Silver Fox targets Japanese firms with tax and HR phishing emails during busy filing season
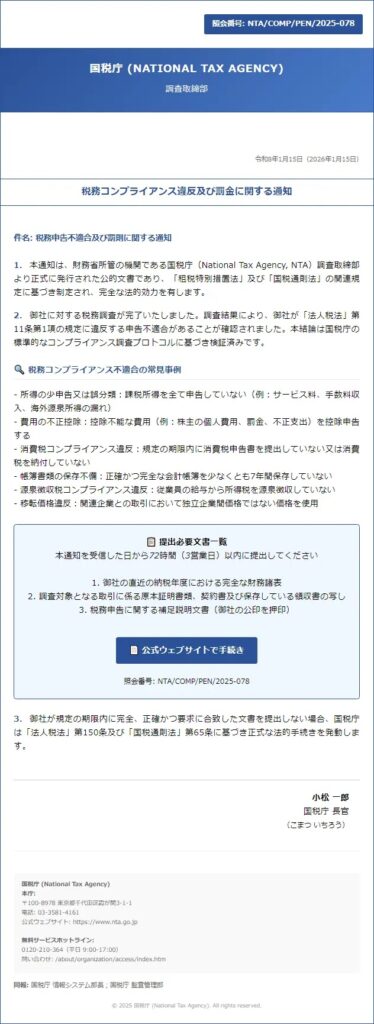
A threat actor known as Silver Fox is targeting businesses in Japan with phishing emails that look like routine tax, payroll, and HR notices. ESET says the campaign focuses on a period when companies already expect a flood of internal messages about tax compliance, salary adjustments, personnel changes, and employee stock ownership plans, which makes the lures more convincing.
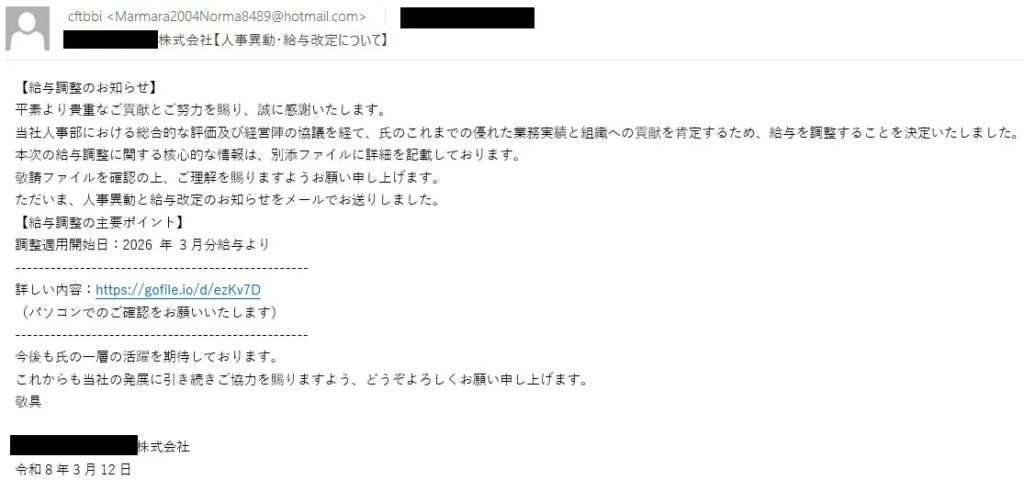
The campaign mainly targets Japanese manufacturers and other businesses, and it uses local language lures tailored to each victim. ESET says Silver Fox includes the company’s name in the subject line and often spoofs real employees or even senior executives, showing that the attackers do research before sending the emails.
If a recipient opens the attachment or follows the malicious link, the attack can install ValleyRAT, a remote access trojan that ESET detects as Win64/Valley. Once active, the malware can give attackers remote control of the infected device, help them steal sensitive data, monitor activity, and keep access alive over time.
Why this campaign stands out
This is not a random spam wave. ESET says Silver Fox has been active since at least 2023 and first focused on Chinese-speaking targets before expanding into Southeast Asia, Japan, and possibly North America. The group runs campaigns in local languages and has targeted sectors that include finance, healthcare, education, gaming, government, and cybersecurity.
What makes the current operation more dangerous is its timing. Japan’s tax and corporate change season creates the perfect cover for fake notices about salary reviews, tax penalties, and staffing updates. ESET says it saw similar activity during the same period last year, which suggests Silver Fox plans its campaigns around predictable business cycles.
The delivery methods also blend into normal business traffic. According to ESET, the attackers use malicious attachments or links that lead to downloadable files, sometimes through public file-sharing services such as WeTransfer or gofile[.]io. The payload often arrives inside ZIP or RAR archives, which can make the file look less suspicious at first glance.
What the phishing emails look like
| Tactic | How Silver Fox uses it |
|---|---|
| Subject line customization | Inserts the target company’s name directly into the email subject |
| Trusted sender spoofing | Impersonates real employees or CEOs |
| Seasonal themes | Uses tax notices, salary changes, personnel moves, and ESOP updates |
| Delivery method | Sends attachments or links to malicious downloads |
| Malware payload | Drops ValleyRAT after the victim opens the file |
| Extra deception | Uses familiar file-hosting platforms and compressed archives |
Source basis: ESET / WeLiveSecurity.
What companies should do now
Businesses in Japan should warn staff that emails about tax issues, salary changes, personnel updates, or stock ownership plans may be part of an active phishing campaign. ESET recommends verifying any such message through a separate channel before opening attachments or downloading files, even when the email appears routine.
Security teams should also remind employees to compare the sender’s display name with the actual email address, watch for unusual phrasing, and treat public file-sharing links with caution. ESET notes that Silver Fox operators are not native Japanese speakers, so some messages may contain subtle wording issues that do not match normal internal communication.
For defenders, this campaign is another reminder that well-timed phishing still works. The attackers do not need flashy techniques when they can hide inside expected business workflows and use pressure points that employees already recognize as urgent.
Quick protection steps
- Verify tax, payroll, or HR emails through a second channel before acting.
- Check that the sender’s real address matches the displayed name.
- Be careful with ZIP or RAR attachments and public file-sharing links.
- Report suspicious emails to IT or security teams right away.
- Keep endpoint protection and system updates current.
FAQ
Silver Fox is a threat actor that ESET says has run finance-themed and business-themed spearphishing campaigns since at least 2023. The group first focused on Chinese-speaking targets and later expanded into Japan and other regions.
ESET says the current activity targets Japanese manufacturers and other businesses during the country’s tax and organizational change season.
The phishing emails can lead to ValleyRAT, a remote access trojan detected by ESET as Win64/Valley.
They copy subjects employees already expect to see, such as salary changes, tax compliance notices, personnel updates, and employee stock plan changes. ESET also says the attackers often spoof real names from the target organization.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages