To beat alert overload, security teams need fewer false positives, not more analysts
False positives may look harmless on paper, but they create a serious operational problem inside a security operations center. Every benign alert still takes analyst time, slows triage, and pushes real threats deeper into the queue. NIST defines a false positive as an instance in which a security tool incorrectly classifies benign content as malicious, while IBM describes alert fatigue as mental and operational exhaustion caused by too many alerts, many of them low priority or non-actionable.
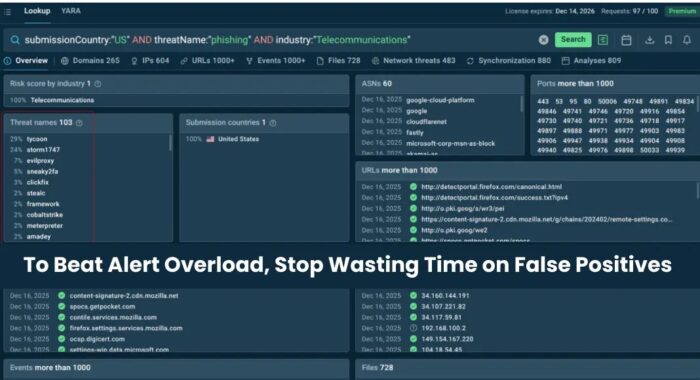
That broader problem is the focus of a new ANY.RUN piece arguing that better threat intelligence can reduce wasted SOC effort. The company says high-confidence, frequently updated threat intelligence feeds can help security teams improve alert quality, shorten investigations, and cut down on analyst burnout caused by noisy detections.
The central argument is straightforward. Security teams do not solve alert overload by hiring more people to investigate low-quality alerts. They solve it by improving the data and detection logic that create those alerts in the first place. That view lines up with wider industry understanding of alert fatigue, where excessive noise reduces visibility and weakens response quality over time.
Why false positives become a SOC problem
A single false alert rarely causes major damage on its own. The issue starts when hundreds or thousands of alerts arrive every day, and analysts must repeatedly investigate activity that turns out to be harmless. Over time, that routine creates a backlog, reduces investigation depth, and increases the chance that a real incident gets delayed or overlooked. IBM says alert fatigue grows when teams face an overwhelming number of alerts, especially those that lack actionability.
This is why false positives matter far beyond simple inefficiency. They can distort the entire detection pipeline. Analysts begin spending more time
validating whether an alert matters than responding to confirmed threats. As that cycle repeats, security teams lose trust in the systems designed to help them. NIST’s definition of false positives and broader industry guidance on mitigation both support the idea that poor signal quality creates unnecessary work that must be corrected elsewhere in the workflow.
What ANY.RUN is proposing
ANY.RUN says its Threat Intelligence Feeds are designed to improve detection quality by supplying fresh malicious IPs, domains, and URLs enriched with sandbox analysis. On its official product page, the company describes the feeds as real-time and “noise-free,” and says they are built for SIEM integration and threat hunting.
The company’s broader platform pitch follows the same theme. ANY.RUN says its Interactive Sandbox and threat intelligence tools help SOC teams analyze suspicious files and URLs quickly so they can handle more alerts and respond faster. On its enterprise page, the company also says it is trusted by more than 15,000 organizations, though that figure comes from the vendor itself and should be read as a company claim rather than an independently verified market total.
ANY.RUN also points to the scale of its ecosystem as part of the value proposition. Its recent annual report says the platform supports more than 500,000 cybersecurity professionals, while other company materials highlight thousands of SOC environments and large daily submission volumes. Again, those figures come from ANY.RUN’s own materials, but they help explain how the company positions its feeds as broad, current, and grounded in live analysis activity.
How stronger threat intelligence can reduce noise
The idea behind the pitch is not controversial. Better threat intelligence can reduce noise when it is fresh, validated, and rich in context. A weak feed filled with outdated or overly broad indicators may trigger on benign infrastructure and create unnecessary alerts. A higher-confidence feed can help narrow detection logic and cut down on irrelevant matches. That is also consistent with general alert fatigue guidance, which emphasizes tuning, validation, and reducing non-actionable signal.
ANY.RUN says its feeds gain precision because indicators come from confirmed malicious activity observed in sandbox detonations rather than passive aggregation alone. The company also says the feeds include context such as malware behavior and related intelligence that can speed up triage. If that works as advertised in a customer’s environment, it could reduce the time analysts spend starting investigations from zero.
That does not mean any threat intelligence feed is automatically low-noise in every stack. Results still depend on how teams integrate the data, tune their detections, and validate matches against their own environment. Even strong data can generate unwanted alerts if rules are too broad or context is ignored.
Where poor intelligence creates false positives
| Threat intelligence issue | How it creates noise | Why it hurts SOCs |
|---|---|---|
| Outdated indicators | Flags domains or IPs no longer linked to active attacks | Analysts waste time on stale matches |
| Limited context | Alert fires with no campaign or behavioral background | Triage takes longer |
| Overly broad IOC sets | Shared or legitimate infrastructure gets caught in detections | Benign activity looks suspicious |
| Slow update cycles | Threat data lags behind attacker changes | Teams investigate the wrong things |
| Weak validation | Low-confidence indicators reach production detections | False positives rise |
The table above reflects common detection engineering problems that security teams already understand well. ANY.RUN’s product messaging targets exactly these pain points by promising real-time, validated intelligence with behavioral enrichment.
Why hiring alone does not solve alert overload
Adding more analysts may help in the short term, but it does not fix the source of the noise. If the underlying detections remain weak, new hires simply spend more time doing repetitive triage. That raises cost without necessarily improving visibility. IBM’s overview of alert fatigue and broader mitigation guidance both point back to the same lesson: reducing irrelevant alerts matters just as much as staffing.
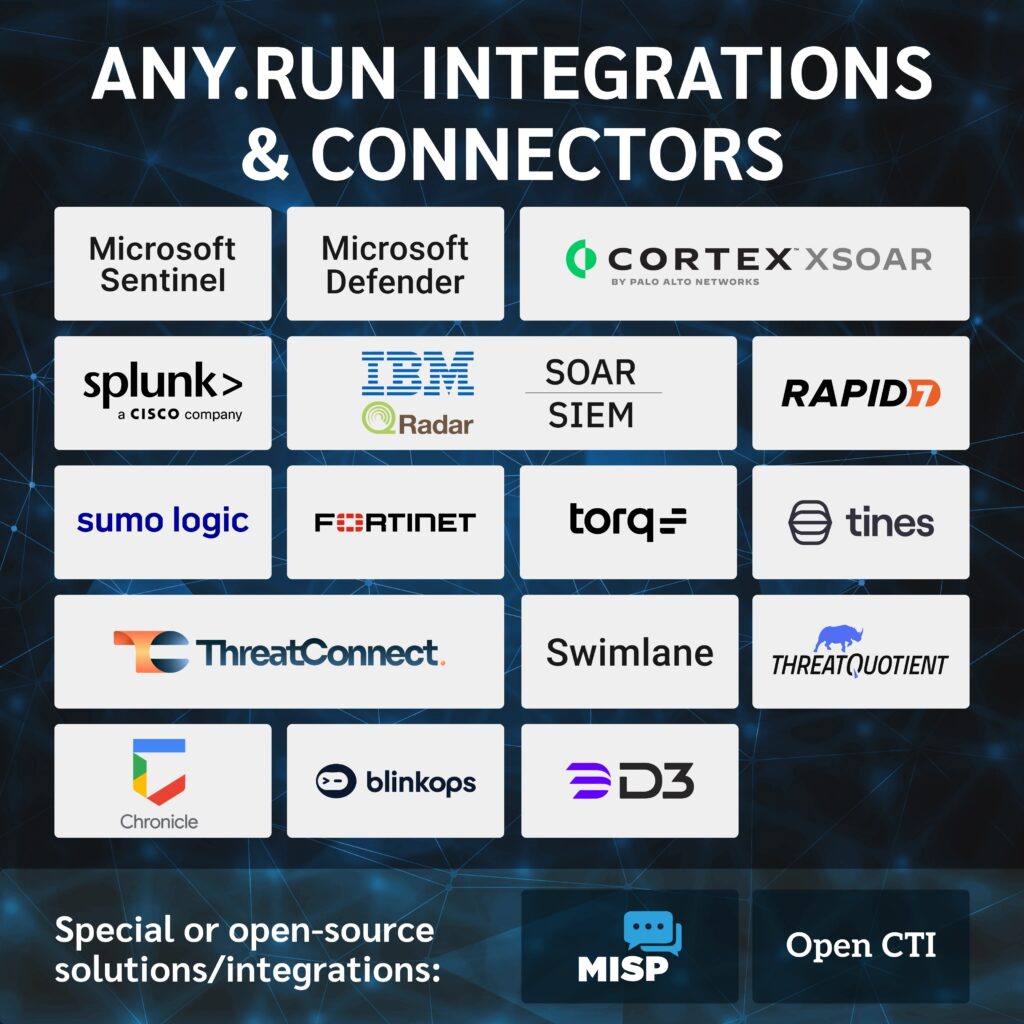
This is where better intelligence, better tuning, and tighter workflows meet. Security teams need to improve the quality of alerts entering the queue, not only the number of people reading them. ANY.RUN’s article frames its feeds as one way to support that shift, especially for teams already using SIEM, SOAR, and threat intelligence workflows.
What security teams should evaluate before buying into the pitch
Security leaders considering this approach should look beyond the marketing claim and ask practical questions:
- How fresh are the indicators in the feed?
- How much context comes with each IOC?
- Can the data be mapped cleanly into the existing SIEM or SOAR stack?
- How often do the indicators trigger on legitimate infrastructure in the organization’s own environment?
- How much analyst time does the feed actually save after deployment?
- Does the vendor show measurable reductions in triage time or false positive rates?
Those questions matter because alert overload is not solved by volume alone. It is solved by signal quality and operational fit. A feed that looks strong in a demo still needs to prove itself in production.
Bottom line
ANY.RUN is pushing a message that will resonate with many SOC leaders: false positives are not a minor annoyance, and alert overload cannot be fixed by hiring alone. The more important fix sits upstream in the quality of the intelligence and detections feeding the queue.
The company’s Threat Intelligence Feeds are built around that promise, with official claims centered on real-time, validated, context-rich indicators derived from sandbox analysis. Whether that delivers a meaningful reduction in false positives will depend on customer deployment and tuning, but the broader point is hard to dispute. Security teams need fewer low-value alerts and more confidence in the ones that remain.
FAQ
NIST defines it as an instance in which a security tool incorrectly classifies benign content as malicious. In practice, it means an alert fires even though there is no real threat to act on.
Because they consume analyst time, delay response to real incidents, and contribute to alert fatigue. IBM says alert fatigue happens when teams face too many alerts, especially low-priority or non-actionable ones.
ANY.RUN says its Threat Intelligence Feeds provide fresh malicious IPs, domains, and URLs enriched with sandbox analysis, with the goal of giving teams higher-confidence detections and less noise.
No. Better data can reduce them, but detection rules, environmental context, and integration choices still shape the final alert quality. Guidance on false positive reduction consistently points to tuning and validation as part of the answer.
Usually not. More staff can help with capacity, but it does not fix the underlying issue if poor detections keep flooding the queue with low-value alerts.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages