Tax-themed Google Ads push rogue ScreenConnect and a kernel-level EDR killer, Huntress warns

Cybercriminals are abusing Google Ads tied to tax-related searches to infect Windows PCs with a stealthy attack chain that ends in a kernel-level tool designed to kill security software, according to Huntress. The campaign has been active since at least January 2026 and targets people searching for W-2 and W-9 forms during tax season.
Huntress says the attackers used fake tax form pages and rogue ScreenConnect installers to gain remote access, then deployed a multi-stage payload that disabled products such as Microsoft Defender, Kaspersky, and SentinelOne. In Huntress’ view, the activity points to either ransomware staging or initial access brokerage, based on what the intruders did after getting in.
The lure works because it matches what victims already want. Someone searches for a tax form, clicks a sponsored result, lands on a convincing page, and downloads what looks like a normal file. Instead of getting only a document or form, they end up giving the attacker hands-on access to the machine. Huntress said it traced more than 60 rogue ScreenConnect sessions across its customer base that tied back to this campaign.
How the attack starts
According to Huntress, one observed chain began when a user searched for a W-2 tax form and clicked a sponsored Google result. That ad led through a redirect to a fake landing page serving a malicious MSI installer disguised as a tax-related file. The installer then deployed ScreenConnect, which gave the attacker remote control over the system.
That choice matters because ScreenConnect is a legitimate remote management tool. A victim may not question the install, and some security teams may not immediately treat it as malware. Huntress said the attackers even used trial cloud instances, which helped them blend in while keeping full keyboard-and-mouse access.
The campaign also did not stop at tax lures. Huntress found a fake Chrome update page in the same exposed infrastructure, with Russian-language JavaScript comments, suggesting the operator runs multiple social engineering fronts at once.
What happens after access
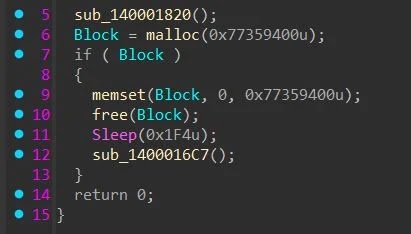
After ScreenConnect opened the door, the attacker deployed a crypter Huntress calls FatMalloc. Huntress said the tool allocates 2GB of memory and fills it before releasing it, a trick that can waste emulator time and cause weaker sandboxes to fail before they ever reach the real payload.
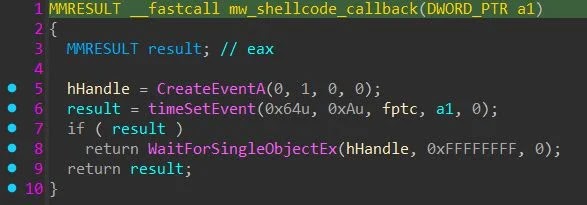
FatMalloc then uses the Windows multimedia timer API to trigger shellcode through a callback path rather than a more obvious thread creation method. Huntress said that approach can reduce visibility because execution appears to come through winmm.dll.
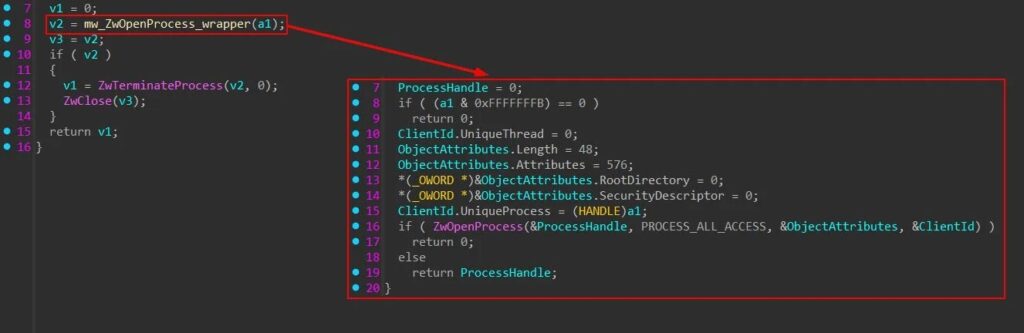
The final payload, called HwAudKiller by Huntress, drops a Huawei audio driver to disk and registers it as a kernel service. Because the driver carries a valid Huawei signature, Windows loads it, and the malware then uses it to terminate targeted security processes from kernel mode. Huntress said the tool loops through running processes and sends matching IDs to the driver, which then kills them with kernel privileges.
Why defenders should pay attention
This is not a simple fake-download scam. It combines malvertising, remote access, anti-analysis techniques, and bring-your-own-vulnerable-driver tactics in one chain. That makes it more dangerous than ordinary malware droppers and much harder to stop once the attacker gains access.
Huntress also described post-compromise behavior that looked consistent with pre-ransomware activity. In one intrusion, the attacker dumped LSASS credentials and used NetExec to harvest accounts across the network after blinding endpoint defenses.
Google’s own advertising rules state that malicious software is not allowed in ads or destinations linked from ads, and its misrepresentation policy bars deceptive destinations that mislead users. Even so, this campaign shows how attackers still slip harmful pages into sponsored search flows at exactly the moment users are most likely to trust the result.
What users should do right now
The safest move is simple. Do not download tax forms from ads or third-party sites.
The IRS publishes official pages for both W-2 and W-9 information, and taxpayers should use IRS pages directly when they need forms or instructions. IRS.gov also maintains a central forms and instructions hub for official downloads.
If a machine already installed a tax-related MSI from an ad, defenders should assume compromise until proven otherwise. Huntress recommends treating any unapproved ScreenConnect trial instance as suspicious, especially instance patterns tied to temporary relay infrastructure.
Key details at a glance
| Item | Finding |
|---|---|
| Campaign theme | Tax-season searches for W-2 and W-9 forms |
| First observed activity | At least January 2026 |
| Initial access | Rogue ScreenConnect installer delivered through Google Ads flow |
| Main evasion stage | FatMalloc anti-analysis crypter |
| Final payload | HwAudKiller |
| Driver abuse | Signed Huawei audio driver used for BYOVD-style process killing |
| Security products targeted | Microsoft Defender, Kaspersky, SentinelOne |
| Likely follow-on activity | Credential dumping and lateral account harvesting |
Signs of compromise
- ScreenConnect installed without IT approval
- Tax-themed MSI files downloaded from sponsored search results
- New kernel driver creation from temporary or unusual directories
- Security tools suddenly stopping without a clear reason
- Suspicious activity involving LSASS access or mass credential collection
- Multiple relay or remote-management tools appearing on the same host
What security teams should prioritize
- Block or strictly control remote management tools that users do not need
- Alert on unexpected ScreenConnect deployments, especially trial instances
- Watch for new kernel services and driver creation events
- Investigate binaries launched from ScreenConnect working directories
- Train users to avoid sponsored results for government forms and common downloads
- Direct employees to official IRS pages instead of search ads for tax documents
FAQ
It starts with malicious ads tied to tax-form searches. The forms themselves are legitimate, but attackers used fake pages and ad redirects to abuse that demand.
Because ScreenConnect is a legitimate remote access tool. That can make the first stage look less suspicious and gives the attacker immediate control over the device.
Huntress said the chain ends with a kernel-level driver abuse technique that kills endpoint protection tools before the attacker moves deeper into the environment.
From official IRS pages and the IRS forms portal, not from sponsored search results or lookalike domains.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages