Threat Actors Use AI Tools for 30-Minute Domain Compromise in 2025

CrowdStrike 2026 Global Threat Report documents 89% increase in AI-enabled attacks. Average eCrime breakout time fell to 29 minutes with fastest at 27 seconds. Attackers weaponized Claude, Gemini, ChatGPT for credential theft and lateral movement.
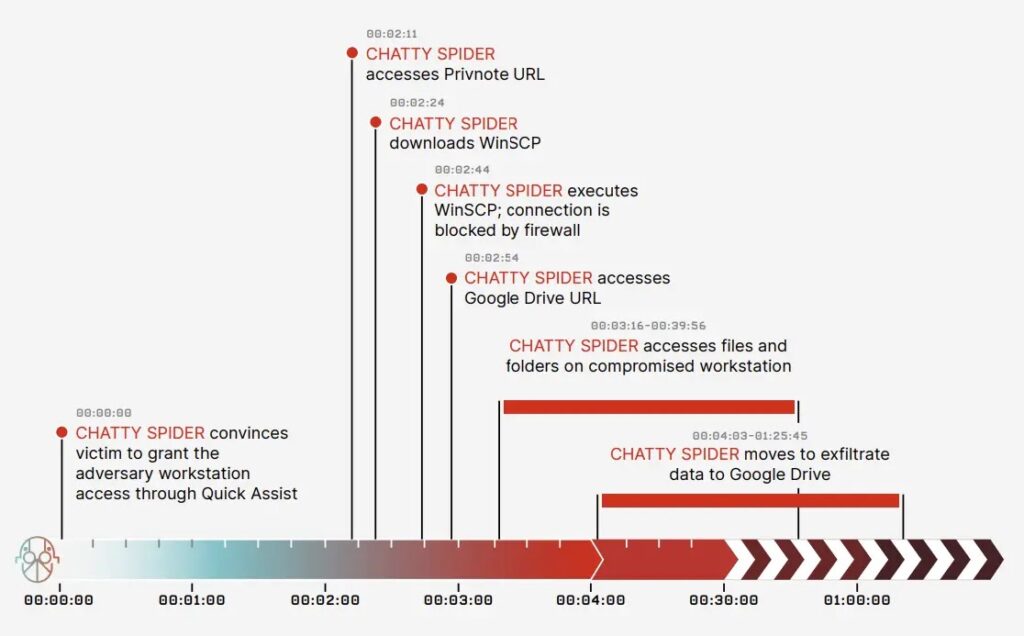
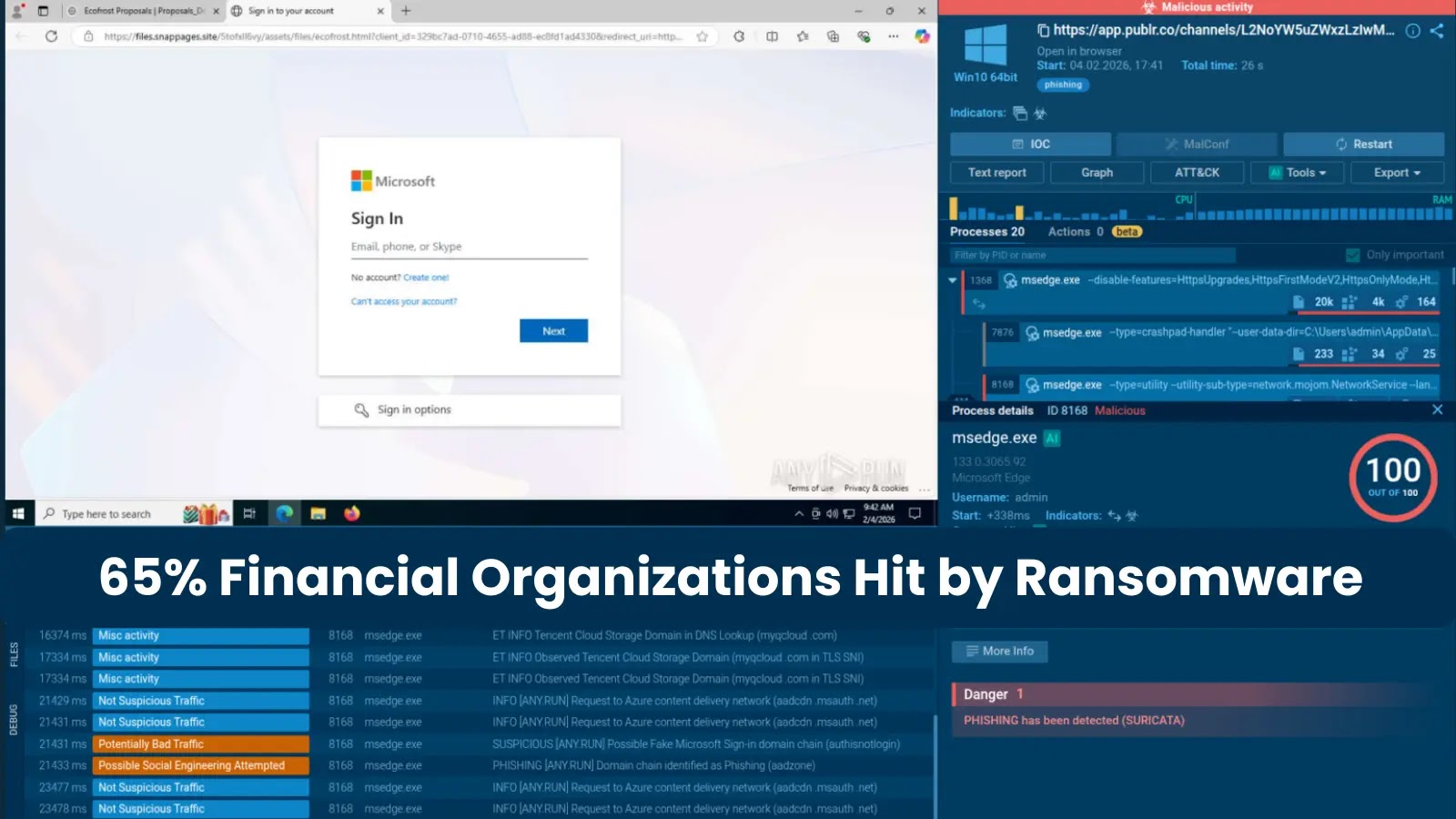
CHATTY SPIDER compromised U.S. law firm via Quick Assist vishing in 4 minutes. WinSCP exfiltration blocked, pivoted to Google Drive before OverWatch stopped data loss. PUNK SPIDER executed 198 ransomware intrusions using Gemini scripts.
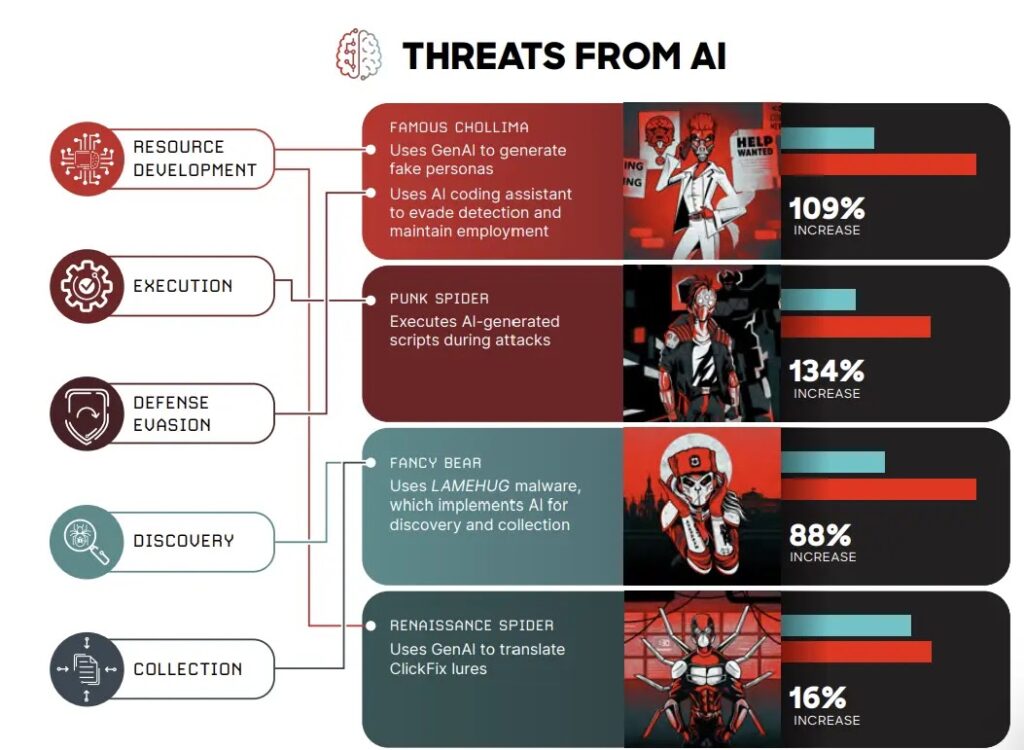
FAMOUS CHOLLIMA doubled activity creating fake personas via GitHub Copilot, VSCodium. AI-generated scripts dumped Veeam credentials and destroyed forensic evidence. 82% malware-free detections show authorized pathway abuse.
NPM packages embedded malicious JavaScript hijacking local AI instances. CrowdStrike responded to 90+ customers across campaigns. LAMEHUG malware queried Hugging Face Qwen2.5 for recon and document collection.
AI lowers barriers across entire kill chains from phishing to exfiltration. Static tools fail against dynamically generated payloads. Cross-domain visibility essential for sub-30 minute intrusions.
Threat Actor Activity Table
| Group | AI Usage | Impact |
|---|---|---|
| CHATTY SPIDER | Quick Assist vishing | 4-min exfiltration |
| PUNK SPIDER | Gemini scripts | 198 intrusions |
| FAMOUS CHOLLIMA | Copilot personas | 2x activity growth |
| FANCY BEAR | Qwen2.5 recon | Malware-free attacks |
AI Weaponization Tactics
- Malicious npm packages hijacking Claude/Gemini
- Gemini scripts dumping Veeam credentials
- ChatGPT generating fake personas
- Qwen2.5 LLM reconnaissance queries
- JIT compiler evasion via AI scripts
Endpoint AI monitoring detects anomalous prompt execution. NPM dependency scanning blocks malicious packages preemptively.
Defensive Requirements
- Cross-domain identity/cloud visibility
- AI tool usage endpoint monitoring
- npm package supply chain validation
- Sub-30 minute detection windows
- Behavioral anomaly detection rules
- Authorized pathway abuse hunting
Enterprises face AI-empowered attackers moving faster than defenses. Traditional malware signatures obsolete against 82% malware-free intrusions. Breakout time compression demands architectural response.
FAQ
27 seconds from initial access to lateral movement.
89% growth documented in 2025.
Claude, Gemini, ChatGPT, GitHub Copilot, Qwen2.5.
Microsoft Quick Assist vishing attack.
82% used authorized pathways exclusively.
90+ customers protected across campaigns.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages