Lazarus Group’s “Graphalgo” Campaign Plants Malware in npm and PyPI Packages Using Fake Job Offers

Cybersecurity researchers have uncovered a large, coordinated malware campaign linked to the North Korea–affiliated Lazarus Group that spreads malicious code through open-source package ecosystems such as npm (JavaScript) and PyPI (Python). The effort, named the Graphalgo campaign, has been active since May 2025 and targets developers with fraudulent job recruitment lures to deliver malware.
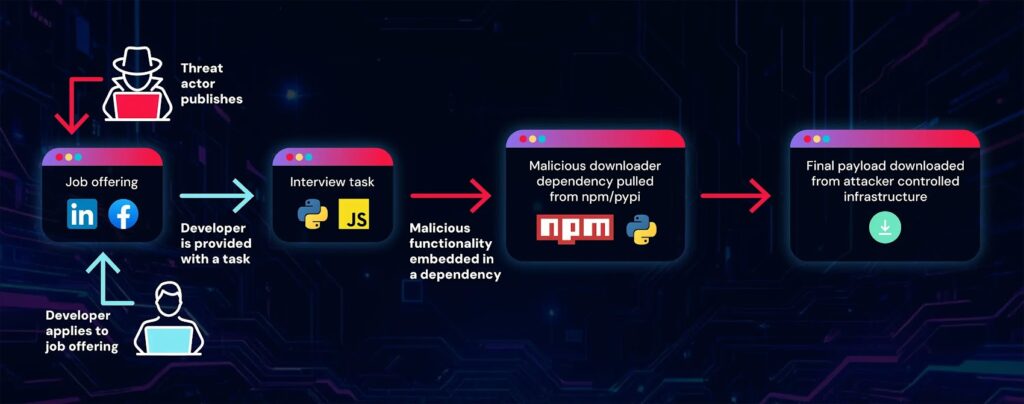
The attackers use social engineering on platforms like LinkedIn, Facebook, and Reddit to reach developers. They publish fake recruitment tasks and coding challenges that appear legitimate but include dependencies fetched from compromised or malicious packages. Once a developer runs standard package installation commands such as npm install, infected dependencies can execute code that gives attackers remote control over the victim’s system.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Official research appears on ReversingLabs’ threat research blog and is widely cited by independent cybersecurity news outlets following its release.
How the Graphalgo Attack Chain Works
The campaign relies on a combination of social tactics, fake company personas, and poisoned open-source packages.
- Fake job contacts: Attackers reach developers through social platforms with invitations to apply for technical roles related to cryptocurrency or blockchain.
- Fake company persona: A bogus entity called Veltrix Capital was created with domain names like
veltrixcap.organd corresponding GitHub accounts to host project repositories. - Malicious coding tasks: The victims are directed to GitHub repositories with seemingly normal assignments. These repositories include dependencies pointing to malicious npm and PyPI packages.
- Supply-chain infection: Developers who install packages such as bigmathutils inadvertently run code that forms part of a larger multi-stage malware attack.
- Remote access takeover: Once executed, compromised packages can install a remote access trojan (RAT) that gives attackers access to system files, process lists, and external command execution.
Official Research Quote
“Developers are approached via social platforms like LinkedIn and Facebook, or through job offerings on forums like Reddit … The campaign includes a well-orchestrated story around a company involved in blockchain and cryptocurrency exchanges.” Karlo Zanki, ReversingLabs threat researcher.
This official quote comes from ReversingLabs’ analysis of the campaign, where the researcher details how attackers embed malicious steps within what appear to be standard development assignments.
Packages and Ecosystems Affected
The attack spans two major open-source package repositories that developers rely on daily.
| Repository | Targeted by Graphalgo | Examples of Infection Vector |
|---|---|---|
| npm (JavaScript) | Yes | bigmathutils and related graph*/big themed packages that appear legitimate but execute malicious payloads. |
| PyPI (Python) | Yes | Packages mimicking graph libraries and utilities that act as malware loaders. |
The npm package bigmathutils had accumulated over 10,000 downloads in its benign first version before a malicious version was released, giving it sufficient reach to seed infections at scale.
Why Graphalgo Is More Than Simple Malware
Two aspects make this campaign notable for threat researchers:
- Social engineering hook: Attackers use fake interview tasks presented via legitimate-looking channels, making developers trust the material before installing dependencies.
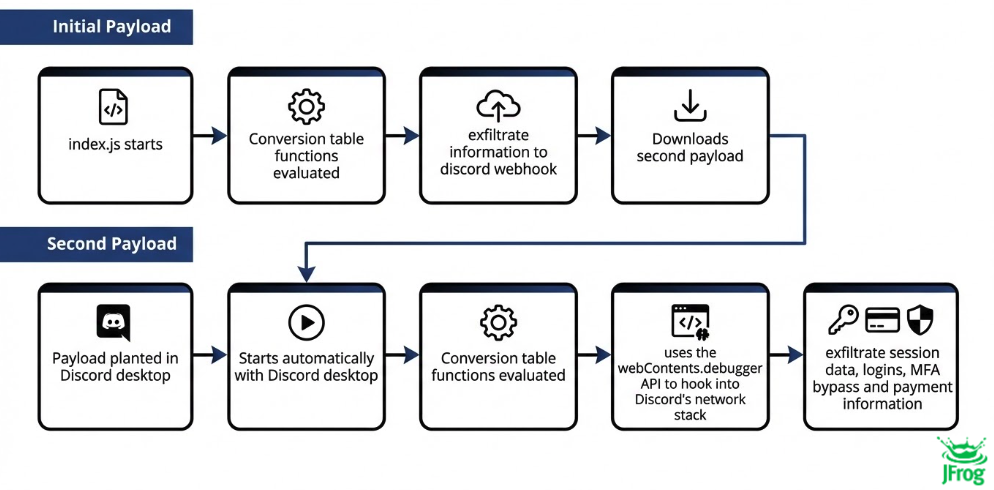
- Modular malware delivery: The attack breaks infection into stages, using package dependencies and remote control setups rather than a single monolithic drop, allowing stealth and persistence.
These traits indicate a strategic, patient operation rather than a quick exploit, consistent with long-term intrusion campaigns attributed to state-linked actors.
Risks to Developers and Organizations
Malware delivered through package repositories can have serious technical and business consequences:
- Compromised development machines: Remote access trojans installed covertly can allow attackers to steal credentials, tokens, or proprietary source code.
- Credential leakage: Malware can monitor and exfiltrate environment variables, API keys, and account data used in development workflows.
- Supply chain impact: Backdoored dependencies can propagate into CI/CD systems, leading to widespread deployment of infected artifacts.
Threat analysts have warned for years that open-source ecosystems are a battleground for malware, given their global reach and trust-based installation models.
Key Technical Features of the Graphalgo Campaign
- Attackers created fake corporate personas and web infrastructure to support recruitment lures.
- Malicious dependencies are hidden within seemingly benign repositories and package releases.
- Infection unfolds when developers install dependencies using standard tools like
npm install. - Some infected packages like bigmathutils reached large download counts before being weaponized.
- The remote access trojan provides attackers with broad command execution once installed.
Recommendations for Developers and Security Teams
Review Dependencies Carefully: Always inspect dependency names, metadata, and versions before adding them to projects.
Use Package Scanning Tools: Automate scanning for known malicious patterns and revoke or alert on suspicious packages.
Verify Recruitment Channels: Be cautious about unsolicited job offers that include code assignments and unfamiliar repositories.
Sandbox New Code: Test code in isolated environments before adding dependencies to production workflows.
Monitor Build Systems: Watch CI/CD logs and artifacts for unusual references or downloading external packages unexpectedly.
Frequently Asked Questions (FAQ)
A: It is a malicious software supply chain campaign by Lazarus Group using fake recruiter lures to distribute malware via open-source packages.
A: They contact developers through LinkedIn, Facebook, and Reddit, offering fake job tasks tied to blockchain or crypto roles.
A: Both npm for JavaScript and PyPI for Python packages are involved.
A: Yes, if infected dependencies are built into applications that run in production environments.
A: Use dependency scanners, sandbox new code, and avoid installing packages from unverified sources or unfamiliar projects.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages