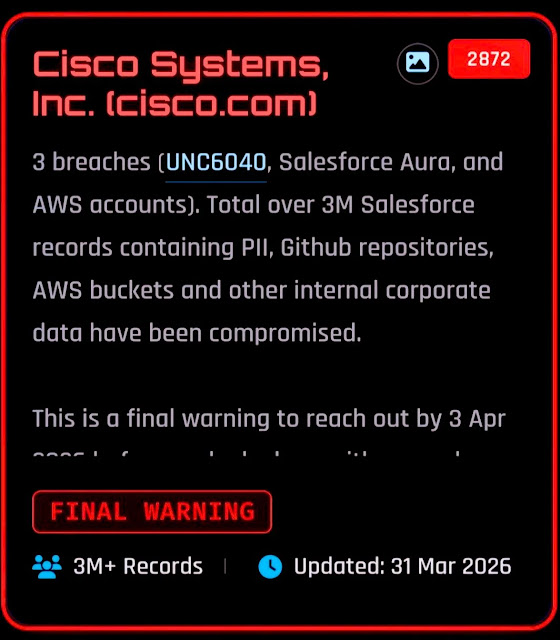
ShinyHunters claims Cisco breach with Salesforce, GitHub, and AWS data, but key details remain unverified

ShinyHunters has allegedly listed Cisco on its leak site and claims it stole more than 3 million Salesforce records along with GitHub repositories and AWS-related data. Multiple security researchers and cyber outlets reported the listing on April 1 and April 2, 2026, but Cisco had not published a public statement specifically addressing this new extortion claim when I checked.
That distinction matters. Right now, the most solid fact is that a public extortion claim exists and names Cisco. The larger claims about the exact volume of data, the number of breach paths, and the scope of exposed internal assets still need independent confirmation from Cisco or a formal incident disclosure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What gives the claim more context is the threat pattern around Salesforce over the past year. Google Threat Intelligence Group said attackers tied to UNC6040 used voice phishing and malicious connected apps to steal Salesforce data, and later extortion activity sometimes claimed affiliation with ShinyHunters to pressure victims.
Why this Cisco claim is getting attention
Cisco is not new to Salesforce-related incident response. In a Cisco advisory about a July 2025 vishing incident, the company said a bad actor targeted a Cisco representative, gained access to a third-party CRM system, and extracted basic profile information from Cisco customer records. Cisco said the incident affected contact and business data, not passwords, Social Security numbers, tax IDs, payment card data, or other sensitive identifiers.
That earlier disclosure does not prove the new ShinyHunters leak claim. It does show that Cisco already faced a real CRM compromise tied to voice phishing and cloud-based data access, which makes any new Salesforce-related extortion allegation more plausible than it would be in a vacuum.
There is also broader context around Cisco and exposed internal assets. In October 2024, Cisco acknowledged that files in a public-facing DevHub resource were unintentionally exposed because of a configuration issue, while saying there was no breach of its products or core systems. That older event is separate from the current claim, but it helps explain why any fresh allegation involving code, cloud storage, or internal repositories gets immediate scrutiny.
What the threat reporting says so far
Google says UNC6040 specializes in voice phishing against Salesforce customers and tricks employees into authorizing malicious connected apps, often modified versions of Data Loader. GTIG also said the follow-on extortion activity it tracks as UNC6240 has repeatedly used the ShinyHunters name in ransom or pressure messages.
Salesforce, for its part, warned in March 2026 about a separate but related campaign involving misconfigured public Experience Cloud guest-user settings. The company said this activity stemmed from customer misconfiguration, not a flaw in the Salesforce platform itself, and said attackers used a modified Aura Inspector tool to scan and extract data from overly permissive public sites.
Taken together, those official statements point to two realistic ways a company like Cisco could end up in a ShinyHunters-style extortion narrative: identity-based compromise through vishing and malicious OAuth-connected apps, or data exposure through poorly locked-down Experience Cloud guest access. What they do not prove is which route, if any, explains the specific Cisco listing now circulating.
What remains confirmed, likely, and unconfirmed
| Status | Detail |
|---|---|
| Confirmed | A leak-site claim naming Cisco has been publicly reported |
| Confirmed | Cisco disclosed a real vishing-related third-party CRM incident in July 2025 |
| Confirmed | Google tied Salesforce-focused extortion activity to actors who sometimes used the ShinyHunters name |
| Confirmed | Salesforce warned in March 2026 about data exposure via misconfigured Experience Cloud guest access |
| Unconfirmed | The exact “3 million records” figure in the new Cisco claim |
| Unconfirmed | The claim that GitHub repositories and AWS buckets were stolen in the same operation |
| Unconfirmed | Whether the latest Cisco listing reflects a new intrusion, recycled data, or a mix of incidents |
What organizations should learn from this
Even if the Cisco claim turns out to be inflated, the attack pattern is real. Google’s reporting shows that social engineering around Salesforce can bypass normal expectations about passwords and MFA when a victim authorizes a malicious connected app themselves.
Salesforce says customers should audit guest user permissions, keep external access private by default, disable public APIs for guest users where possible, and follow least-privilege access rules. Those steps directly reduce the risk from the large-scale scanning and data theft campaigns now hitting public-facing Salesforce environments.
For companies worried about ShinyHunters-style extortion, the practical priority is not the branding used by the actor. The priority is whether anyone recently approved a suspicious connected app, whether public Experience Cloud pages expose more data than intended, and whether event logs show unusual export activity or mass queries.
Immediate checks for defenders
- Review all Salesforce connected apps and remove anything unrecognized.
- Restrict who can use Data Loader and who can manage connected apps.
- Enforce trusted IP ranges and stronger access controls for administrative users.
- Audit Experience Cloud guest-user permissions and disable public APIs unless they are truly required.
- Review Salesforce event logs for large exports, unusual API activity, and access from unexpected networks.
FAQ
Not publicly, based on the sources I checked. Cisco has a public advisory for a July 2025 CRM vishing incident, but I did not find a Cisco statement that confirms this new April 2026 leak-site claim.
Not necessarily. Salesforce said its March 2026 warning involved customer-configured guest-user settings, not an inherent platform flaw. Google also said the vishing campaign it tracked relied on social engineering and malicious connected apps, not a core Salesforce vulnerability.
That remains unclear. Google said extortion actors following Salesforce intrusions sometimes claimed to be ShinyHunters, likely to increase pressure on victims. That means the branding on a leak site or in an extortion email does not settle attribution by itself.
The main risk is not only exposure of customer and employee data. Stolen CRM records, cloud secrets, OAuth tokens, and repository access can support follow-on phishing, lateral movement, account compromise, and supply-chain abuse. That risk grows if the same actor also reaches GitHub or AWS environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages