Storm-2755 uses AiTM session hijacking to redirect employee salaries in Canada

Microsoft says a financially motivated threat actor tracked as Storm-2755 is targeting Canadian employees in a “payroll pirate” campaign that redirects salary payments to attacker-controlled bank accounts. The group uses adversary-in-the-middle, or AiTM, phishing to steal live session tokens, then abuses those sessions to access payroll and HR systems without needing to beat multi-factor authentication again.
According to Microsoft Incident Response researchers, the campaign stands out because it does not focus on one sector. Instead, Storm-2755 broadly targets users in Canada through generic searches such as “Office 365” and even common misspellings like “Office 265,” then pushes victims toward a fake Microsoft 365 sign-in page through SEO poisoning and malvertising.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Once a victim signs in, the attackers steal both credentials and authenticated session data. Microsoft says that lets Storm-2755 reuse a valid session and bypass legacy MFA protections that are not phishing-resistant, which gives the actor a quiet path into Microsoft services and, in some cases, payroll platforms such as Workday.
How the attack works
Microsoft says the campaign begins with an actor-controlled domain, bluegraintours[.]com, placed high in search results. Victims who click the link land on a phishing page that closely imitates Microsoft 365. Sign-in logs then show a 50199 interrupt error just before the attacker takes over the same session.
One of the clearest signs of compromise is the shift in user-agent. Microsoft says the session often switches to Axios, typically version 1.7.9, while the session ID stays the same. That combination suggests the actor replayed a stolen session token instead of creating a fresh login. Microsoft also says this attack path appears to take advantage of known Axios vulnerabilities, including CVE-2025-27152.
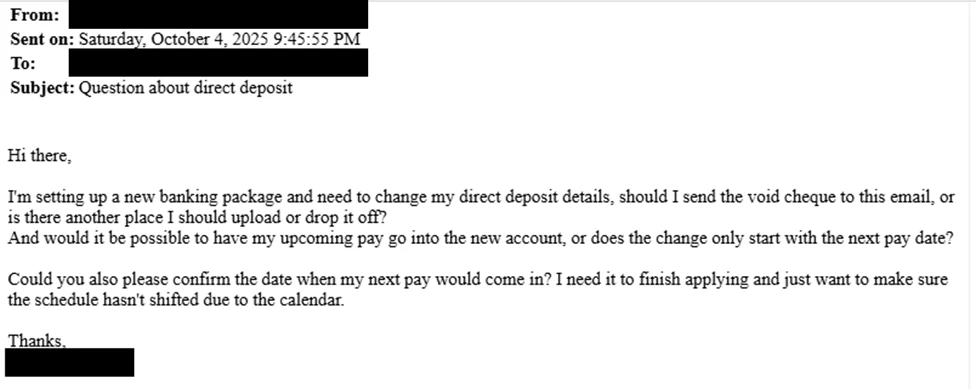
After that, Storm-2755 searches internal resources and mailboxes for terms tied to payroll and HR. Microsoft observed keyword searches such as “payroll,” “HR,” “human,” “resources,” “finance,” and “admin,” followed by phishing emails sent from the victim’s real inbox with subject lines like “Question about direct deposit.”
What the attackers do after compromise
If the email trick works, HR staff may manually change the employee’s direct deposit details. When that fails, Microsoft says the attackers sometimes log directly into HR software-as-a-service platforms such as Workday and change the banking information themselves. In one confirmed case, that led to a payroll deposit being sent to an attacker-controlled bank account.
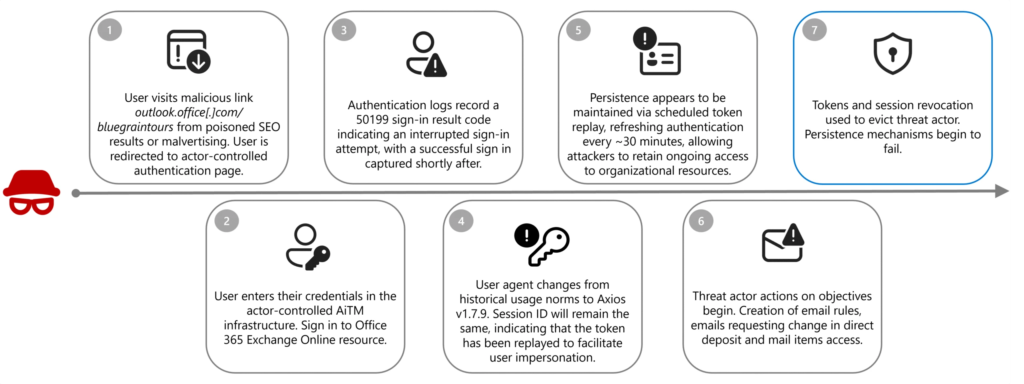
Storm-2755 also hides its activity carefully. Microsoft says the group creates inbox rules that move messages containing terms like “direct deposit” or “bank” into conversation history and stop further rule processing. That prevents the victim from seeing replies from HR about the fraudulent payment change.
The actor also renews stolen sessions around 5:00 AM in the user’s local time zone to lower the odds of a real user interrupting the session. Microsoft says it saw non-interactive sign-ins to OfficeHome tied to the Axios user-agent about every 30 minutes until defenders revoked the tokens.
Key campaign details
| Item | Details |
|---|---|
| Threat actor | Storm-2755 |
| Victims | Canadian employees across multiple sectors |
| Initial lure | SEO poisoning and malvertising |
| Phishing domain | bluegraintours[.]com |
| Main technique | AiTM session hijacking |
| User-agent seen after takeover | axios/1.7.9 |
| Signs of abuse | 50199 interrupt error, same session ID, user-agent shift |
| Follow-on targets | HR teams, payroll workflows, Workday and similar services |
| Defense evasion | Inbox rules, off-hours token renewal |
| Financial impact | Salary payments redirected to attacker-controlled accounts |
The table above is based on Microsoft’s April 9 research post on Storm-2755.
Why this campaign matters
This is not just another phishing story. The campaign shows how attackers can turn a stolen session into direct financial theft by abusing normal business workflows inside email and payroll systems. Because the attacker acts inside a real employee account, the fraud can look like a routine request instead of an intrusion.
The use of AiTM also matters because it weakens older MFA setups. Microsoft says phishing-resistant methods such as FIDO2 and WebAuthn are designed to stop this kind of token theft, while SMS codes, push prompts, and email-based one-time passwords often do not provide the same level of protection.
Microsoft’s findings also suggest that security teams need to watch for session anomalies, not just failed logins. A valid session can remain active for days or weeks, and in some cases Storm-2755 changed passwords and MFA methods to keep access after the original token expired.
What organizations should do now
- Revoke compromised tokens and sessions immediately.
- Remove suspicious inbox rules, especially ones tied to payroll or banking terms.
- Reset passwords and re-register MFA methods for affected users.
- Enforce phishing-resistant MFA such as FIDO2 or WebAuthn.
- Use Conditional Access policies to shorten session lifetime and force reauthentication when risk changes.
- Enable Continuous Access Evaluation where supported so stolen tokens lose value faster.
- Alert on suspicious inbox-rule creation and audit HR and payroll platforms for unauthorized changes.
- Watch for unusual Axios user-agents tied to Microsoft service sign-ins.
FAQ
Microsoft says Storm-2755 steals authenticated sessions from Canadian employees, then uses those sessions to change payroll details and redirect salary payments.
It uses AiTM phishing to steal session cookies and OAuth access tokens after a real sign-in. That gives the attacker a live authenticated session without needing another MFA prompt.
Microsoft observed the session user-agent change to Axios 1.7.9 while the session ID stayed the same. It says the attack path appears to exploit known Axios issues, including CVE-2025-27152.
Unexpected direct deposit change requests, especially those sent from legitimate employee accounts, plus silent mailbox rule creation and unauthorized updates in Workday or similar systems.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages