many teams see ScreenConnect, Atera, RustDesk, or another approved tool in the environment and assume activity through it must be legitimate. Huntress argues that this mindset no longer works. An approved tool may still be part of an attack if the session appears at the wrong time, from the wrong account, or in ways that do not fit the normal baseline.
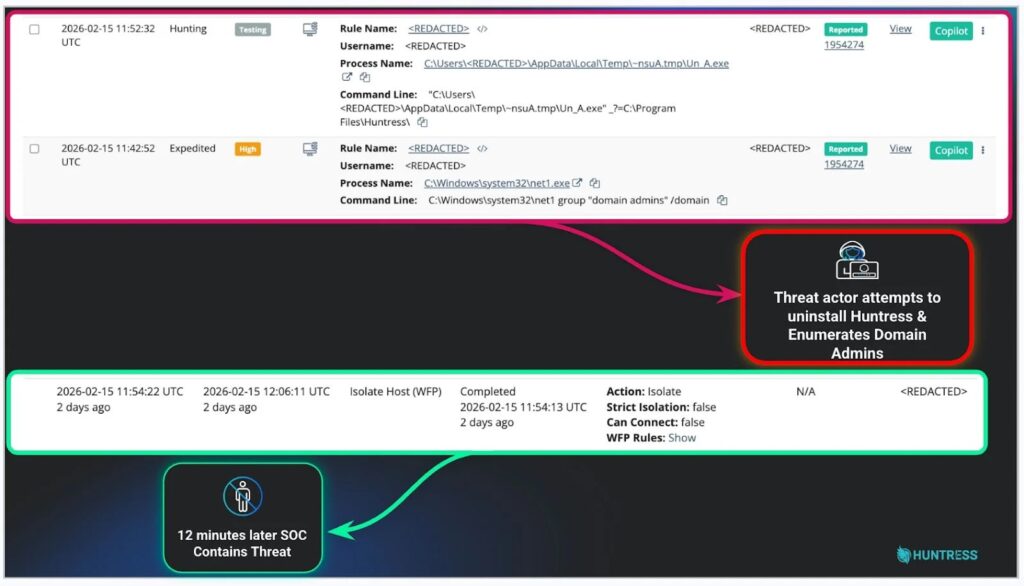
This problem becomes more serious in managed service provider environments. Huntress described one case where a threat actor used stolen RMM credentials to access a partner environment, run enumeration commands, and attempt to disable the Huntress agent. The company says the intrusion was contained about 12 minutes after the first command ran, but the same access could have exposed every customer managed by that MSP.
Ransomware risk rises fast
The ransomware angle makes RMM abuse especially dangerous. Huntress says more than 50% of cases following suspicious Atera RMM activity were directly linked to ransomware attacks. In the same guidance, Huntress says abuse of tools such as RustDesk or Atera can lead to ransomware damage in as little as an hour or two.
That speed matters because the attacker no longer needs to waste time building persistence from scratch. Once inside an RMM session, they can run commands, move laterally, disable protections, stage tools, and push later payloads while appearing to be legitimate support staff. The gap between first access and serious operational impact can shrink quickly.
RMM abuse at a glance
| Metric | Verified detail |
|---|---|
| Year-over-year rise in RMM abuse | 277% in 2025, according to Huntress |
| Share of observed incidents | 24% of incidents in Huntress reporting |
| Ransomware link | Over 50% of cases following suspicious Atera activity tied to ransomware |
| Common entry methods | Phishing and social engineering, including e-signature, invoice, voicemail, and file-share lures |
| MSP risk | One compromised RMM account can expose downstream customer environments |
What security teams should do
The practical fix is not to ban every RMM platform. Most organizations need them. The better approach is to move from trusting tool presence to verifying behavior. Huntress recommends defining a normal baseline for who uses each tool, at what times, from which systems, and to which destinations. An approved product should still trigger scrutiny when usage falls outside that pattern.
Security teams should also keep a detailed inventory of approved RMM tools, including executable hashes and expected servers or connection endpoints. Huntress says that kind of fingerprinting helps defenders spot rogue installs, modified binaries, or authorized tools connecting to unexpected infrastructure.
Awareness training still matters because many rogue RMM installs begin with user action. Huntress says employees and IT staff need to recognize that a routine-looking email or support message may actually be the start of remote access for an attacker. Fast reporting can shrink the time between infection and containment.
FAQ
It is the malicious use of legitimate remote monitoring and management software to gain remote access, persist inside networks, and carry out follow-on actions such as credential theft, lateral movement, or ransomware deployment.
Because the software is legitimate, trusted, and already designed for remote administration. That helps attackers blend into normal activity and avoid tools focused on clearly malicious binaries.
Huntress says more than half of cases following suspicious Atera activity were linked to ransomware, which shows how often remote admin abuse becomes a precursor to bigger attacks.
Yes. Huntress says a compromised MSP RMM account can create a one-to-many problem because one trusted admin channel may reach many customer environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages