Steaelite RAT Powers Double Extortion Attacks on Enterprises

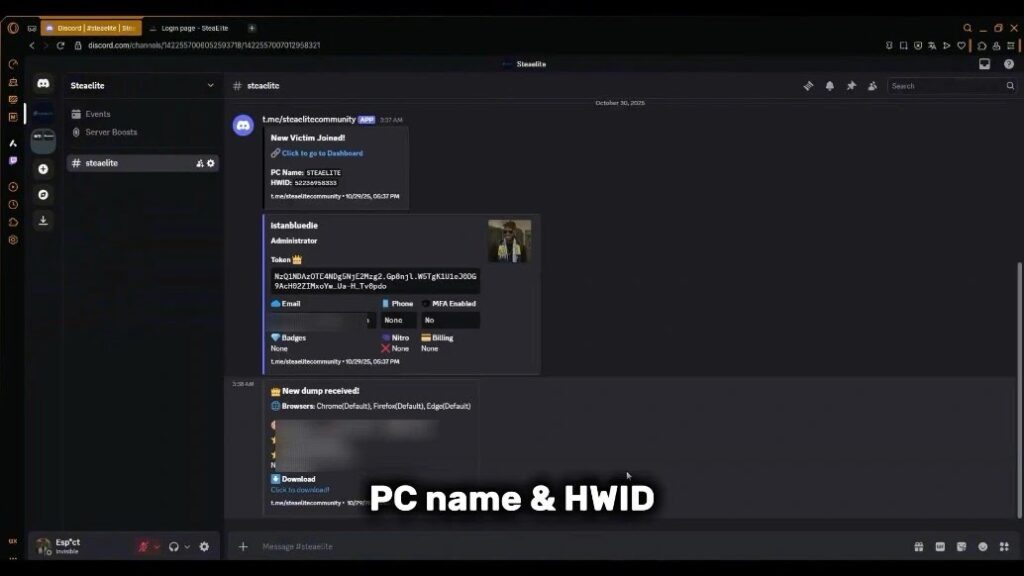
Steaelite RAT merges data theft and ransomware into one browser panel. This new malware hit dark web markets in November 2025. Enterprises now face faster double extortion from low-skill attackers. The tool claims full undetectability on Windows 10 and 11.
Security teams spotted Steaelite through underground forum posts. Sellers promote it with YouTube demos. Over 87 messages show strong buyer interest. BlackFog research calls it a game changer for solo cybercriminals.
Traditional attacks needed separate tools and teams. Steaelite handles both stages alone. Developers even plan an Android ransomware add-on. This threatens employee mobiles used for work logins.
Steaelite Key Features
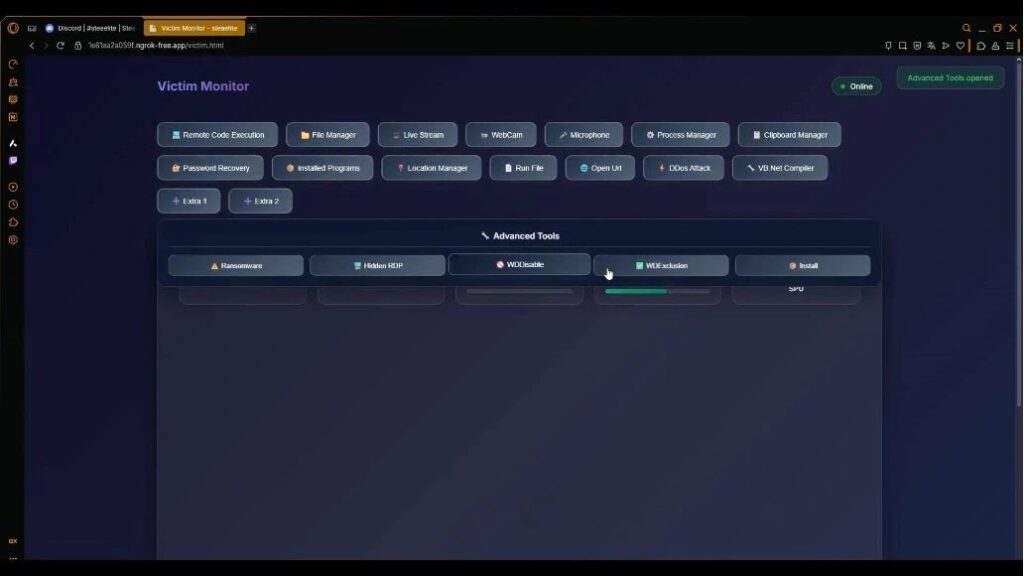
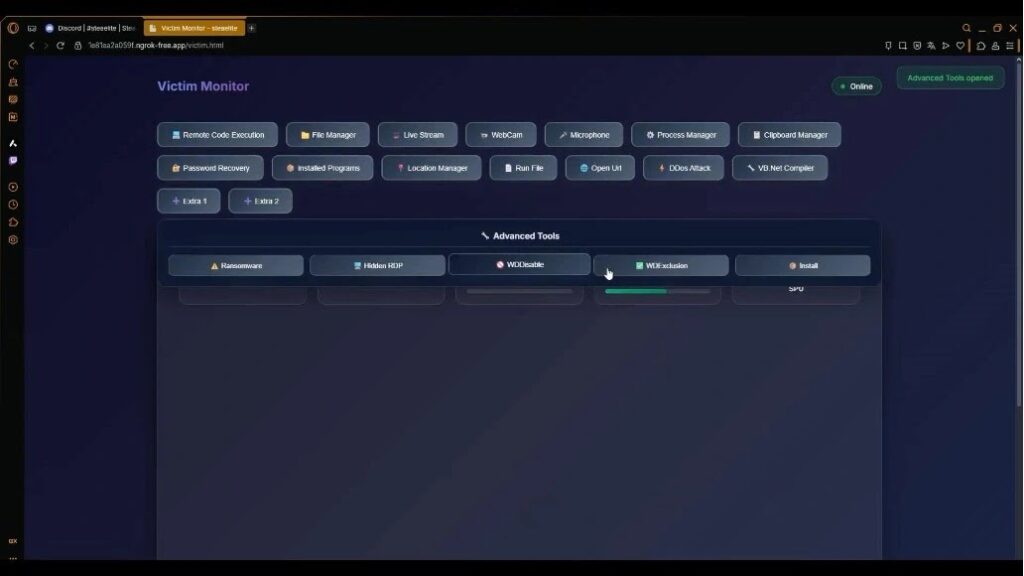
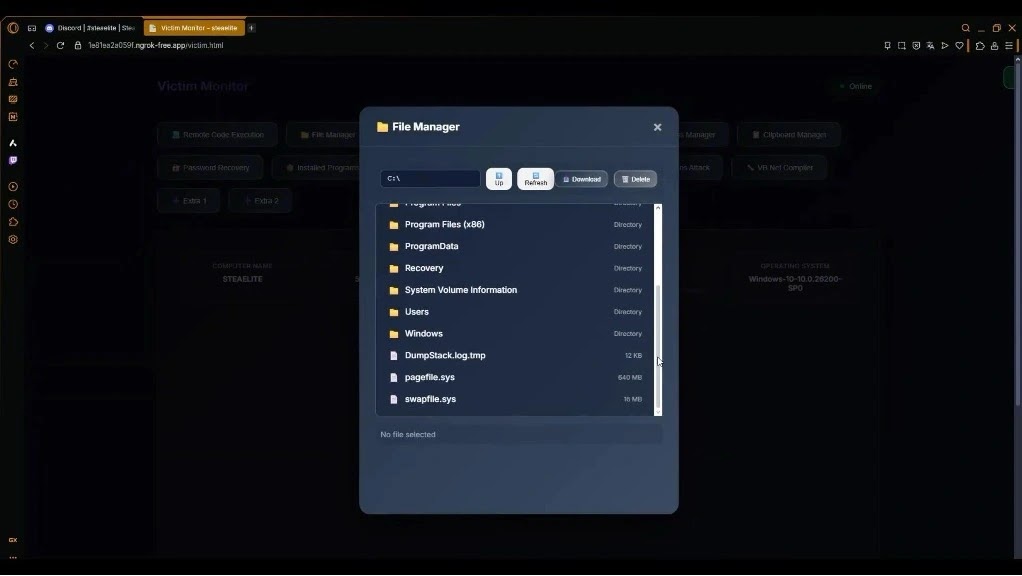
The browser dashboard automates the kill chain. Victims connect and lose data instantly. Operators get full control with clicks.
| Feature | Function | Risk Level |
|---|---|---|
| Auto Credential Dump | Grabs browser passwords, cookies on connect | High |
| HVNC Monitoring | Hidden VNC screen access | Critical |
| Ransomware Deploy | One-click encryption from panel | Critical |
| Crypto Clipper | Swaps wallet addresses in clipboard | High |
| UAC Bypass | Runs commands as admin without prompts | High |
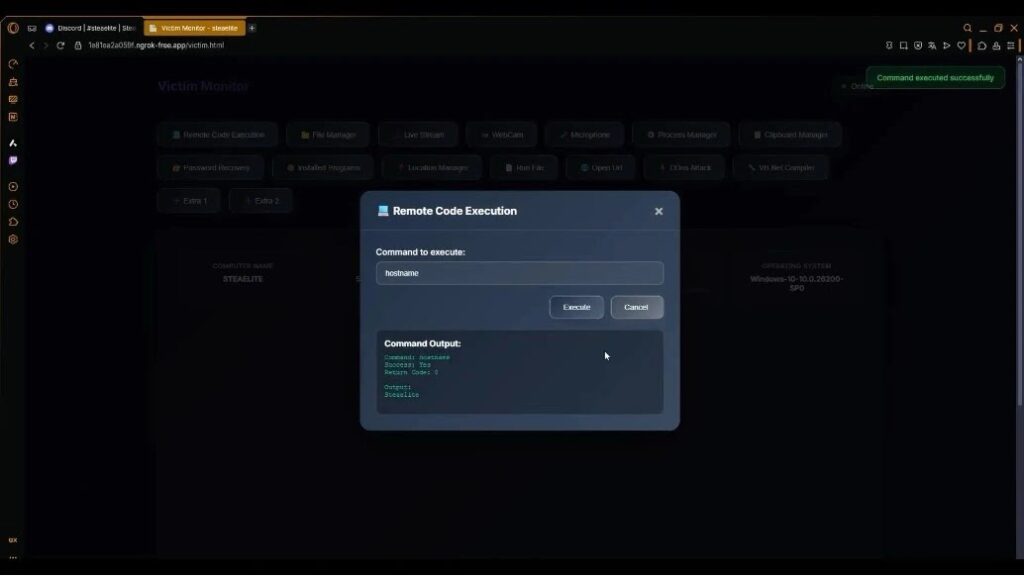
Live tools include webcam access, file manager, and DDoS modules. Remote code execution works via browser prompt.
Attack Workflow
Steaelite starts with initial access. It exfils data before operators log in. Ransomware follows if paid demands fail.
Attackers bypass banking apps and Windows Defender. File manager downloads proof for leaks. Clipboard monitoring steals crypto quietly.
Enterprises lose credentials early. Even blocked ransomware leaves stolen files. Mobile expansion widens targets.
BlackFog Findings
Analysts note the all-in-one design lowers barriers. No need for custom malware. Dark web access costs stay low.
Official statement from BlackFog: “Steaelite consolidates double extortion in one panel.”
Defense Measures
Security teams can fight back:
- Block ngrok-free.app domains in firewalls.
- Watch for HVNC processes and UAC bypasses.
- Audit browser credentials weekly.
- Use app whitelisting on endpoints.
- Deploy phishing-proof MFA everywhere.
Monitor SHA-256: b2a8d97da2a653de75d3d1be5839. Check paths like /dashboard.html.
Indicators of Compromise
| IOC Type | Value |
|---|---|
| SHA-256 | b2a8d97da2a653de75d3d1be5839 |
| C2 Domain | 1e81ea2a059f.ngrok-free.app |
| Paths | /dashboard.html, /victim.html |
| Username | Steaelite |
FAQ
Combines data theft and ransomware in one panel.
November 2025 on dark web forums.
Android ransomware module in development.
Grabs credentials on victim connect, before operator action.
Block C2 domains, use MFA, whitelist apps.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages