Threat actors intensify targeting of IP cameras across the Middle East amid ongoing conflict

Check Point Research says it observed a sharp rise in attempts to exploit internet-connected Hikvision and Dahua IP cameras across Israel, Qatar, Bahrain, Kuwait, the UAE, Cyprus, and Lebanon starting February 28, 2026. The activity came from infrastructure Check Point attributes to multiple Iran-nexus threat actors, and it focused only on these two camera vendors in the telemetry Check Point analyzed.
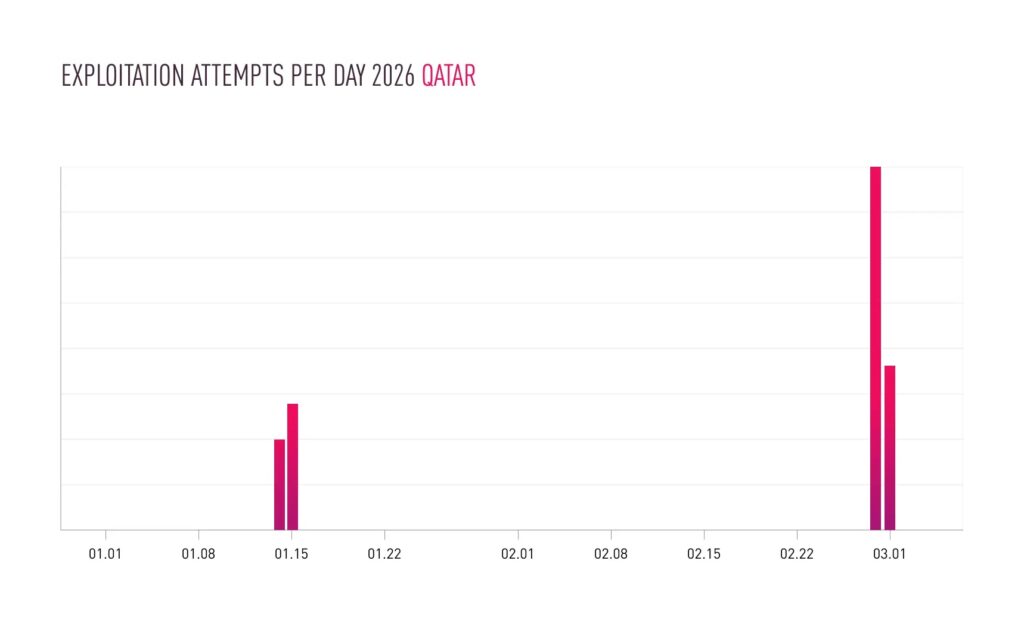
Check Point also says it saw earlier, more targeted waves on January 14–15 against cameras in Israel and Qatar, and it links the timing to heightened regional tension and Iran’s temporary airspace closure during that period.
The practical risk is straightforward. If your cameras or NVRs sit on the public internet and still run old firmware, attackers can attempt authentication bypass, command injection, or remote code execution using known CVEs. Check Point says patches exist for every vulnerability it listed, so exposure and patching discipline will decide who gets hit next.
What researchers observed
Check Point says the attacking infrastructure combined commercial VPN exit nodes and VPS hosts. It specifically names Mullvad, ProtonVPN, Surfshark, and NordVPN as VPN providers seen in the infrastructure used for scanning.
Check Point’s findings also connect camera targeting to operational support and battle damage assessment concepts. It says monitoring camera-targeting from attributed infrastructure may serve as an early indicator of potential follow-on kinetic activity in some cases.

Targeted countries and activity windows
| What | What Check Point reported |
|---|---|
| Main spike | Began February 28, 2026 |
| Countries named | Israel, Qatar, Bahrain, Kuwait, UAE, Cyprus, Lebanon |
| Earlier activity | January 14–15 in Israel and Qatar |
| Vendor focus | Hikvision and Dahua only (from the tracked infrastructure) |
Vulnerabilities being scanned and exploited
Check Point mapped the activity to five known vulnerabilities spanning Hikvision and Dahua products.
| CVE | Vendor | Vulnerability type | Public description source |
|---|---|---|---|
| CVE-2017-7921 | Hikvision | Improper authentication | NVD |
| CVE-2021-36260 | Hikvision | Command injection in web server | NVD |
| CVE-2023-6895 | Hikvision | OS command injection | NVD |
| CVE-2025-34067 | Hikvision | Unauthenticated remote code execution | NVD |
| CVE-2021-33044 | Dahua | Authentication bypass | NVD |
Why Hikvision and Dahua deployments face outsized risk
These brands appear widely deployed in public spaces and commercial sites, which makes them attractive for real-time visual intelligence. Check Point says it did not see interaction attempts against other camera vendors from the same tracked infrastructure, which suggests deliberate targeting rather than random scanning.
Independent coverage adds context. The Register reports Check Point tracked “hundreds” of exploit attempts tied to these CVEs since hostilities began on February 28, based on an interview with a Check Point threat intelligence manager.
What organizations should do now
- Remove direct WAN exposure for cameras and NVRs. Put them behind a VPN or a zero-trust access gateway and block port forwards.
- Change default credentials and enforce unique passwords per device.
- Patch firmware and management platforms. Check Point says updates are available for all listed CVEs and it recommends replacing end-of-life devices that no longer receive fixes.
- Segment camera networks. Put cameras on a dedicated VLAN and block lateral access to corporate or OT networks. Limit outbound traffic to only required endpoints.
- Monitor for compromise signals like repeated login failures, unexpected remote logins, or unusual outbound connections initiated by camera systems.
Fast hardening checklist
| Control | Minimum bar | Better bar |
|---|---|---|
| Remote access | No public internet exposure | VPN or ZTNA with device posture checks |
| Credentials | Unique passwords, no defaults | Rotate credentials and store in a vault |
| Firmware | Patch all devices quarterly | Patch on vendor release plus exposure review |
| Network | VLAN isolation | Micro-segmentation plus egress allowlists |
| Monitoring | Auth failures and logins | Add flow monitoring for unexpected egress |
FAQ
Check Point says it observed intensified targeting from Iran-nexus infrastructure starting February 28, with patterns that may align with operational support and battle damage assessment concepts.
Check Point says it observed attempts against Hikvision and Dahua devices, and it did not observe interaction attempts against other camera vendors from the same infrastructure.
Yes. Check Point states patches are available for all five vulnerabilities it listed.
Remove public internet exposure for cameras and NVRs. That step cuts off the easiest path for scanning and exploitation attempts.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages