VIP Keylogger Malware Campaign Uses Steganography and Fileless Execution to Steal Credentials

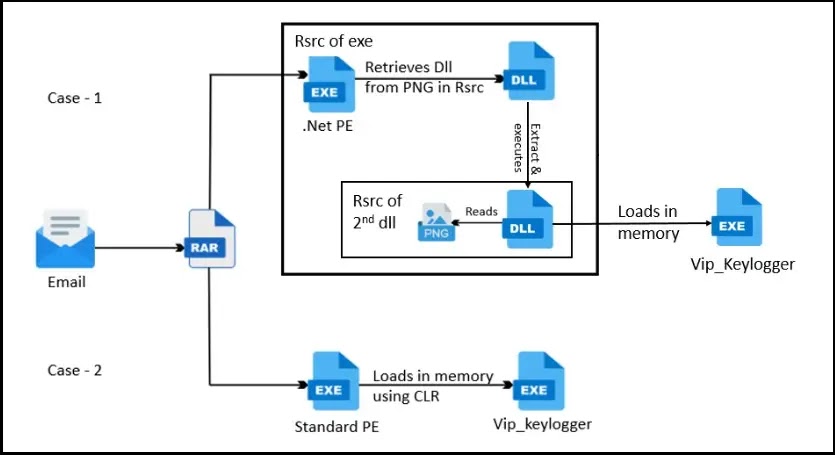
A large phishing campaign distributing VIP Keylogger malware is targeting organizations and individuals worldwide. Security researchers warn that the threat uses fileless techniques, steganography, and modular payloads to steal credentials from browsers, email clients, and messaging platforms.
Unlike traditional malware that installs visible files on a computer, this campaign executes the keylogger directly in memory, making detection significantly harder for standard antivirus tools. The malware spreads mainly through phishing emails that disguise malicious attachments as legitimate business documents.
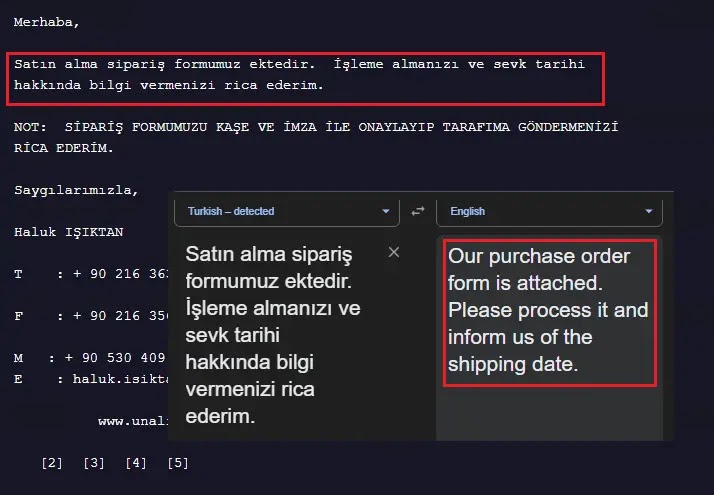
Researchers discovered the campaign after suspicious email samples appeared on VirusTotal. The phishing messages often include attachments that appear to be purchase orders or financial documents. When opened, the attachment launches the malware and begins harvesting sensitive data from the infected device.
Security analysts believe the operation may be linked to a Malware-as-a-Service (MaaS) model. This means the keylogger can be rented or customized by different attackers, allowing cybercriminals with limited technical knowledge to launch credential-stealing campaigns.
How the VIP Keylogger phishing attack begins
The attack starts with spear-phishing emails designed to trick users into opening a compressed attachment.
In many cases, the email contains a RAR archive disguised as a business document. Inside the archive is an executable file with a name that resembles a spreadsheet or invoice.
Once the victim runs the file, the malware loads the keylogger payload directly into memory, avoiding traditional file-based detection.
Typical infection chain
- Phishing email pretending to contain a purchase order or invoice
- RAR or ZIP attachment included in the message
- Executable disguised as a document
- Malware loads the keylogger payload in memory
- Credentials and data are extracted from the system
This type of delivery method is effective because many users still trust email attachments that appear to come from business partners.
Malware capabilities and data targets
Once the keylogger runs on an infected system, it begins collecting a wide range of sensitive information.
The malware specifically targets browsers, email software, and communication platforms that commonly store credentials or tokens.
Data types collected by VIP Keylogger
| Target Category | Examples | Data Stolen |
|---|---|---|
| Web browsers | Chrome, Edge, Brave, Opera | Saved passwords, cookies, credit card details |
| Mozilla applications | Firefox, Thunderbird, Waterfox | Login credentials and browsing data |
| Email clients | Outlook, Foxmail, Postbox | POP3, IMAP, SMTP passwords |
| Communication apps | Discord, Pidgin | Tokens and account data |
| FTP tools | FileZilla | Server credentials |
The malware extracts browser passwords by accessing encryption keys stored on the system and decrypting them using Windows APIs or browser security libraries.
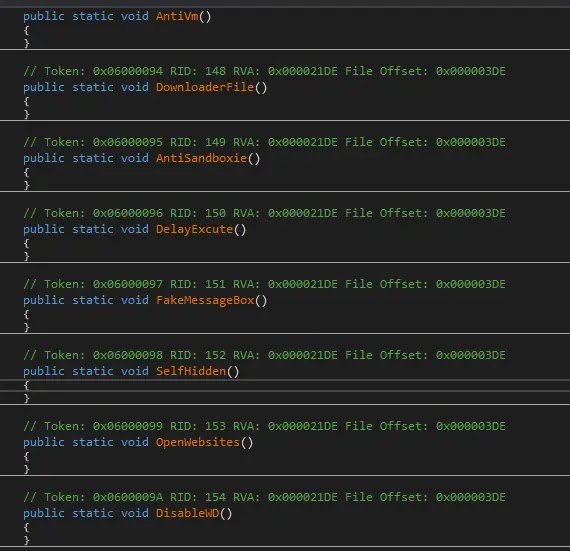
Advanced evasion techniques used in the campaign
VIP Keylogger uses multiple techniques to bypass security detection and operate quietly inside infected systems.
1. Steganography
Attackers hide malicious payloads inside seemingly harmless files such as images. The malware retrieves the hidden code at runtime.
2. Process hollowing
The malware launches a legitimate system process in suspended mode and replaces its memory with malicious code.
3. Fileless execution
Instead of writing files to disk, the payload runs entirely in system memory.
4. Security bypass
Some variants disable Windows security mechanisms such as AMSI and ETW before executing the keylogger.
These techniques make the malware difficult to detect using traditional signature-based antivirus solutions.
Data exfiltration methods used by attackers
After collecting credentials and other sensitive information, the malware sends the stolen data to attacker-controlled infrastructure.
Common exfiltration channels
- SMTP email servers
- FTP servers
- Telegram bots
- Discord webhooks
- HTTP POST requests
Researchers observed that some samples send stolen credentials through SMTP servers using port 587, which helps attackers retrieve the information remotely.
Signs of a VIP Keylogger infection
Security teams should watch for the following indicators that may suggest the malware is present:
- Suspicious email attachments disguised as invoices or purchase orders
- Unknown processes spawning legitimate Windows executables
- Unusual outbound traffic through SMTP or FTP
- Security tools failing to log suspicious script activity
Organizations that detect these behaviors should investigate affected machines immediately.
How organizations can reduce the risk
Security experts recommend several defensive steps to protect against phishing-based malware campaigns.
Recommended protections
- Avoid opening attachments from unknown or suspicious email senders
- Use endpoint detection tools that monitor memory-based attacks
- Deploy email filtering to block suspicious archives and executables
- Keep browsers and applications fully updated
- Train employees to recognize phishing attempts
Modern endpoint detection and response systems can identify process injection and memory manipulation behavior used by this malware.
FAQ
VIP Keylogger is a credential-stealing malware designed to capture keystrokes, browser credentials, cookies, and account tokens from infected systems.
The malware spreads mainly through phishing emails containing malicious attachments disguised as invoices, purchase orders, or financial documents.
The keylogger runs in system memory rather than installing files on disk. This technique allows it to bypass many traditional antivirus tools.
It can steal browser passwords, credit card information, email credentials, chat application tokens, and FTP server details.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages