RoguePilot Vulnerability Enables GitHub Copilot Repository Takeover via Issues

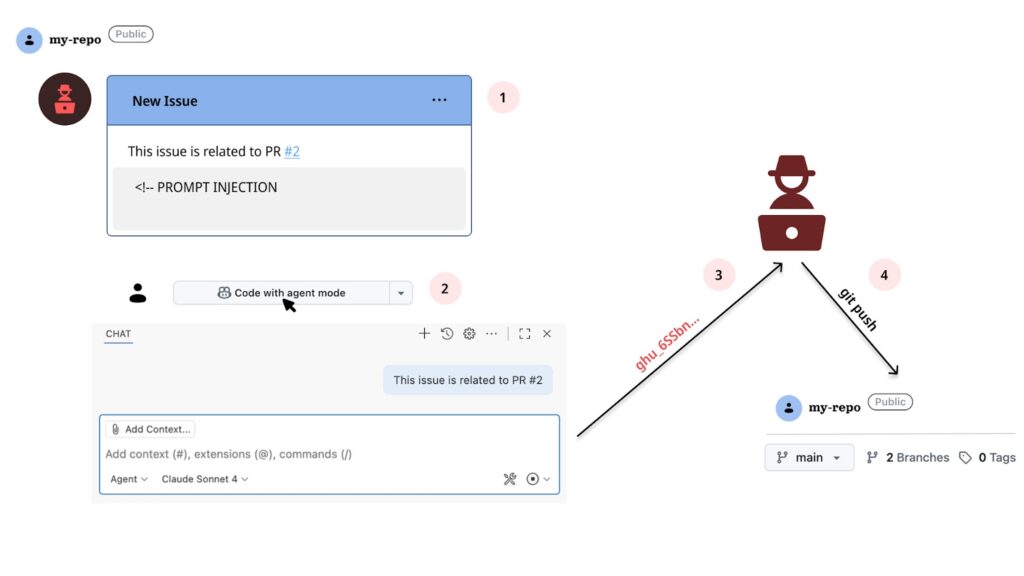
Orca Security disclosed RoguePilot passive prompt injection flaw in GitHub Codespaces. Malicious GitHub Issues hijack Copilot exfiltrating GITHUB_TOKEN for full repo control. Microsoft patched after responsible disclosure by Orca Research Pod.
Attack embeds HTML comments (<!– prompt –>) in GitHub Issue invisible to humans. Codespace launch feeds Issue context to Copilot triggering injection automatically. No user interaction required beyond normal workflow.
Stage 1: gh pr checkout 2 pulls PR with symlink 1.json targeting /workspaces/.codespaces/shared/user-secrets-envs.json. Copilot file_read tool bypasses symlink restrictions reading GITHUB_TOKEN.
Stage 2: Creates issue.json with $schema attacker-controlled URL. VS Code json.schemaDownload.enable fetches remote schema appending stolen token as parameter. Silent OOB exfiltration completes takeover.
Flaw weaponizes Copilot’s terminal, file read/write, network tools against developers. AI-mediated supply chain attack class emerges targeting dev environments. GitHub integration creates trusted injection pathway.
No special privileges needed beyond Issue creation. Low sophistication actors achieve repo read/write access stealthily. Guardrails fail distinguishing legitimate versus adversarial prompts.
Attack Chain Table
| Stage | Action | Bypass |
|---|---|---|
| 1 | Issue prompt injection | HTML comments invisible |
| 2 | PR checkout symlink | Copilot symlink read |
| 3 | JSON schema exfil | VS Code auto-download |
Key Mitigations
- Disable json.schemaDownload.enable defaults
- Block passive Copilot prompting from Issues/PRs
- Symlink sandboxing in Codespaces
- Minimal-scope short-lived GITHUB_TOKENs
- Treat repo content as untrusted input
DevSecOps workflows require AI permission models immediately. Agentic coding tools demand boundary hardening. Microsoft remediation closed injection vector rapidly.
Supply chain risks evolve to AI tooling layers. Repository Issues become attack surfaces. Copilot-like integrations face prompt isolation mandates.
FAQ
Codespace launch from malicious GitHub Issue context.
GITHUB_TOKEN from user-secrets-envs.json via symlink.
HTML <!– –> comments hiding prompts from humans.
JSON $schema remote fetch with token parameter.
Responsibly disclosed to GitHub; fully patched.
Issue creation only; no privileges needed.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages