TA416 returns to Europe with web bug phishing, PlugX malware, and wider diplomatic targeting

TA416, a China-aligned espionage group also tracked as Mustang Panda, has resumed campaigns against European government and diplomatic targets after a relative lull in the region. Proofpoint says the activity ran from mid-2025 into early 2026 and focused heavily on diplomatic missions to the EU, NATO-linked targets, and later some Middle Eastern government entities.
The campaign stands out because it does not always start with malware. In several cases, the first email only carried a web bug or a unique tracking link, which let the attackers learn who opened the message or clicked the lure before they sent a more dangerous follow-up. Proofpoint says that approach likely helped TA416 refine later malware delivery attempts.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
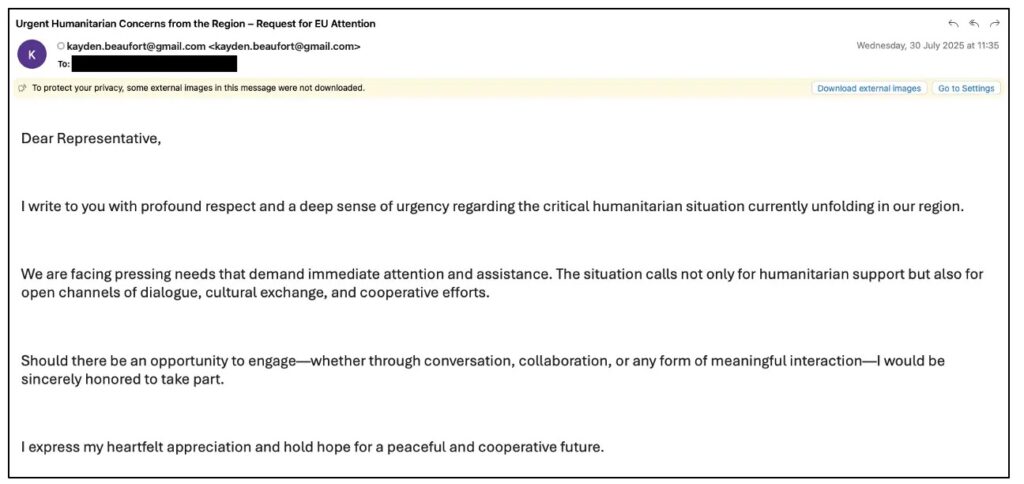
Researchers say the operation mixed freemail accounts, spoofed diplomatic identities, and compromised mailboxes. The lures used themes such as humanitarian concerns, interview requests, collaboration proposals, and a Greenland article copied from the London School of Economics site.
How the campaign worked
Proofpoint says TA416 restarted its European targeting one day after the 25th EU-China summit in July 2025, when it sent more than 100 phishing emails with web bugs to diplomatic missions to the EU across several European countries. In January 2026, the group launched another wave against European government entities using Greenland-themed lure emails with tracking infrastructure tied to TA416.
The malware stage focused on higher-value targets. In late September 2025, the group targeted European ministries of defense and ministries of foreign affairs, especially people assigned to NATO missions and delegations. Proofpoint later saw January and February 2026 campaigns aimed at European government organizations and mailboxes linked to diplomatic missions to the EU and Taiwan.
In mid-March 2026, the operation expanded into the Middle East. Proofpoint says that region had not been a regular TA416 target before and linked the shift to the outbreak of war in Iran. One campaign used a compromised Syrian foreign affairs account and sent Iran-related lures to embassies across multiple Middle Eastern countries. Zscaler separately reported a March 2026 PlugX campaign against Persian Gulf targets and assessed with medium confidence that it may be linked to Mustang Panda.
What changed in the infection chain
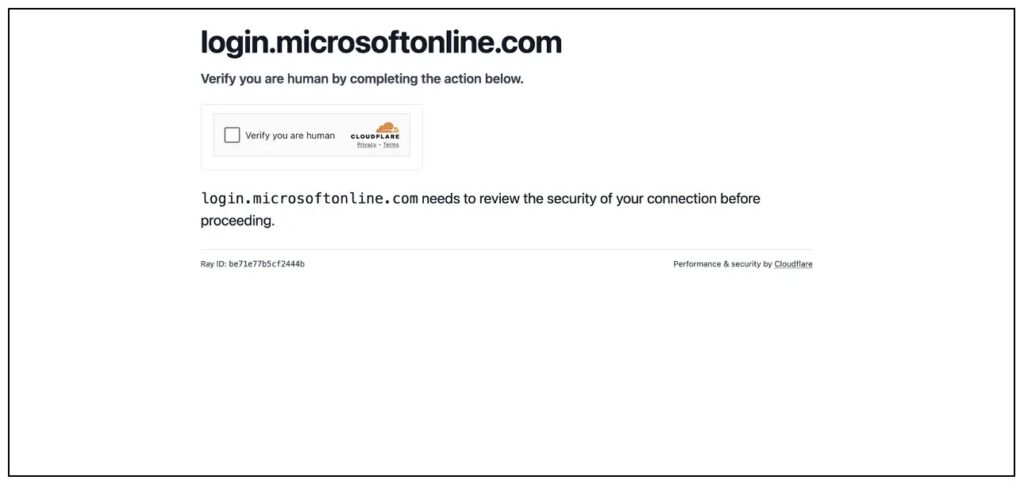
Proofpoint says TA416 kept changing the front end of the attack while preserving the same final goal: loading a customized PlugX backdoor through DLL sideloading. Between September 2025 and March 2026, researchers observed fake Cloudflare Turnstile pages, abuse of Microsoft Entra ID OAuth redirects, and archives containing a renamed MSBuild executable plus a malicious C# project file.
In the earlier wave, fake Turnstile pages impersonated Microsoft login flows and led victims to ZIP files hosted on Azure Blob Storage. Those archives used ZIP smuggling and LNK files to launch the next stage, which ended with a legitimate signed executable, a malicious DLL, and an encrypted payload that loaded PlugX into memory.
By early 2026, the actor shifted again. Proofpoint says later archives came from Google Drive or compromised SharePoint locations, and the malware chain used renamed MSBuild plus a malicious CSPROJ file to decode Base64 URLs, fetch another sideloading package into a temp folder, and launch PlugX. In March 2026 samples, the sideloading set was copied to C:\Users\Public\Canon and persistence came through a Run registry key named Canon. Proofpoint also said the loader used API hashing, junk code, and control-flow flattening to resist analysis.
Why this matters
This is a classic espionage operation, not a smash-and-grab cybercrime run. The web bug stage gives the attackers quiet reconnaissance, while the later PlugX infection can provide host details, remote access, payload delivery, reverse shell capability, and uninstall functions. Proofpoint says the PlugX variant used HTTP-based command and control with RC4-encrypted traffic.
The broader attribution also fits a long-running pattern. MITRE ATT&CK describes Mustang Panda as a China-based cyber espionage actor active since at least 2012 and says the group has repeatedly targeted government and diplomatic organizations using tailored phishing lures and decoy content.
For defenders, the lesson is simple. Treat diplomatic-themed emails, unexpected cloud-hosted archives, and Microsoft-branded login links that end in file downloads as high-risk, especially if they involve LNK, ZIP, RAR, CSPROJ, or unusual MSBuild execution. Proofpoint’s findings show that TA416 keeps changing delivery methods fast, but the operational purpose stays the same.
Key signs defenders should watch
- Emails with web bugs or unique image links used for recon before malware delivery.
- Phishing lures tied to diplomacy, humanitarian issues, interviews, or current geopolitical events.
- Links that start on trusted Microsoft domains but redirect to attacker-controlled download pages through Entra ID abuse.
- Archives from Azure Blob Storage, Google Drive, or compromised SharePoint sites that contain LNK files, renamed MSBuild, or malicious project files.
- PlugX-style persistence, including files placed in public folders and Run registry keys.
Attack chain summary
| Stage | What researchers observed | Why it matters |
|---|---|---|
| Reconnaissance | Web bug emails and unique tracking URLs | Helps the actor identify engaged targets before sending malware |
| Initial lure | Diplomacy and geopolitics-themed phishing emails | Increases the odds that government staff will open the message |
| Delivery | ZIP archives, LNK files, fake Turnstile pages, Entra ID redirect abuse | Gives the attacker multiple ways to bypass defenses and reputation checks |
| Execution | Renamed MSBuild, malicious CSPROJ, DLL sideloading | Helps launch malware while blending in with legitimate tools |
| Payload | Customized PlugX backdoor | Supports espionage, follow-on payloads, and remote command execution |
| Persistence and evasion | Run key persistence, API hashing, junk code, control-flow flattening | Makes removal and analysis harder |
FAQ
TA416 is a threat cluster widely associated with Mustang Panda, a China-linked cyber espionage actor that targets governments, diplomats, NGOs, and related organizations.
The group combined quiet email recon using web bugs with later malware delivery, which let it test engagement before escalating to PlugX infection.
Proofpoint said the main targets included European diplomatic missions, ministries of defense, ministries of foreign affairs, NATO-linked delegations, and later government and diplomatic entities in the Middle East.
Researchers said the end goal stayed consistent across several infection chains: a customized PlugX backdoor delivered through DLL sideloading.
Prioritize filtering and sandboxing for cloud-hosted archives, restrict unnecessary MSBuild execution, monitor Run registry changes, and treat diplomatic lures with embedded tracking content as suspicious. That guidance follows directly from the attack patterns Proofpoint described.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages