Suspected DPRK-linked intrusions hit crypto firms, steal cloud secrets, and raid container registries (report)

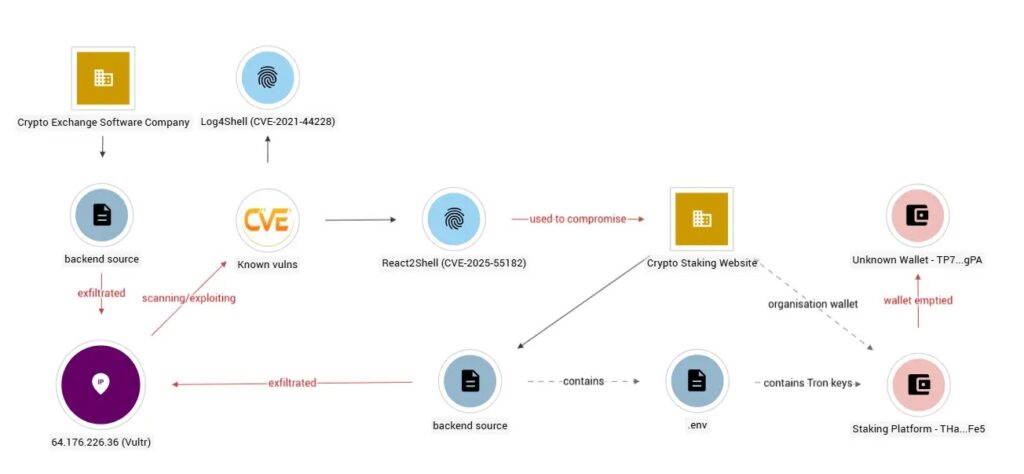
A suspected North Korea linked threat actor has compromised multiple cryptocurrency organizations and moved across the crypto supply chain, from staking platforms to exchange infrastructure, according to new research published by Ctrl-Alt-Intel. The activity blends web app exploitation with deep cloud post exploitation, then focuses on the assets that matter most in crypto operations: private keys, secrets, and proprietary exchange logic.
Ctrl-Alt-Intel says it identified the campaign through a rare source of evidence: exposed open directories tied to the attacker’s own working environment, which included command history and tooling artifacts. A threat intel vendor archived at least one of those directories during the intrusion window, which helped researchers reconstruct the kill chain without naming victims.
Two entry paths show up in the report. In one track, the attacker mass scanned for React2Shell (CVE-2025-55182) and used WAF bypass techniques to find exposed crypto services, including a USDT staking product. In another track, the attacker already had valid AWS access tokens and moved straight into cloud enumeration, which suggests prior credential theft or reuse from earlier compromise.
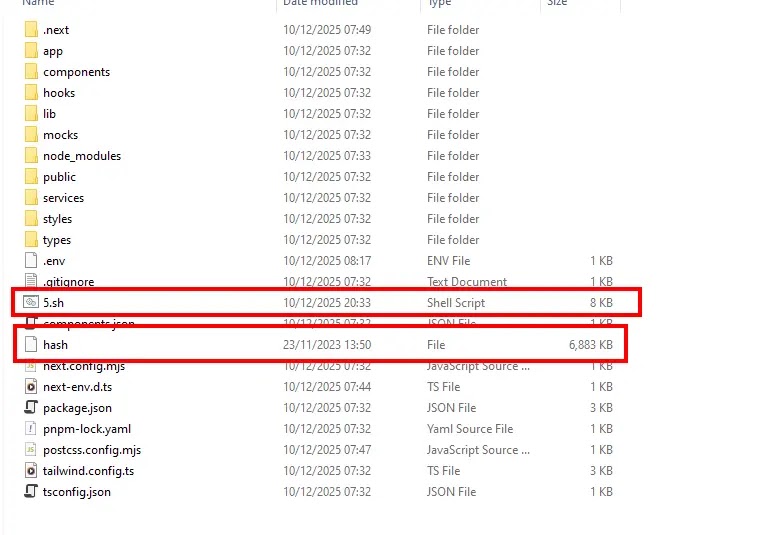
Researchers also describe credential exposure inside application code. In one victim codebase, Ctrl-Alt-Intel found environment variables that referenced Tron wallet keys, plus supporting scripts that interacted with wallet balances. The report notes an on chain TRX transfer around the broader timeframe but stops short of attributing that specific transfer to this actor.
This matters because the attacker’s workflow mirrors the path many crypto teams take in real life. Engineers ship fast, secrets drift into .env files, infrastructure state lands in S3, and container images accumulate internal logic and credentials. The report shows how a single foothold can turn those normal practices into a full cloud compromise.
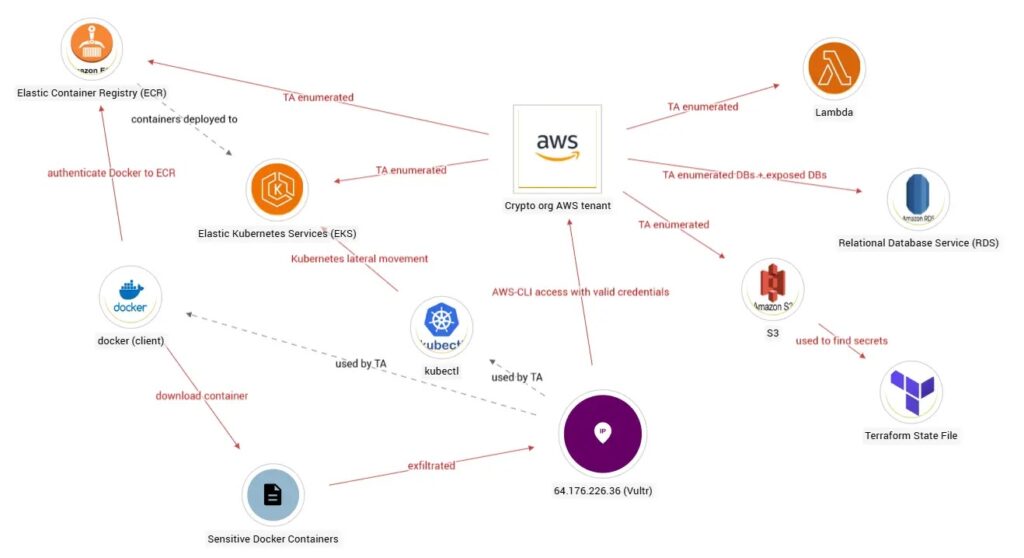
What the attacker did, step by step
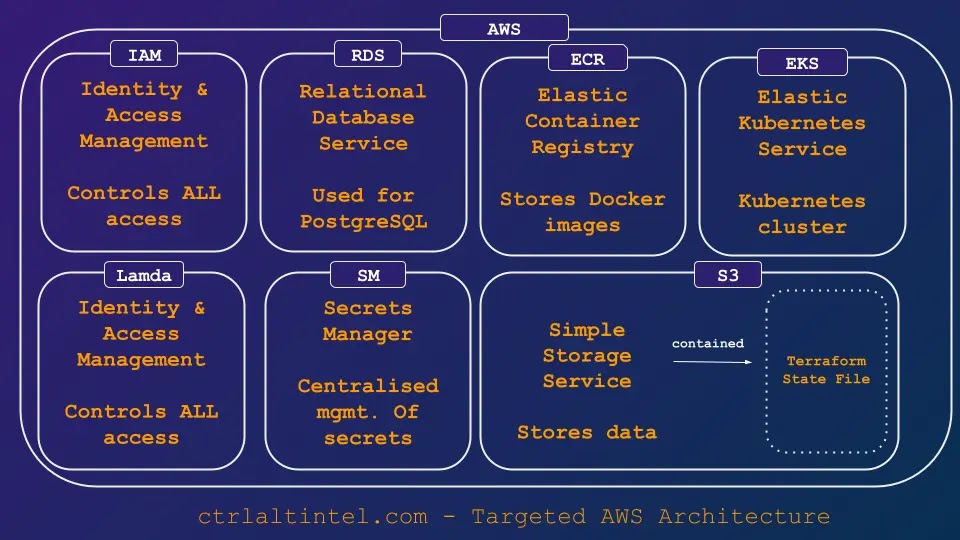
Ctrl-Alt-Intel summarizes a chain that starts with initial access, then quickly pivots into cloud discovery and secret harvesting using standard admin tooling like the AWS CLI and kubectl. The actor enumerated S3, RDS, EC2, Lambda, IAM, EKS, and ECR, then used that visibility to pull credentials from multiple places, including Terraform state files and Kubernetes Secrets.
The report also describes two command and control components: VShell listening on port 8082 and an FRP reverse proxy configured on port 53, a DNS port that many networks treat as routine traffic. Ctrl-Alt-Intel also observed infrastructure access over IPv6, which can slip past monitoring setups that focus mainly on IPv4.
Quick view: kill chain and targets
| Phase | What the report says the actor targeted | Why it matters for crypto teams |
|---|---|---|
| Initial access | React2Shell exploitation and stolen AWS tokens | One foothold unlocks production environments |
| Discovery | S3, RDS, EC2, Lambda, IAM, EKS, ECR enumeration | Attackers map systems fast and pick high value assets |
| Credential access | Secrets Manager, Terraform state, K8s Secrets/ConfigMaps, .env files, containers | These stores often contain wallet keys, API tokens, and signing material |
| Lateral movement | AWS IAM to Kubernetes via EKS kubeconfig update | Cluster access exposes workloads and secrets |
| Collection/exfiltration | Docker images pulled from ECR and saved as tar archives | Images can embed exchange logic and hidden credentials |
| C2 and persistence | VShell on 8082 and FRP over 53, plus IPv6 access | Harder to spot if monitoring misses DNS egress patterns or IPv6 |
Why CVE-2025-55182 keeps showing up
React2Shell (CVE-2025-55182) drew rapid exploitation after disclosure because it can allow unauthenticated remote code execution in affected React Server Components deployments. React published official remediation guidance and later updated its instructions as additional related CVEs appeared.
CISA also added CVE-2025-55182 to its Known Exploited Vulnerabilities catalog, which signals real world exploitation and typically triggers urgent patch expectations for US federal agencies and contractors.
What defenders should prioritize right now
- Patch React2Shell exposures and verify versions against React’s official advisory and your framework’s patched releases.
- Hunt for signs of cloud enumeration at scale, especially aws s3 ls –recursive patterns and bulk reads of Terraform state objects in S3.
- Treat Terraform state as a secret store and lock down access, because state files can hold credentials in plain text by design.
- Audit EKS access paths, including who can run aws eks update-kubeconfig and which IAM roles can authenticate kubectl in the cluster.
- Restrict ECR pulls, monitor unusual image downloads, and scan images for embedded keys and internal endpoints before promotion.
- Monitor DNS egress and IPv6 traffic, then alert on outbound sessions that look like tunnels or long lived reverse proxies.
Indicators and investigation prompts (starter list)
- Web layer: spikes in requests that match known React2Shell probing patterns, especially against server action endpoints and RSC routes.
- AWS: sts:GetCallerIdentity followed by wide service enumeration and aggressive S3 listing.
- S3: reads of *.tfstate, kube configs, *.pem, *.key, *.ppk, plus filenames containing env, secret, cred, or pass.
- EKS: sudden kubeconfig updates paired with kubectl listing of pods, ConfigMaps, and Secrets.
- Network: unexpected inbound on 8082, plus unusual outbound patterns over port 53 that do not look like normal DNS.
FAQ
Ctrl-Alt-Intel links the activity to suspected DPRK based actors with moderate confidence and cites targeting patterns and tradecraft as supporting context.
The report documents exposure of wallet private keys in victim code and notes a TRX transfer around the timeframe, but it does not prove this actor executed that specific theft.
Terraform can store sensitive values in state in plain text, including credentials and tokens, which makes tfstate a high value target once an attacker reaches S3 or your CI/CD storage.
React published a critical advisory for React Server Components and CISA later listed the CVE as known exploited, which puts it in the “patch now” category for exposed services.
Least privilege IAM, short lived credentials, and tight S3 access controls reduce what stolen tokens can reach, especially state files, Secrets Manager, and container registries.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages