Steganography NPM Attack Hides Pulsar RAT in Innocent PNG Images
Malicious NPM package buildrunner-dev embeds Pulsar RAT inside PNG images using steganography. Typosquatted buildrunner package evades scanners by encoding malware in pixel RGB values. Veracode uncovered seven-layer obfuscated batch file delivering UAC bypass and process hollowing.
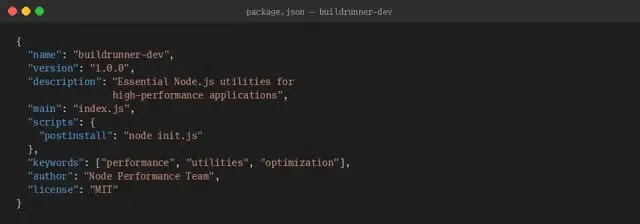
Developers install via npm install triggering postinstall init.js script. Codeberg repository serves packageloader.bat with 1,653 obfuscated lines. Junk comments, fake base64, and dummy variables hide 21 functional instructions.
Batch file checks admin privileges then exploits fodhelper.exe UAC bypass silently. Conhost.exe launches hidden PowerShell evading behavioral detection. Anti-virus enumeration dictates customized infection paths.
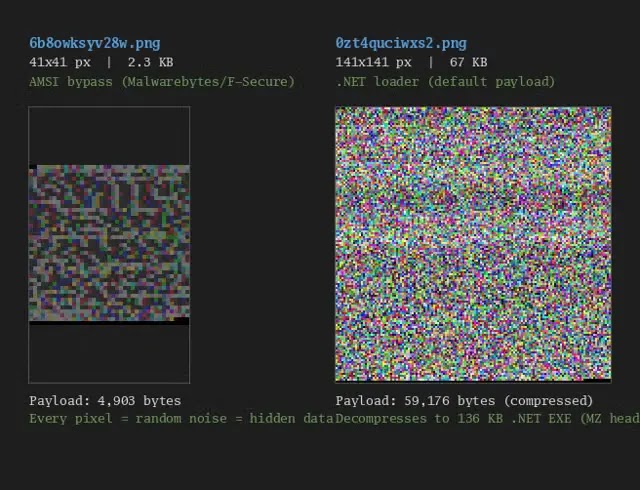
ImgBB hosts two steganographic PNGs carrying encrypted payloads. 6b8owksyv28w.png (41×41px) contains 4,903-byte AMSI bypass PowerShell. 0zt4quciwxs2.png (141×141px) hides 136KB .NET loader in pixel noise.
Third PNG at i.ibb.co/tpyTL2Zg/s9rugowxbq8i.png serves live C2 channel. Pulsar RAT downloads via process hollowing into legitimate Windows binaries. Startup folder persistence ensures reboot execution.
Supply chain attacks weaponize developer trust in package managers. Abandoned legitimate packages create perfect typosquatting vectors. Steganography defeats signature and heuristic scanners completely.
Attack Chain Table
| Stage | Action | Technique |
|---|---|---|
| Lure | npm install buildrunner-dev | Typosquatting |
| Stage 1 | init.js downloads packageloader.bat | Codeberg repo |
| Escalation | fodhelper.exe UAC bypass | MITRE T1548.002 |
| Stage 2 | Steganographic PNG extraction | ImgBB pixel decode |
| Persistence | %AppData%\protect.bat | Startup folder |
| Payload | Pulsar RAT process hollowing | Legit binary injection |
Key Indicators
| Type | Indicator |
|---|---|
| NPM Package | buildrunner-dev |
| Batch File | packageloader.bat |
| Persistence | %AppData%\protect.bat |
| Executable | JJYDJO.exe |
| C2 Image | i.ibb.co/tpyTL2Zg/s9rugowxbq8i.png |
| AMSI PNG | 6b8owksyv28w.png |
| Loader PNG | 0zt4quciwxs2.png |
Development pipelines require package allowlisting immediately. Postinstall script execution demands sandbox isolation.
Defensive Actions
- Audit NPM dependencies weekly
- Disable automatic postinstall hooks
- Block ImgBB domains in corporate firewalls
- Monitor fodhelper.exe registry abuse
- Deploy steganography detection tools
- Scan for protect.bat in AppData
- Train developers on typosquatting risks
Enterprise CI/CD pipelines face highest exposure. Compromised developer machines enable lateral movement. Rapid package removal lags behind sophisticated delivery.
FAQ
Steganography encodes payloads in RGB pixel values.
fodhelper.exe registry abuse without prompts.
Typosquatted NPM package buildrunner-dev.
Pulsar RAT remote access and control.
Windows Startup folder via protect.bat.
Seven layers hiding 21 functional lines in 1,653 total.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages