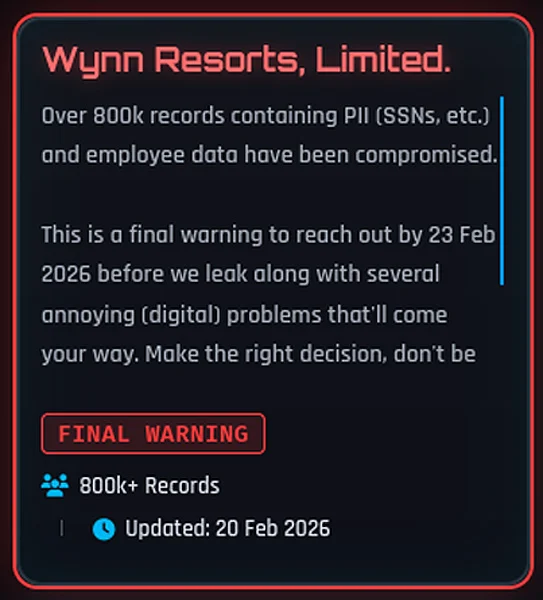
Wynn Resorts Confirms ShinyHunters Employee Data Breach After Extortion Listing

Wynn Resorts acknowledged unauthorized access to employee data following ShinyHunters extortion threat. Company activated incident response hiring external cybersecurity experts immediately. Attackers claimed 800K records with SSNs before February 23, 2026 deadline. Official statement confirmed data deletion claims by threat actors.
External experts verified no evidence of publication or misuse to date. Employee credit monitoring and identity protection offered complimentary. Guest operations and physical properties remained fully operational throughout incident.
ShinyHunters listing appeared then vanished from extortion site rapidly. Past patterns suggest negotiation activity or disputed claims. Company declined comment on ransom payment status to BleepingComputer.
Oracle PeopleSoft environment cited as breach source by attackers. Vishing campaigns targeted SSO accounts at Google, Microsoft, Okta previously. Device code phishing harvested Entra authentication tokens recently.
ShinyHunters February spree hit Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, Match Group. Salesforce OAuth token abuse stole customer data across enterprises last year. Credential stuffing combines multiple leaks amplifying fraud potential.
ShinyHunters February Victims Table
| Company | Data Type | Status |
|---|---|---|
| Wynn Resorts | Employee PII/SSNs | Confirmed |
| Panera Bread | 51M accounts | Leaked |
| Betterment | 14M accounts | Leaked |
| SoundCloud | 298M accounts | Leaked |
| Canada Goose | 600K customers | Leaked |
Attack Infrastructure Targets
- SSO platforms: Google, Microsoft, Okta
- SaaS applications: Salesforce, M365, Google Workspace
- Enterprise tools: SAP, Slack, Adobe, Atlassian
- Vishing vectors: Device code authentication
- OAuth abuse: Third-party application tokens
Employee monitoring essential across gaming, hospitality sectors. Combined datasets fuel targeted executive phishing campaigns.
Protection Requirements
- Deploy phishing-resistant MFA everywhere
- Monitor ShinyHunters leak site actively
- Credit monitoring for all employees
- SSO session timeout enforcement
- Device code phishing awareness training
- External breach verification services
Hospitality represents high-value target for employee data. SSN exposure drives identity theft, account takeover risks. Rapid response preserved operational continuity successfully.
FAQ
Employee data including SSNs compromised.
800K records targeted for extortion.
None; guest operations remained normal.
Complimentary credit monitoring services.
No evidence of publication/misuse found.
Vishing against SSO platforms likely.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages