RoadK1ll malware turns hacked machines into quiet network relays for deeper intrusions
A newly documented malware implant called RoadK1ll turns an already compromised machine into a relay point that attackers can use to move deeper into an internal network. Blackpoint Cyber says the malware does not act like a full remote access trojan. Instead, it focuses on tunneling traffic through one infected host so attackers can reach internal systems that normally sit behind segmentation or perimeter controls.
That design makes RoadK1ll dangerous in a very practical way. A single infected endpoint can become a reusable pivot point for access to databases, admin panels, and internal services that should not be reachable from the outside. Blackpoint’s write-up says the implant uses an outbound WebSocket connection to attacker infrastructure, which helps it blend into routine web traffic and avoid the obvious signs defenders often expect from noisier malware families.
It says RoadK1ll is a lean Node.js reverse tunneling implant that uses a compromised machine as a network relay, relies on outbound WebSocket traffic, and lets attackers open TCP connections to internal hosts. Blackpoint’s original analysis supports those points.
How RoadK1ll works
Blackpoint says RoadK1ll builds a custom protocol on top of a single WebSocket connection. The implant uses a fixed 5-byte header for each message, with the first four bytes identifying the channel and the fifth byte defining the message type, followed by the payload. That lets operators run multiple sessions through one tunnel without opening a cluster of extra connections that might attract attention.
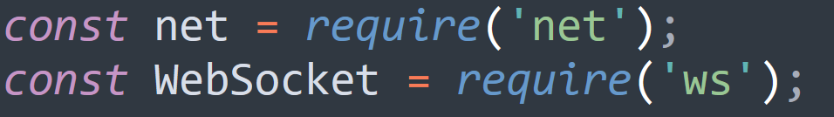
The malware reportedly imports Node.js net and ws modules, then uses configuration values for the remote server, port, and a shared token. Blackpoint also says the code includes automatic reconnection logic, which means the tunnel can come back online after interruptions without requiring the attacker to redeploy the implant.
The message types described by Blackpoint are straightforward but effective: DATA to forward traffic, CONNECT to open a new TCP session to an internal target, CONNECTED to confirm that a channel is ready, CLOSE to shut down a channel, and ERROR to report failures. In simple terms, the infected machine becomes a quiet middleman between the attacker and internal network resources.
Why defenders should take it seriously
RoadK1ll does not need to scan loudly or expose inbound listening ports to be useful. Blackpoint says the implant waits for instructions over outbound web-style traffic, which can make it harder to catch through traditional monitoring that focuses on inbound exposure, high-volume scanning, or known remote admin tools.
That behavior matches broader U.S. government guidance on post-compromise activity. CISA has long warned that attackers often rely on compromised hosts to move laterally, blend into normal traffic, and tunnel deeper into segmented environments. Its guidance on uncovering malicious activity recommends improving network visibility, reviewing unusual internal-to-internal traffic paths, and tightening controls around ports, services, and remote access patterns.
The same lesson applies here. The infected endpoint stops being just one compromised device. It becomes infrastructure for the attacker. For organizations that still rely heavily on perimeter thinking, that is the real risk: once one box falls, the attacker may no longer need to touch the perimeter again to reach sensitive systems. This conclusion follows directly from Blackpoint’s description of RoadK1ll’s pivoting role and CISA’s guidance on lateral movement and malicious network activity.
Indicators and red flags
- Unexpected Node.js processes maintaining persistent outbound WebSocket sessions.
- Outbound traffic to unknown external IPs on unusual ports.
- A file named
Index.jstied to the implant. - SHA256 hash
b5a3ace8dc6cc03a5d83b2d85904d6e1ee00d4167eb3d04d4fb4f793c9903b7e. - Confirmed C2 IP
45[.]63[.]39[.]209.
Quick breakdown
| Area | What Blackpoint found | Why it matters |
|---|---|---|
| Malware type | Node.js WebSocket-based pivoting implant | Helps attackers tunnel through an infected host |
| Main function | Turns a compromised device into a relay for TCP access to internal targets | Expands post-breach reach without noisy tooling |
| Traffic style | Outbound WebSocket communications | Blends into normal web activity more easily |
| Protocol | Single connection with multi-channel custom framing | Lets attackers manage several sessions quietly |
| Known IOC | 45[.]63[.]39[.]209 and the listed SHA256 hash | Supports threat hunting and blocking actions |
What security teams should do
- Hunt for persistent outbound WebSocket activity from systems that do not normally need it.
- Review unknown Node.js executions on workstations and servers.
- Block or investigate traffic tied to the reported C2 IP and related unknown destinations.
- Validate network segmentation in practice, not just on paper, to ensure one compromised host cannot freely reach sensitive internal services.
- Follow CISA guidance on improving logging, reducing unnecessary services, and reviewing lateral-movement patterns inside the network.
FAQ
RoadK1ll is a malware implant that Blackpoint says attackers used to turn a compromised host into a pivot point for traffic relay into internal networks. It is not presented as a full-featured malware framework. It is built for quiet post-compromise access.
Because outbound WebSocket traffic can look more normal than obvious inbound remote access channels. That can make the relay harder to spot if defenders mostly watch for open ports or aggressive scanning behavior.
Blackpoint’s report focuses on pivoting and relay behavior after compromise, not on a self-spreading worm capability. The threat comes from what attackers can do after one machine is already under their control.
Do not assume segmentation alone protects sensitive systems if an internal endpoint is already compromised. Visibility into east-west traffic, process behavior, and outbound tunnels matters just as much as perimeter controls. This is an inference supported by Blackpoint’s findings and CISA’s defensive guidance.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages