Web server exploits and Mimikatz linked to years-long attacks on Asian critical sectors

A newly detailed cyber campaign has targeted high-value organizations across South, Southeast, and East Asia by exploiting internet-facing web servers, planting web shells, stealing credentials, and moving deeper into both Windows and Linux environments. Palo Alto Networks Unit 42 says the activity cluster, tracked as CL-UNK-1068, hit aviation, energy, government, law enforcement, pharmaceutical, technology, and telecommunications organizations, and it assesses with high confidence that the attackers are a Chinese threat actor.
Unit 42 also says the campaign appears geared mainly toward cyber espionage. The researchers describe a toolset built around custom malware, modified open-source tools, and living-off-the-land binaries, which helped the attackers keep long-term access while blending into normal activity.
The report stands out because it tracks the activity back to at least 2020 and shows a practical, low-noise intrusion style rather than one flashy malware family. In many cases, the attackers appear to have started with web server exploitation, deployed web shells such as Godzilla and AntSword, then collected sensitive files, credentials, and host data from compromised systems.
What happened
According to Unit 42, a typical intrusion chain began with the exploitation of a web server, followed by web-shell deployment and lateral movement to additional hosts. The attackers then looked for files such as web.config, .aspx, .asmx, .asax, and .dll under c:\inetpub\wwwroot on Windows web servers, likely to steal credentials, understand the application environment, or uncover additional weaknesses.
The group also collected browser history and bookmarks, XLSX and CSV files from user directories, and .bak database backup files from Microsoft SQL Server systems. That mix suggests an operator looking for credentials, internal documentation, and business data that can support long-term intelligence collection.
One of the more unusual details in the report involves exfiltration. Unit 42 says the attackers sometimes archived stolen files with WinRAR, encoded the archive with certutil -encode, and then used the type command to print the Base64 output to the screen through a web shell. That let them extract data in text form even when the shell did not support direct file transfer.
Why Mimikatz matters here
Mimikatz remains one of the most recognized post-compromise tools because it can dump passwords and other secrets from memory on Windows systems. In this campaign, Unit 42 says CL-UNK-1068 used Mimikatz alongside LsaRecorder, DumpItForLinux, Volatility, and a SQL Server Management Studio password export tool to collect credentials across both Windows and Linux environments.
That behavior fits a broader trend in modern intrusions. CISA and partner agencies warned in 2024 that living-off-the-land techniques and abuse of legitimate admin tools make attacks harder to detect because the activity can resemble normal system behavior. Those same agencies also highlighted credential access, reconnaissance, persistence, and lateral movement as common goals in stealthy post-exploitation operations.
Tools and techniques seen in the campaign
| Area | Tools or methods Unit 42 described | Why it matters |
|---|---|---|
| Initial access and foothold | Web server exploitation, Godzilla, AntSword | Lets attackers gain a quiet foothold on exposed servers |
| Credential theft | Mimikatz, LsaRecorder, DumpItForLinux, Volatility, SSMS password export tool | Helps attackers move laterally and access sensitive systems |
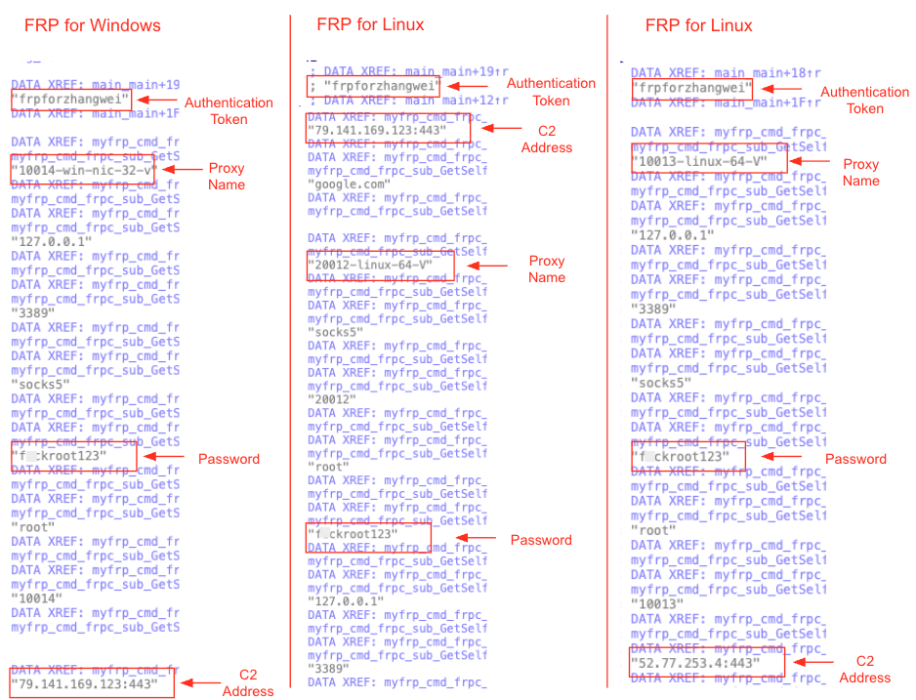
| Persistence and tunneling | Fast Reverse Proxy, DLL side-loading, legitimate Python executables | Gives long-term remote access while masking malicious execution |
| Reconnaissance | SuperDump, batch scripts, custom scanner ScanPortPlus | Maps hosts, services, and local environment for next-stage actions |
| Exfiltration | WinRAR, certutil encoding, command-line output via web shell | Moves data out in a way that may avoid simpler transfer controls |
Why critical infrastructure should pay attention
This campaign did not rely on a single rare zero-day or one signature-heavy backdoor. It leaned on web exploitation, web shells, open-source tools, credential theft, and legitimate binaries. That makes the activity more repeatable and harder to spot, especially in organizations with large server estates and uneven logging.
The cross-platform angle also matters. Unit 42 says the operators maintained different tool variants for Windows and Linux, which is important for sectors like telecom, energy, and government where mixed environments are common. When one actor can pivot across web servers, endpoints, databases, and Linux systems with the same campaign logic, defenders need visibility across the whole estate, not only Windows endpoints.
What defenders should do now
- Audit internet-facing web servers for shells, suspicious scripts, and unusual file access patterns around application directories such as
inetpub\wwwroot. - Hunt for credential-dumping behavior tied to Mimikatz, LSA hooking, memory capture, and unusual access to SSMS credential stores.
- Watch for living-off-the-land activity involving
certutil,type, compression utilities, Python executables, and DLL side-loading chains. - Review outbound tunnels, FRP-like behavior, and long-lived remote access paths that do not match approved administration workflows.
- Segment critical systems and tighten access between web tiers, database servers, and user endpoints so a compromised server cannot easily become a pivot point.
Big picture
The most important takeaway is not just that Mimikatz showed up again. It is that a long-running threat cluster appears to have combined ordinary web compromises with patient credential theft and quiet data collection against strategically important sectors in Asia. That combination makes the campaign dangerous because it does not need to look exotic to be effective.
For defenders, this report reinforces a familiar lesson. If an exposed web server falls, the incident may not stay confined to the web tier for long. The follow-on risk often comes from the tools attackers use after initial access, especially the ones that look legitimate at first glance.
FAQ
Palo Alto Networks Unit 42 says it assesses with high confidence that CL-UNK-1068 is a Chinese threat actor. It also says the main objective is likely cyber espionage, though it does not fully rule out cybercriminal motives.
Unit 42 lists aviation, energy, government, law enforcement, pharmaceutical, technology, and telecommunications organizations across South, Southeast, and East Asia.
The report says typical attack chains began with web server exploitation, followed by web shells, lateral movement, credential theft, and data collection.
Because it remains a practical tool for credential dumping after initial compromise. In this campaign, it was part of a broader credential-theft toolkit that helped the attackers move inside victim environments.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages