VIPERTUNNEL hides in a fake DLL and turns Python into a stealthy SOCKS5 backdoor

A newly detailed malware campaign shows how attackers can turn a normal Python runtime into a quiet persistence and tunneling tool on Windows. InfoGuard Labs says the backdoor, called VIPERTUNNEL, hides behind a layered loader chain, abuses Python startup behavior, and ultimately gives attackers a SOCKS5 proxy channel into compromised networks.
The most interesting part is not just the backdoor itself. The infection chain uses a scheduled task that launches pythonw.exe without arguments, then relies on a tampered sitecustomize.py file to trigger malicious code every time the interpreter starts. That design avoids suspicious command-line artifacts and helps the malware blend into legitimate Python behavior.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
InfoGuard says it found VIPERTUNNEL during a ransomware incident response case in early 2026 after spotting an unusual scheduled task. The researcher then traced execution from the task to sitecustomize.py, then to a file named b5yogiiy3c.dll that was not a real DLL at all, but a Python script disguised with a DLL extension.
How the loader chain works
According to InfoGuard Labs, the malware starts with a scheduled task that repeatedly launches a local copy of pythonw.exe from C:\ProgramData\cp49s\. Because Python automatically imports sitecustomize.py at startup when present in the environment, the attackers used that hook for silent execution.
From there, the modified startup file checks that Python was launched without command-line arguments and then loads the fake DLL file through Python logic. InfoGuard says this “DLL” contains several obfuscation layers, including encoding, encryption, and control-flow flattening, with each stage decrypting the next one in memory.
The final payload is a Python backdoor built around three classes named Wire, Relay, and Commander. InfoGuard says those components handle C2 communication and SOCKS5-style relaying, which lets the malware act as a stealthy pivot point for further activity inside the victim network.
Why this malware is hard to spot
VIPERTUNNEL does not need a normal Windows EXE payload to stay active. It hides inside Python’s own startup flow, uses pythonw.exe to avoid a visible console window, and keeps much of its execution inside memory after the initial handoff. That makes it more annoying to investigate than a standard dropped backdoor.
InfoGuard also says the malware communicates outbound over port 443, which helps it blend into normal encrypted web traffic. That does not make it invisible, but it does reduce the odds that defenders will catch it through simple allowlist logic or casual network review.
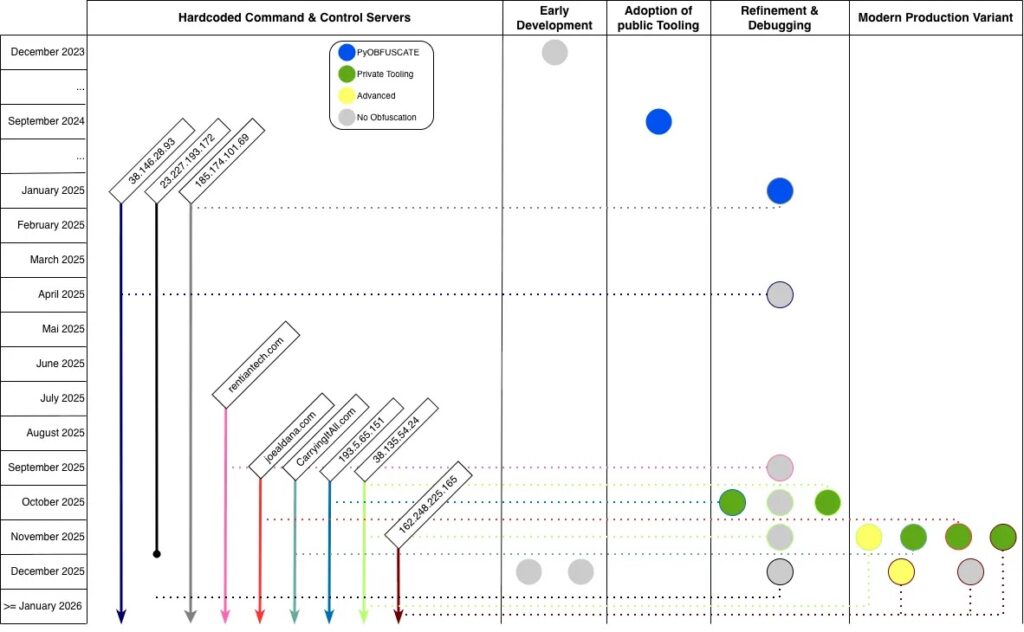
The same research links the obfuscation framework behind VIPERTUNNEL to another Python malware family called ShadowCoil, a browser credential stealer. InfoGuard presents that shared obfuscation and development history as evidence that both tools are related, though the actor attribution should be treated more carefully than the code-level overlap.
Attribution needs careful wording
InfoGuard includes an attribution section in its April 9 write-up and discusses links between VIPERTUNNEL, ShadowCoil, and activity associated with UNC2165. Separately, Google Cloud’s Mandiant has previously described UNC2165 as a financially motivated cluster with overlaps to Evil Corp.
What that does not prove on its own is that every VIPERTUNNEL sample should be stated as definitively “Evil Corp malware” without qualification. The strongest supported wording is that InfoGuard sees clustering ties and overlap with activity linked to UNC2165, while Mandiant has connected UNC2165 to broader Evil Corp overlaps.
That distinction matters because loader reuse, packer reuse, and shared infrastructure patterns can support clustering, but they do not always justify absolute actor claims in a headline.
Key technical details
| Item | Verified detail |
|---|---|
| Malware family | VIPERTUNNEL |
| Platform | Windows host using Python runtime |
| Persistence | Scheduled task plus tampered sitecustomize.py |
| Disguise | Fake .dll file that is actually a Python script |
| Function | SOCKS5 proxy backdoor / network pivot |
| Evasion | Multi-layer obfuscation, in-memory handoff, port 443 traffic |
| Related malware | ShadowCoil |
| Research source | InfoGuard Labs, April 9, 2026 |
The technical details above come from InfoGuard’s original malware analysis.
What defenders should look for
pythonw.exelaunched by a scheduled task with no arguments.- Unexpected
sitecustomize.pyfiles outside normal Python deployment paths. - Fake DLL filenames that are actually Python loaders or scripts.
- Python processes making unusual outbound connections over port 443.
- Hunting for class names such as
Wire,Relay, andCommander, or the error stringConnectionTimeoutOccuredError, which InfoGuard says can support detection.
FAQ
Not exactly. InfoGuard says the file posing as a DLL was actually a Python script using a .dll extension to mislead analysts and tools.
It creates a SOCKS5 proxy tunnel to attacker-controlled infrastructure, which can give operators persistent access and a way to relay traffic deeper into the victim environment.
sitecustomize.py? Python can load sitecustomize.py automatically during startup, so attackers can use it as a quiet persistence hook without putting a suspicious script path on the command line.
The safest phrasing is that InfoGuard sees links to activity associated with UNC2165, and Mandiant has previously said UNC2165 overlaps with Evil Corp. That is stronger than a vague rumor, but still more careful than calling every sample directly confirmed Evil Corp malware.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages