109 fake GitHub repositories spread SmartLoader and StealC malware

A new malware campaign abused trust in GitHub by cloning legitimate open source projects and turning them into traps. Researchers at Hexastrike found 109 fake repositories across 103 GitHub accounts that pushed victims toward malicious ZIP files carrying SmartLoader, a LuaJIT-based loader that can fetch StealC and other payloads.
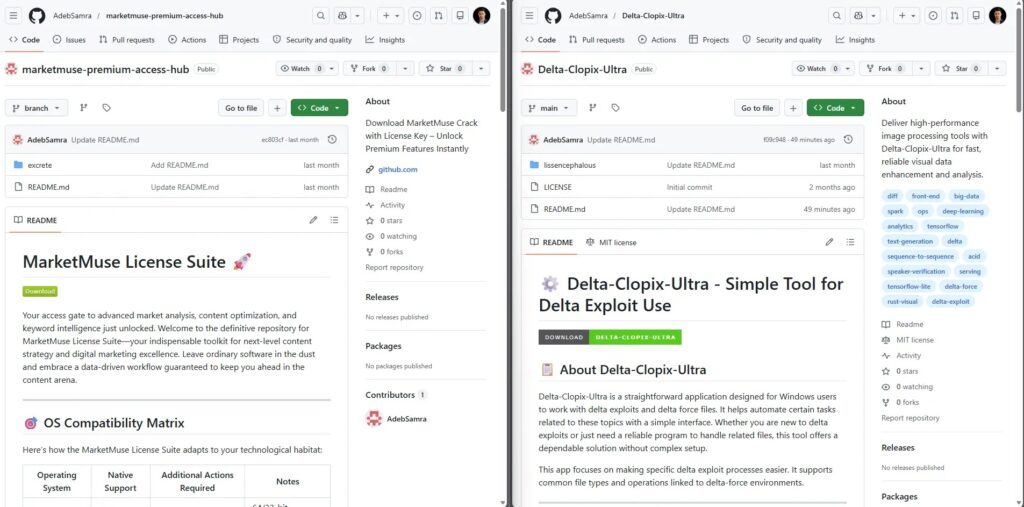
This campaign can hit regular users and developers. The fake repositories kept most of the original source code in place, but swapped real project guidance for download buttons that pointed to malware hidden inside the repo tree instead of normal releases.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The risk goes beyond one bad download. GitHub sits at the center of developer workflows, so cloned projects can look credible at a glance, especially when the attacker preserves the original code layout and only alters the README and download path. GitHub’s own documentation shows users can report malicious repositories, and GitHub also offers malware alerts and secret-scanning features for organizations trying to reduce exposure.
How the SmartLoader campaign works
Hexastrike says the operator copied real repositories, reposted them under new accounts, and buried ZIP archives deep inside repository folders. That design made the malicious download look like a normal package rather than an obvious payload.
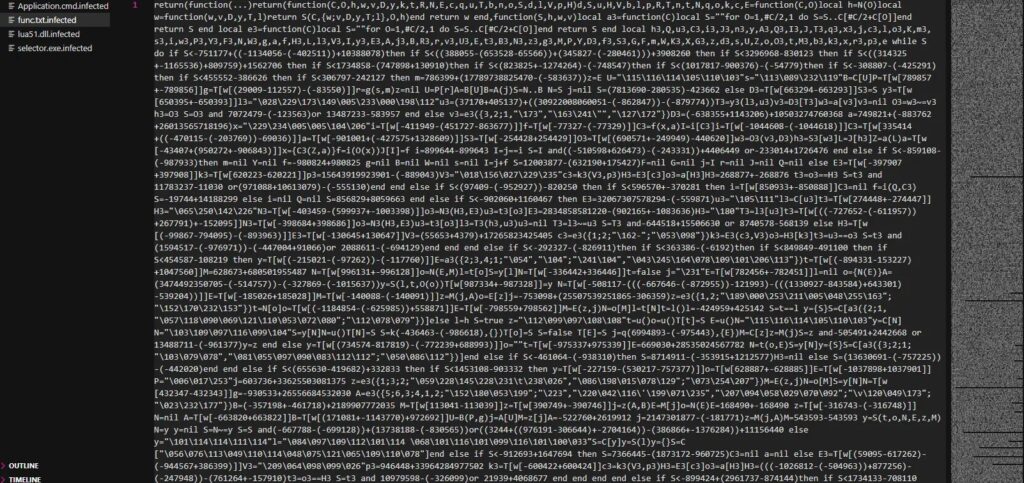
Once opened, the archive launched a batch file that started a LuaJIT interpreter and ran an obfuscated Lua script. According to the sample details published by Hexastrike and earlier SmartLoader reporting from Trend Micro, this family often hides its visible activity, fingerprints the host, and then downloads follow-on malware.
One detail makes this campaign stand out. SmartLoader used a blockchain-based dead drop resolver to pull its active command-and-control address from Polygon infrastructure, which let the operator change backend systems without rebuilding every sample.
Why this attack matters
This was not a random copycat wave. Hexastrike said the 109 repositories shared the same archive layout, staging method, README pattern, and malware family, which pointed to centralized control or a tightly managed cluster. Researchers also said the campaign stayed active for at least seven weeks, with fresh repositories still appearing as of April 12, 2026.
That timeline fits a broader pattern. Trend Micro reported a similar SmartLoader operation in 2025 that used fake GitHub repositories and AI-polished lures to spread loaders and info-stealers, showing that threat actors have kept refining this playbook instead of abandoning it.
The practical danger is simple. A user may inspect the repository, see familiar code, assume it is safe, and still get infected because the real trap sits inside a ZIP file or fake installer path rather than the visible source itself.
What security teams should watch for
| Indicator | Why it matters |
|---|---|
| ZIP files hidden deep inside a repo tree | Common lure used in this campaign |
| README download buttons instead of normal releases | Signals a cloned-project trap |
luajit.exe, Lua scripts, or odd .txt or .log script launches | Common SmartLoader execution pattern |
| Outbound calls to Polygon RPC services from non-browser processes | Possible dead drop resolver behavior |
Scheduled tasks from %LOCALAPPDATA% or user-writable paths | Possible persistence |
POST requests to bare IP addresses or suspicious /api/ and /task/ paths | Possible exfiltration or tasking |
The defensive response should start with source validation. Download software from verified release pages, not from ZIP files buried in a repository tree, and confirm the publisher identity before you run anything.
Teams should also monitor for unusual script launchers, unsigned interpreters, suspicious scheduled tasks, and outbound traffic to blockchain RPC endpoints from tools that should not be talking to them. GitHub’s docs note that organizations can use malware alerts, security features, and reporting workflows to catch or escalate suspicious content faster.
If a device touched one of these fake repos and executed the archive, responders should assume credential theft is possible. StealC is an information stealer, and GitHub’s secret-scanning guidance makes the follow-up step clear: find exposed secrets and rotate them quickly.
What to do right now
- Verify the original publisher before downloading any project archive or installer.
- Prefer official releases and tagged packages over files hidden inside repository folders.
- Block or investigate non-browser traffic to Polygon RPC endpoints if it appears on developer endpoints.
- Hunt for
luajit.exe, suspicious batch launchers, and strange scheduled tasks in user-writable paths. - Review repositories and developer machines for exposed tokens, then rotate any secrets at risk.
- Report malicious repositories directly to GitHub so the trust chain breaks faster for other users.
FAQ
Hexastrike found 109 fake GitHub repositories across 103 accounts that pushed SmartLoader and follow-on malware such as StealC through cloned open source projects and hidden ZIP archives.
It queries a Polygon-based dead drop resolver to fetch the current server details, which gives the operator more flexibility and makes takedowns harder.
They borrow the trust of real projects. Attackers often leave most of the code intact, so a quick inspection can miss the malicious download path in the README or archive structure.
Disconnect the affected device from sensitive workflows, investigate executed files, hunt for persistence, and rotate any credentials that may have been exposed. GitHub’s secret-scanning guidance supports rapid secret remediation as part of that response.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages