83% of Ivanti EPMM Exploit Attempts Traced to Single IP on Bulletproof Hosting Network

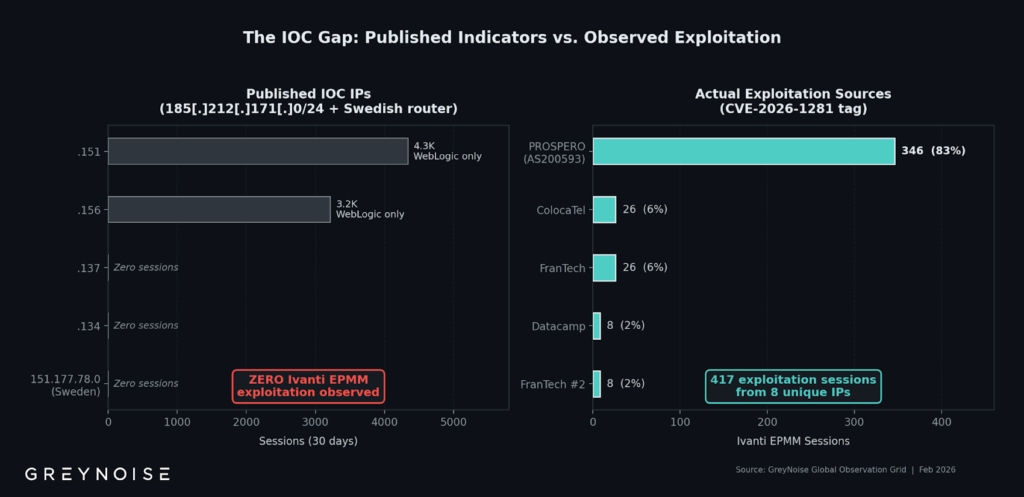
A large majority of recent exploitation attempts targeting a critical Ivanti Endpoint Manager Mobile vulnerability have been traced to a single IP address operating from bulletproof hosting infrastructure. According to threat intelligence firm GreyNoise, 83 percent of all observed exploitation sessions against the newly disclosed Ivanti EPMM flaw originated from one IP address.
Between February 1 and February 9, 2026, GreyNoise recorded 417 exploitation sessions from eight unique source IP addresses. Of those, 346 sessions were linked to 193.24.123.42, a host operating on infrastructure associated with PROSPERO. The scale and concentration of activity point to automated and coordinated exploitation.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The attacks target CVE-2026-1281, a critical Ivanti Endpoint Manager Mobile vulnerability with a CVSS score of 9.8, alongside CVE-2026-1340, another high-severity flaw that can enable unauthenticated remote code execution. Ivanti previously confirmed it was aware of a “very limited number of customers” impacted by zero-day exploitation of these vulnerabilities.
What the Data Shows
GreyNoise’s telemetry provides clear quantitative indicators of the campaign’s structure.
| Metric | Observed Value |
|---|---|
| Total exploitation sessions | 417 |
| Unique source IPs | 8 |
| Sessions from 193.24.123.42 | 346 |
| Percentage from single IP | 83% |
| Exploited CVE score | 9.8 (CVE-2026-1281) |
| Time window analyzed | Feb 1–9, 2026 |
This level of concentration suggests centralized scanning and exploitation rather than scattered opportunistic activity.
GreyNoise stated: “The IP rotates through 300+ unique user agent strings spanning Chrome, Firefox, Safari, and multiple operating system variants. This fingerprint diversity, combined with concurrent exploitation of four unrelated software products, is consistent with automated tooling.”
Simultaneous Exploitation of Multiple CVEs
The same infrastructure was not limited to Ivanti EPMM. GreyNoise observed exploitation attempts against three additional unrelated vulnerabilities:
| CVE | Software Targeted | Sessions Observed |
|---|---|---|
| CVE-2026-21962 | Oracle WebLogic | 2,902 |
| CVE-2026-24061 | GNU InetUtils telnetd | 497 |
| CVE-2025-24799 | GLPI | 200 |
The presence of 2,902 WebLogic exploitation sessions from the same infrastructure indicates a broad scanning operation targeting high-value enterprise services.
DNS Beaconing and Exploit Verification
GreyNoise further noted that 85 percent of exploitation sessions used DNS callbacks to verify exploitability before deploying any payload.
This behavior is consistent with reconnaissance and initial access brokerage. Instead of immediate ransomware or malware deployment, attackers appear to be identifying vulnerable systems for potential later use or resale.
European Agencies Confirm Targeting
Following disclosure of the vulnerabilities, several European entities reported being targeted, including:
- Dutch Data Protection Authority
- Council for the Judiciary (Netherlands)
- European Commission
- Finland’s Valtori
These confirmations indicate the campaign has geopolitical reach and is not limited to isolated enterprise victims.
Infrastructure Link to PROSPERO
The IP address 193.24.123.42 is hosted on infrastructure tied to PROSPERO, a provider often associated with bulletproof hosting services. PROSPERO is assessed to have links to Autonomous System AS200593 and Proton66, networks previously connected to malware distribution campaigns involving:
- GootLoader
- Matanbuchus
- SpyNote
- SocGholish
The historical association with malware distribution adds further risk context to the current exploitation campaign.
Why Ivanti EPMM Is a High-Value Target
Ivanti Endpoint Manager Mobile is used to manage mobile devices and enforce enterprise policies. A compromise provides access to device management infrastructure across entire organizations.
GreyNoise warned: “Organizations with internet-facing MDM, VPN concentrators, or other remote access infrastructure should operate under the assumption that critical vulnerabilities face exploitation within hours of disclosure.”
With a CVSS 9.8 score, CVE-2026-1281 ranks at the highest severity tier. Exploitation enables remote code execution without authentication, making it especially dangerous for publicly exposed systems.
Recommended Mitigation Steps
Organizations using Ivanti EPMM should take the following actions immediately:
Patch Management
- Apply vendor-issued patches for CVE-2026-1281 and CVE-2026-1340.
- Confirm patch success across all internet-facing EPMM instances.
Network Controls
- Audit DNS logs for OAST-style callbacks.
- Monitor for suspicious access to
/mifs/403.jsp. - Block traffic from Autonomous System AS200593 where feasible.
Infrastructure Review
- Inspect SSL VPN credential exposure.
- Verify integrity of Mobile Device Management servers.
- Conduct forensic analysis on any exposed system.
Key Risk Indicators at a Glance
- 83% of exploitation sessions linked to one IP
- 417 total sessions in eight days
- 300+ rotating user agents
- 85% DNS-based exploit verification
- 2,902 WebLogic exploitation sessions from same infrastructure
These numbers show scale, automation, and coordination.
Frequently Asked Questions
CVE-2026-1281, a critical Ivanti EPMM vulnerability with a CVSS score of 9.8, along with CVE-2026-1340.
GreyNoise telemetry shows 346 of 417 sessions originated from 193.24.123.42, indicating centralized automated scanning.
It suggests attackers are verifying which targets are exploitable before deploying malware.
Evidence suggests reconnaissance and initial access validation rather than immediate payload deployment.
Any organization running internet-facing Ivanti EPMM, MDM systems, VPN concentrators, or remote access infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages