Trojanized OpenVSX extension spreads GlassWorm across VS Code, Cursor, and Windsurf
A fake OpenVSX extension that impersonates WakaTime can infect multiple VS Code-based editors on the same machine, not just the one where a developer installs it. Researchers at Aikido say the malicious extension, specstudio/code-wakatime-activity-tracker, bundles a native Zig-based binary that silently looks for other compatible editors and force-installs a second-stage malicious extension into them.
According to Aikido, the attack targets the wider VS Code extension ecosystem. The malware checks for Visual Studio Code, VS Code Insiders, Cursor, Windsurf, VSCodium, and Positron on both Windows and macOS, then uses each editor’s own command-line installer to push the payload across the machine.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The extension tries to look legitimate because it closely copies the real WakaTime workflow, including similar prompts and interface behavior. WakaTime’s official VS Code plugin is a genuine time-tracking extension, which likely helped the fake package blend in with normal developer activity.
How the malware works
Aikido says the malicious package changes the extension’s activate() flow so it loads a native binary before any expected WakaTime logic runs. On Windows that file appears as win.node, and on macOS it appears as mac.node, both built as native Node.js add-ons with direct operating system access.
After that, the binary downloads a malicious .vsix package from an attacker-controlled GitHub Releases page. Researchers say the downloaded package impersonates steoates.autoimport, a popular auto-import extension, and then gets installed silently into every supported editor the malware finds.
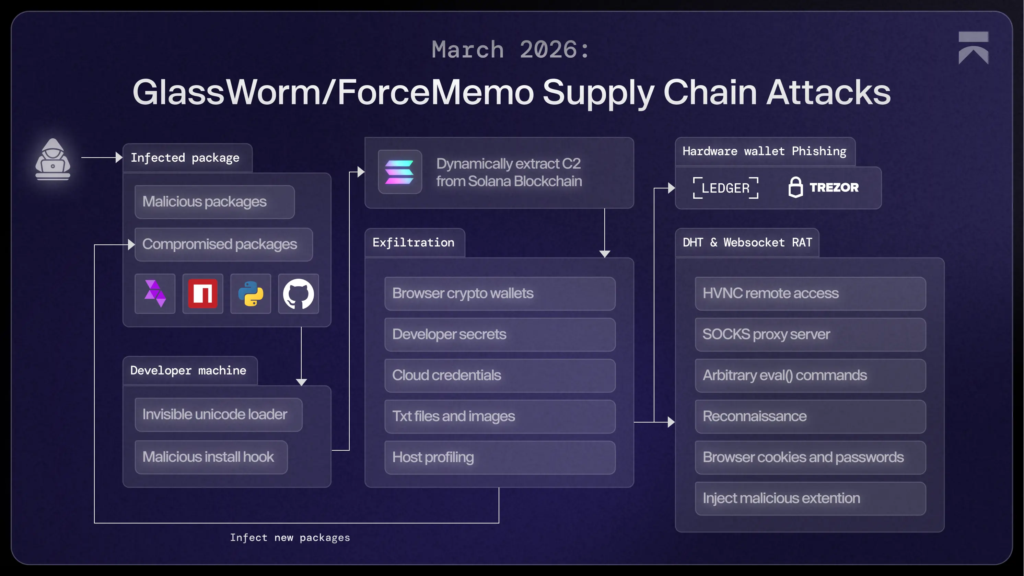
Aikido says the second-stage payload matches the broader GlassWorm campaign it has tracked since March 2025. In this latest version, the malware geofences Russian systems, retrieves command-and-control details through the Solana blockchain, exfiltrates data, and can install a persistent RAT along with a malicious Chrome extension.
Why this attack stands out
This campaign matters because it does not stay inside one editor session. A developer who installs the rogue extension in Cursor but also keeps VS Code or Windsurf on the same machine could end up with all of them quietly compromised.
It also shows how GlassWorm keeps evolving. Aikido says the campaign first appeared in March 2025 in malicious npm packages that hid payloads in invisible Unicode characters, and it later expanded across GitHub, npm, browser extensions, and VS Code-related ecosystems.
OpenVSX has already faced earlier GlassWorm incidents this year. In February, SecurityWeek reported that a hijacked Open VSX publisher account was used to push poisoned extensions tied to the same malware family, showing that attackers have kept coming back to this ecosystem.
What developers should check now
Aikido says anyone who installed specstudio/code-wakatime-activity-tracker or finds floktokbok.autoimport in any IDE should treat the machine as compromised. The firm also published file indicators including win.node and mac.node, plus the attacker GitHub Releases URL used to fetch the second-stage .vsix file.
Because this malware can reach browser data, development secrets, and other local information, the response should go beyond deleting one extension. Developers should assume exposed API keys, access tokens, browser sessions, and repository credentials may need rotation if the extension was installed or executed. That conclusion follows directly from Aikido’s analysis of exfiltration and persistence behavior.
I could not find a public statement from Eclipse Open VSX about this specific April 2026 case in the sources I checked. The most detailed public technical write-up available right now comes from Aikido, which discovered and analyzed the attack.
Incident summary
| Item | Details |
|---|---|
| Malicious extension | specstudio/code-wakatime-activity-tracker |
| Claimed disguise | Fake WakaTime-style productivity extension |
| Malware family | GlassWorm |
| Second-stage extension | floktokbok.autoimport / autoimport-2.7.9.vsix |
| Targeted editors | VS Code, VS Code Insiders, Cursor, Windsurf, VSCodium, Positron |
| Platforms mentioned | Windows and macOS |
| Notable behavior | Multi-IDE infection, Solana-based C2 lookup, data theft, RAT deployment |
Recommended actions
- Remove
specstudio/code-wakatime-activity-trackerfrom any installed editor. - Check every VS Code-compatible IDE on the same machine for
floktokbok.autoimport. - Look for
win.nodeormac.nodeinside suspicious extension folders. - Rotate API keys, tokens, SSH keys, and other secrets accessible from the affected system.
- Review browser sessions and sign out of critical services if the machine ran the payload.
- Audit connected repositories and recent commits for any unexpected changes.
FAQ
It is a malware campaign that Aikido says has moved across npm, GitHub, browser extensions, and editor ecosystems since March 2025. In this latest case, it uses a fake OpenVSX extension and a native dropper to spread across multiple IDEs on one machine.
Aikido lists VS Code, VS Code Insiders, Cursor, Windsurf, VSCodium, and Positron as targets because they share the VS Code extension format and support CLI-based extension installs.
Aikido says the presence of specstudio/code-wakatime-activity-tracker or floktokbok.autoimport should be treated as a full compromise signal.
The available reporting points to an impersonating OpenVSX package, not a compromise of WakaTime’s official VS Code plugin. WakaTime’s official plugin remains listed separately on its own site.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages