WhatsApp Account Password Adds Third Security Layer Against SIM Swaps

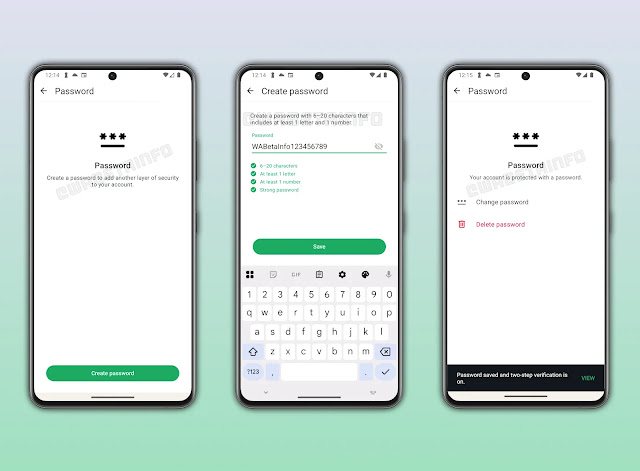
WhatsApp beta version 2.26.7.8 introduces optional account passwords atop SMS and 2FA verification. Alphanumeric passwords (6-20 characters with letter+number) create three-factor barriers stopping SIM swap attacks completely. Strength meter guides robust choices. Users control enable/disable anytime.
Current flow requires 6-digit SMS code after phone registration. Optional 2FA PIN adds secondary check. Email backup recovers SIM-unreachable accounts since 2.23.24.10.
New password triggers post-SMS or post-2FA. Single password setups prompt after SMS only. Full three-factor demands SMS → 2FA PIN → password sequence. Attackers need all three factors simultaneously.
SIM swappers grab SMS codes via carrier bribes. 2FA PINs leak through phishing occasionally. Password remains user-only knowledge blocking final access layer.
Strength evaluation prevents weak choices. Real-time feedback pushes complexity. Full flexibility allows instant removal or updates matching user risk tolerance.
Two billion users face daily account takeover attempts. Enterprise chats, family groups, and personal messages demand layered protection. Optional rollout respects varying threat models globally.
Authentication Flows Table
| Setup | Login Sequence | Attack Resistance |
|---|---|---|
| SMS Only | 6-digit code | SIM swap vulnerable |
| SMS + 2FA | Code → PIN | Phishing risk |
| SMS + Password | Code → Password | Strong protection |
| Full Triple | Code → PIN → Password | Maximum security |
Beta testing refines UX before stable release. Gradual rollout follows completion. Google Play Beta users test first.
Password integrates final login step seamlessly. No app restart needed post-setup. Biometric unlock potential exists for future iterations.
SIM Swap Protection Impact
Attackers compromise SMS via social engineering at carriers. 2FA PINs extract through fake verification screens. Password survives both vectors completely.
Enterprise deployments gain compliance value. GDPR, HIPAA demand multi-factor beyond SMS. Triple auth satisfies strictest regimes automatically.
Consumer adoption hinges on frictionless UX. Optional nature preserves accessibility. Power users enable full stack immediately.
Setup Benefits
- Blocks SIM swap + phishing combinations
- Enterprise-grade three-factor compliance
- User-controlled enable/disable anytime
- Strength meter prevents weak passwords
- No mandatory rollout preserves choice
Two billion accounts secure incrementally. Beta feedback shapes final implementation. Widespread account takeovers drop post-launch significantly.
Phishing kits evolve targeting 2FA gaps currently. Password layer forces redesign entirely. Attack economics suffer under triple barriers.
FAQ
6-20 alphanumeric with minimum one letter, one number.
No. Adds third layer atop SMS + 2FA for maximum protection.
Yes. Full control to enable/disable anytime through settings.
Android 2.26.7.8 via Google Play Beta Program.
Yes. Attackers need password even with SMS + 2FA PIN access.
Post-beta testing. Gradual stable deployment follows.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages