VoidStealer uses a new debugger trick to steal Chrome’s master key

VoidStealer is using a newer and quieter method to bypass Chrome’s Application-Bound Encryption, or ABE, and steal the browser’s v20_master_key from memory. Researchers at Gen Digital say this is the first infostealer they have seen in the wild using a debugger-based ABE bypass built around hardware breakpoints, instead of the noisier methods that usually rely on privilege escalation or code injection.
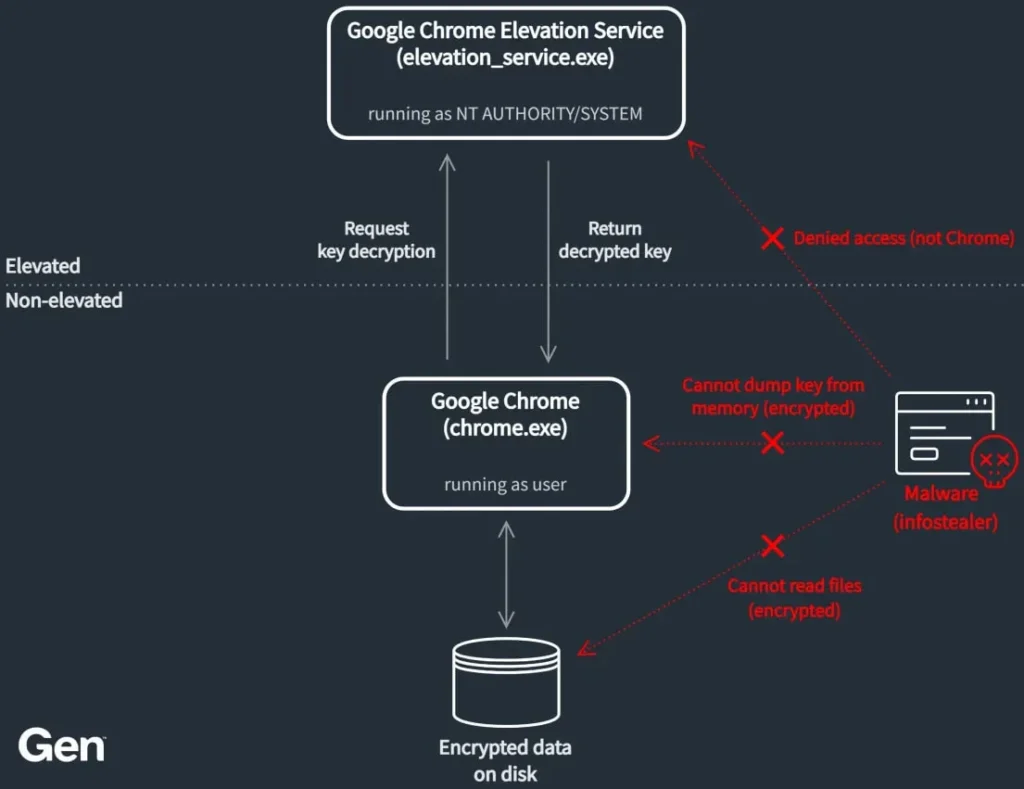
That matters because Chrome introduced ABE in Chrome 127 to make cookie and credential theft harder on Windows. Google said the feature ties encrypted data to the app’s identity and forces decryption through a privileged service, which raised the cost for attackers and made common theft attempts easier to detect.
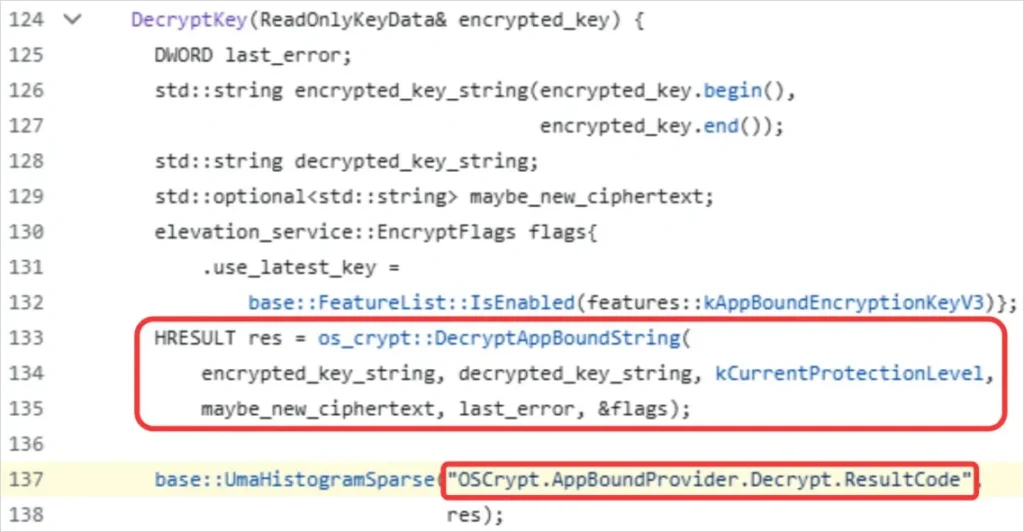
Gen Digital says VoidStealer still finds a way in by waiting for the brief moment when Chrome holds the master key in plaintext during startup and decryption. Instead of injecting code into the browser, the malware attaches as a debugger, sets hardware breakpoints at the right spot, and reads the key from memory when the target instruction runs.
What happened
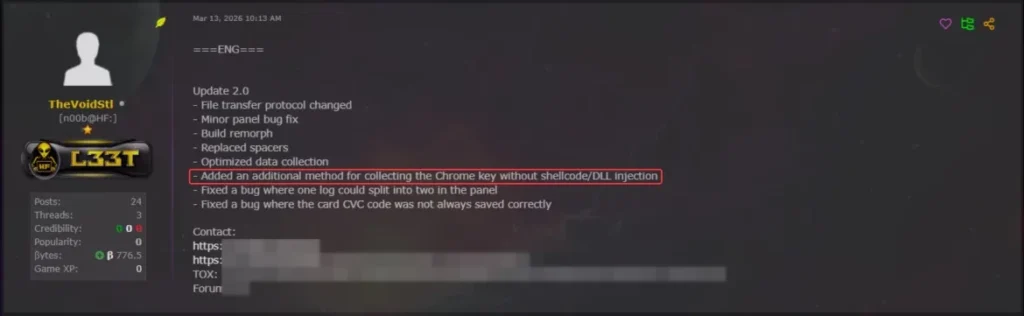
Researchers traced the technique to VoidStealer version 2.0, which Gen says introduced the debugger-based ABE bypass on March 13, 2026. The malware has been marketed as a malware-as-a-service offering since mid-December 2025 and has seen rapid version updates since then.
Google’s original design for ABE assumed attackers would need system privileges or direct injection into Chrome to get past the protection. Gen says VoidStealer lowers that footprint by relying on debugger attachment and ReadProcessMemory, which can look less suspicious than direct process injection in some environments.
Source: Gen Digital
Why this Chrome bypass stands out
This bypass does not mean ABE failed completely. Chrome’s protection still raised the barrier and forced attackers toward more specialized tradecraft. But the VoidStealer case shows that threat actors keep adapting, especially when public proof-of-concept work already demonstrates parts of the attack path. Gen says the implementation appears to be adapted from the open-source ElevationKatz project, though VoidStealer is the first malware family the company has seen use this specific debugger-based method in real attacks.
Google has also kept hardening ABE after launch. In Chromium’s security updates, the company said it shipped several improvements to app-bound encryption, including process-bound encryption to better resist local memory inspection, plus other mitigations and reliability fixes. Chromium also said it is rolling out a mitigation that prevents abuse of the local DevTools debugging API for credential theft.
Source: Gen Digital
VoidStealer at a glance
| Item | Details |
|---|---|
| Malware family | VoidStealer |
| Type | Infostealer / MaaS |
| Key technique | Debugger-based bypass of Chrome ABE |
| Main target | Chrome and Chromium-based browser secrets |
| What it steals | v20_master_key, which enables decryption of protected browser data |
| Why researchers care | It avoids privilege escalation and code injection |
| First observed in this form | VoidStealer v2.0, reported March 13, 2026 |
| Research source | Gen Digital |
How the attack works
The attack works by timing memory access during browser startup, when Chrome decrypts protected data and briefly handles the master key in plaintext. Gen says VoidStealer performs the following steps:
- Launches a hidden, suspended browser process.
- Attaches to that process as a debugger and waits for the target browser DLL to load.
- Scans for a target string and identifies the instruction tied to it.
- Sets hardware breakpoints on that instruction across browser threads.
- Waits for Chrome to decrypt protected data during startup.
- Reads the register that points to the plaintext
v20_master_key. - Extracts the key with
ReadProcessMemory.
Why users and admins should care
If attackers obtain the master key, they can decrypt sensitive browser data that ABE was supposed to protect more effectively on disk. Google introduced ABE specifically because traditional Windows DPAPI protections did not stop malicious code running as the logged-in user from accessing that data.
For enterprise defenders, this case is a reminder that browser protection alone is not enough. Google said ABE was designed to make attacker behavior louder and easier for defenders to spot, and Chrome emits related events such as Event ID 257 on failed verification attempts. Gen’s research adds that newer bypasses may trade brute force for stealth, which makes detection engineering and endpoint visibility even more important.
Source: Gen Digital
What has changed on Google’s side
Google has not published a dedicated public response to VoidStealer as of the sources reviewed here. Still, the broader Chromium security updates show that Google has continued strengthening app-bound encryption after launch, including memory-inspection hardening and debugging-related mitigations. That suggests the company treats local browser data theft as an active and evolving threat area.
What defenders can do now
- Keep Chrome and other Chromium-based browsers fully updated.
- Monitor for suspicious debugger attachment to browser processes.
- Watch for unusual use of
ReadProcessMemoryagainst Chrome or Edge. - Restrict local admin rights wherever possible.
- Review endpoint rules for browser process tampering and credential theft behavior.
- Check Chrome-related Windows event logs in managed environments.
FAQ
VoidStealer is an infostealer sold as malware-as-a-service. Gen Digital says it has been advertised since mid-December 2025 and gained a new ABE bypass in version 2.0.
It is a Windows protection added in Chrome 127 that ties encrypted browser data to the app’s identity, so other apps running as the same user cannot easily decrypt it.
Gen says it avoids two common red flags: privilege escalation and code injection. Instead, it uses debugger attachment and hardware breakpoints to capture the key from memory.
No. Chrome’s ABE still made theft harder and pushed attackers toward more advanced methods. But this case shows that browser protections need constant updates because infostealers keep adapting.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages