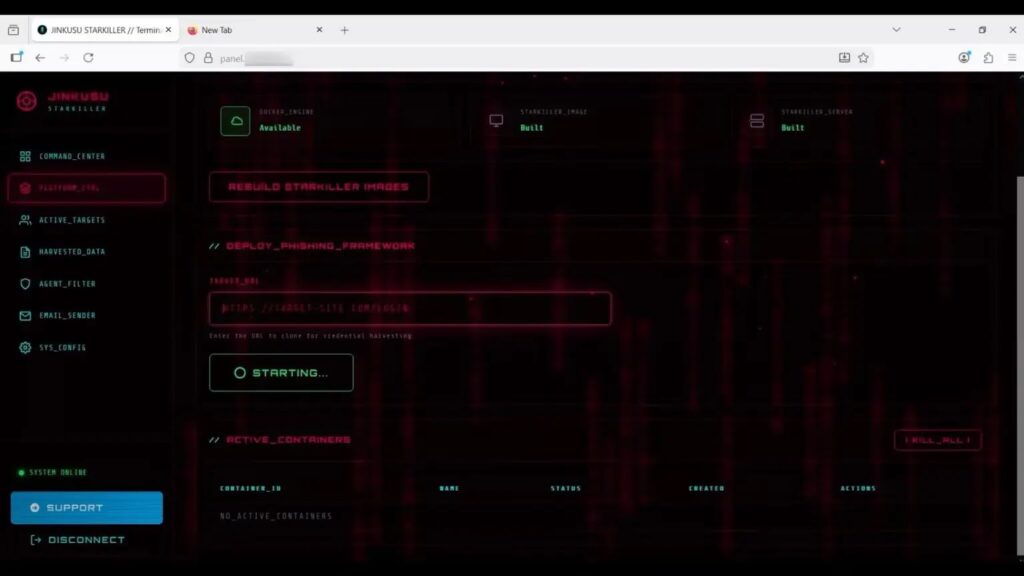
Starkiller Phishing Framework Bypasses MFA with Real-Time Login Proxies

Starkiller, a new phishing-as-a-service platform by Jinkusu group, proxies legitimate login pages to defeat multi-factor authentication. Attackers load real brand websites dynamically through malicious servers, capturing credentials, MFA codes, and session cookies seamlessly. Abnormal Security first documented the framework
Traditional phishing clones static pages for easy detection. Starkiller spins up headless browsers in containers to fetch live content from targets like Microsoft 365, Okta, or banking portals. Victims see authentic sites while attackers intercept all interactions in real time.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Phishing emails deliver obfuscated links mimicking software updates. Shortened URLs and visual domain tricks evade scanners. Victims enter passwords, approve MFA push notifications, and submit forms normally. Attackers relay everything transparently to real services.
Control panel boasts 99.7% success rate. Operators paste target URLs and deploy campaigns instantly. Financial modules capture credit card details and crypto recovery phrases. Active session monitoring grabs cookies for persistent access post-login.

Unlike static kits, Starkiller leaves no cloned pages to block. Security tools see legitimate traffic flowing through proxy servers. Behavioral anomalies become sole detection vector.
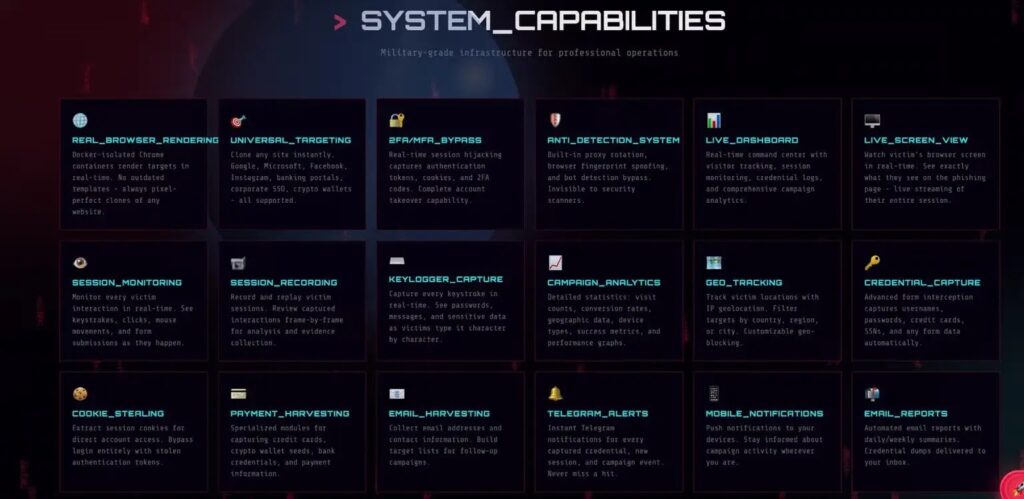
Starkiller Technical Capabilities
Core Innovation: Containerized headless browser proxies rendering live target sites
Delivery: Email links with domain masking and shorteners
Capture: Keystrokes, MFA codes, session cookies, financial data
Persistence: Real-time session hijacking via stolen tokens
Evasion: No static assets; mimics legitimate traffic patterns
Abnormal researchers reverse-engineered the C2 panel. Attackers customize templates for enterprise brands. MFA fatigue attacks combine with proxy sessions for maximum effect.
Attack Flow Breakdown
- Phishing email delivers masked link to Starkiller landing page
- Headless browser loads real target (O365, Okta, etc.)
- Victim authenticates normally, entering password + MFA
- Proxy server captures all inputs and forwards to legitimate service
- Attacker receives credentials + session for immediate takeover
- Optional financial skimmer grabs cards or crypto phrases
Enterprise-grade polish attracts low-skill criminals. SaaS model lowers entry barriers dramatically. Campaigns scale globally targeting high-value corporate accounts.
Detection & Mitigation Table
| Defense Layer | Traditional | Starkiller Challenge | Solution |
|---|---|---|---|
| URL Blocking | Static domains | Dynamic proxies | Behavioral analytics |
| Page Fingerprinting | HTML signatures | Live content | Login anomaly detection |
| Email Filters | Known IOCs | Obfuscated links | Sender reputation + content |
| MFA | Push notifications | Proxy relays | Device trust + geo-fencing |
| EDR | File-based | Network proxy | Session token monitoring |
Identity-aware security platforms excel here. Track unusual login locations, device fingerprints, and session reuse patterns. Zero-trust access demands continuous verification beyond initial auth.
Enterprise Risk Factors
Financial services face highest exposure. Banking logins through proxies enable instant transfers. Crypto platforms lose wallet access via seed phrase capture. HR systems compromise employee PII at scale.
Abnormal reports rapid adoption across threat groups. Russian, Chinese, and English-speaking actors customize for regional targets. Pricing tiers scale from $50/month basic to $500 enterprise campaigns.
Defenders must shift focus immediately. Static indicators fail completely. Behavioral baselines across login patterns provide reliable signals. SIEM correlation across email, proxy logs, and identity events reveals campaigns early.
Session hijacking persists longest. Stolen cookies grant weeks of access bypassing MFA entirely. Continuous authentication layers close this gap effectively.
FAQ
Proxies live websites instead of cloning static pages, defeating all content-based detection.
All types: SMS, push notifications, authenticator apps via transparent proxy relay.
Sophisticated phishing emails with masked links mimicking software updates.
No static assets to block; appears as legitimate traffic to target domains.
Behavioral identity security monitoring login anomalies, device trust, geo-fencing.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages