Russian APT exploits Zimbra flaw to spy on Ukrainian agency in stealthy “Operation GhostMail”

A Russia-linked cyberespionage campaign has exploited a Zimbra webmail flaw to target a Ukrainian government agency in a stealthy phishing operation that relied on no attachments, no links, and no macros. Researchers at Seqrite say the campaign, dubbed “Operation GhostMail,” abused CVE-2025-66376, a stored cross-site scripting bug in Zimbra’s Classic UI, to steal credentials, mailbox data, and other sensitive information from a live browser session.
The short answer for defenders is clear. If an organization still runs vulnerable Zimbra builds, it needs to patch immediately and audit for signs of account abuse. Zimbra says CVE-2025-66376 was fixed in ZCS 10.0.18 and 10.1.13, while CISA added the flaw to its Known Exploited Vulnerabilities catalog on March 18, 2026, with an April 1, 2026 remediation deadline for federal agencies.
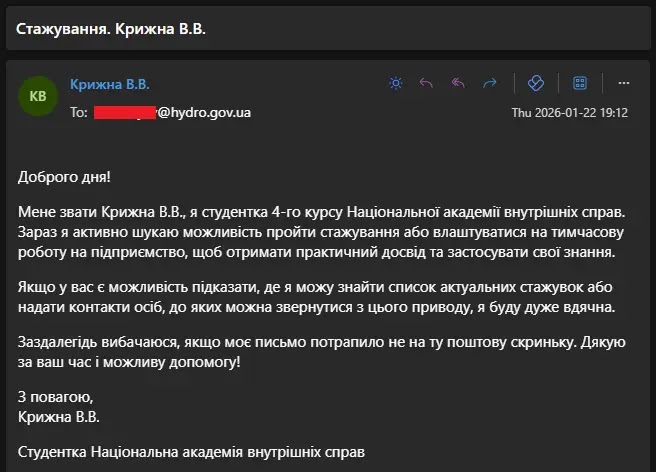
According to Seqrite, the phishing email hit the Ukrainian State Hydrology Agency on January 22, 2026. The message posed as an internship inquiry written in Ukrainian and carried its malicious payload inside the HTML body. The user-provided sample describes the same campaign details, including the target, delivery method, and two-stage browser-based payload.
What happened in Operation GhostMail
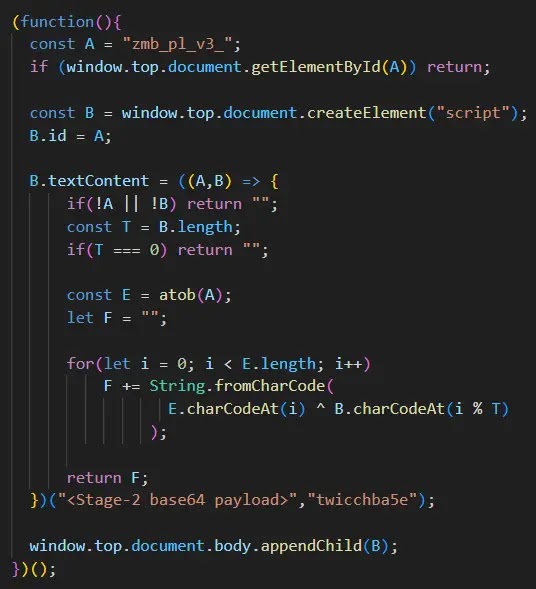
Seqrite says the attack exploited Zimbra’s Classic UI by abusing insufficient sanitization of CSS @import directives in HTML email content. When the target opened the email while already authenticated to a vulnerable Zimbra session, the JavaScript payload executed in the browser and escaped the email frame to gain broader access to session data and same-origin resources.
The campaign stood out because it avoided the usual phishing artifacts. Researchers said there were no malware-laced attachments and no suspicious external links, which likely reduced the chance of detection by both users and conventional email filters. That core point also appears in the user-provided sample article.
Seqrite attributed the operation to APT28 with medium confidence. The company based that assessment on technical overlaps with earlier Zimbra-focused activity and the geopolitical profile of the target. MITRE identifies APT28 as a Russia-linked threat group attributed to the GRU’s 85th Main Special Service Center.
Why this Zimbra flaw is dangerous
Zimbra’s own security materials describe CVE-2025-66376 as a stored XSS vulnerability in the Classic UI. The flaw allows abuse of CSS @import directives inside HTML email, which creates a dangerous path for attackers because webmail users often trust normal-looking messages.
CISA’s KEV listing changes the urgency level. When CISA adds a bug to KEV, it signals that attackers are already exploiting it in real-world operations. In this case, that public warning arrived just before researchers published details of GhostMail, which strengthens the case for rapid patching and review of older Zimbra deployments.
Reported attack flow
| Stage | What researchers say happened | Why it matters |
|---|---|---|
| Delivery | Phishing email posed as a harmless internship request | Social engineering kept suspicion low |
| Initial execution | Hidden JavaScript payload ran in vulnerable Zimbra Classic UI | No attachment or link was needed |
| Browser escape | Script moved into the top-level document context | It gained access to cookies, storage, and SOAP API rights |
| Collection and exfiltration | Data moved out over HTTPS and DNS | Detection became harder |
Seqrite said the loader first checked whether a script was already running, then decoded a base64 payload and applied XOR decryption before injecting the final script into the top-level document. The user-provided sample includes the same two-stage structure and notes the use of a hardcoded command-and-control domain registered two days before the phishing email arrived.
What attackers reportedly stole
Researchers say the second-stage stealer harvested a wide range of data, including session tokens, login credentials, backup two-factor authentication codes, browser-saved passwords, and up to 90 days of email archives. Seqrite also said the attackers enabled IMAP and created an app-specific password called “ZimbraWeb,” which could preserve mailbox access even after a standard password reset.
That persistence detail matters. A password reset alone may not fully remove access if attackers also created alternate mailbox access paths during the session. The sample text the user shared highlights the same recommendation to audit for app-specific passwords named “ZimbraWeb” and to monitor SOAP API calls such as GetScratchCodesRequest and CreateAppSpecificPasswordRequest.
Affected and fixed versions
| Product branch | Vulnerable before | Fixed version |
|---|---|---|
| Zimbra 10.0 | 10.0.18 | 10.0.18 or later |
| Zimbra 10.1 | 10.1.13 | 10.1.13 or later |
Zimbra’s security pages say the Classic UI XSS flaw was patched in ZCS 10.0.18 and 10.1.13. GitHub’s advisory database reflects the same version boundaries for CVE-2025-66376.
What organizations should do now
- Patch Zimbra to 10.0.18 or 10.1.13 at minimum.
- Move off the Classic UI where possible.
- Review account activity for unexpected IMAP enablement.
- Search for app-specific passwords, especially one named “ZimbraWeb.”
- Inspect unusual SOAP API calls tied to scratch codes or app-password creation.
- Tighten DNS and HTTPS monitoring for suspicious outbound activity.
- Disable IMAP or POP3 for users who do not need it.
These recommendations line up with the vendor’s patch guidance, CISA’s KEV action, and the post-compromise behaviors described by Seqrite and in the user-provided sample.
Quick facts
| Item | Detail |
|---|---|
| Campaign name | Operation GhostMail |
| Attributed actor | APT28, with medium confidence from Seqrite |
| Target named by researchers | Ukrainian State Hydrology Agency |
| Exploited flaw | CVE-2025-66376 |
| Vulnerable component | Zimbra Classic UI |
| CISA status | Added to KEV on March 18, 2026 |
FAQ
It is a cyberespionage campaign described by Seqrite in which a Russia-linked actor used a Zimbra XSS flaw to compromise a Ukrainian government target through a malicious HTML email.
Yes. Zimbra says CVE-2025-66376 was patched in 10.0.18 and 10.1.13, but unpatched systems remained exposed.
Seqrite says it did not. The payload lived inside the email’s HTML body, which made the campaign harder to spot through common phishing checks.
CISA adds vulnerabilities to KEV when there is evidence of active exploitation. That listing means defenders should treat the issue as an immediate patching priority.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages