Windows Error Reporting ALPC Zero-Day: CVE-2026-20817 PoC Enables Local Privilege Escalation
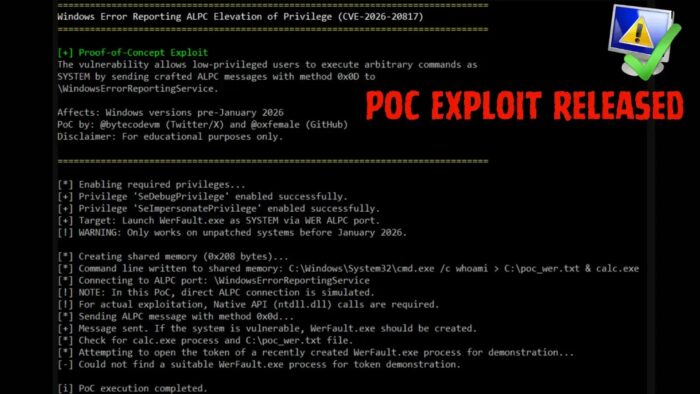
A critical local privilege escalation flaw in Windows Error Reporting (WER) service now has a public PoC exploit. Known as CVE-2026-20817, it lets low-privileged users run code as SYSTEM. Security researcher @oxfemale released the C++ exploit on GitHub.
The issue sits in WER’s ALPC port, named \WindowsErrorReportingService. It handles inter-process talks. The SvcElevatedLaunch method, or 0x0D, skips user permission checks. Attackers supply bad command lines via shared memory. WER then spawns WerFault.exe with those, gaining SYSTEM rights.
No complex setup needed. The PoC connects to the port and sends crafted messages. WerFault inherits high privileges like SeDebugPrivilege and SeImpersonatePrivilege. This opens full system control, though not full TCB access.
Researcher Said: “Public PoC for CVE-2026-20817 demonstrates full SYSTEM access via WER ALPC. Patch now.”
Vulnerability Overview
| Feature | Details |
|---|---|
| CVE ID | CVE-2026-20817 |
| Type | Local Privilege Escalation (LPE) |
| Affected Service | Windows Error Reporting (WER) |
| Key Method | SvcElevatedLaunch (0x0D) |
| Patch Date | January 2026 Security Update |
| Impact | Arbitrary code as SYSTEM |
It hits Windows 10, Windows 11 pre-January 2026, and Servers 2019/2022. Red teams test it now. Defenders must watch for odd WerFault spawns.
Exploit Steps
- Set up shared memory with malicious command.
- Link to WER ALPC port locally.
- Fire method 0x0D message with process ID, memory handle, command length.
- WER runs WerFault.exe as SYSTEM.
Post-exploit, attackers debug processes or impersonate users. Full compromise follows fast in unpatched setups.
Detection and Defense
Monitor for these signs:
- WerFault.exe with strange child processes.
- SYSTEM tokens on low-priv apps.
- ALPC traffic spikes to WER port.
Patch at once with January 2026 updates. Block untrusted shared memory access. Run endpoint tools with behavior alerts on privilege jumps.
FAQ
WER ALPC flaw allowing LPE to SYSTEM via bad validation.
@oxfemale on GitHub.
Windows 10/11 before Jan 2026, Servers 2019/2022.
Apply January 2026 patches; monitor WerFault.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages