Cellebrite Tool Used on Kenyan Activist's Phone in Police Custody

Citizen Lab confirmed Kenyan police used Cellebrite forensic tools on activist Boniface Mwangi’s Samsung phone during July 2025 custody. The pro-democracy leader, who plans a 2027 presidential run, got his device back in September without password protection. Extraction likely happened July 20-21, 2025.
Cellebrite tools can pull all phone data including messages, files, financial info, and passwords. Mwangi’s device showed clear forensic traces. Police held it nearly two months before return.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This follows Jordan’s use of Cellebrite on Gaza protest supporters from late 2023 to mid-2025. Devices seized during arrests came back compromised.
Cellebrite told The Guardian: “Technology used only with legal due process or consent to aid investigations.” Company claims strict client vetting.
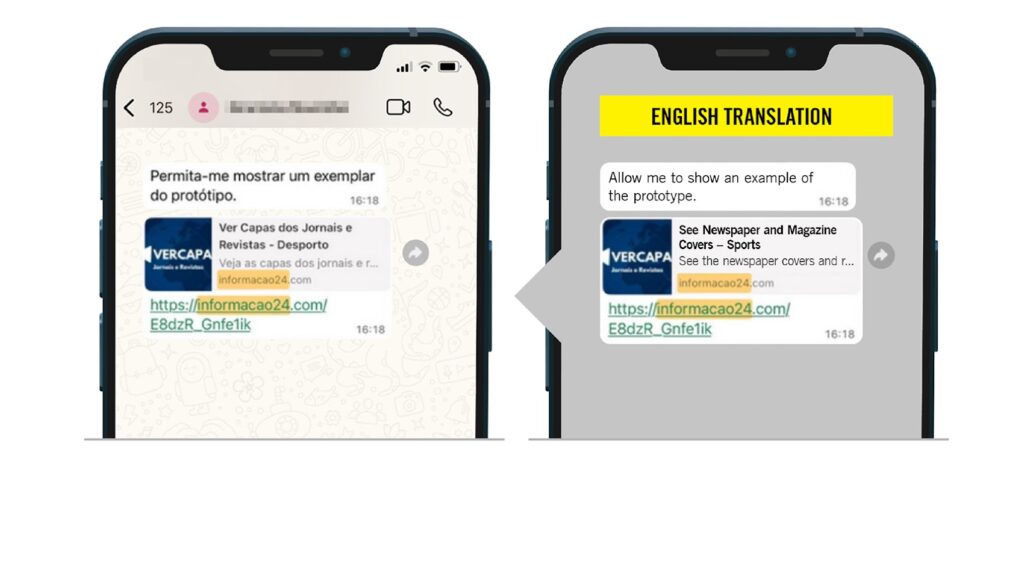
Kenyan case adds to evidence of government misuse. Amnesty International found Predator spyware on Angolan journalist Teixeira Cândido’s iPhone in May 2024 via WhatsApp link.
Predator Spyware Details
Intellexa’s Predator hit outdated iOS 16.2 device. Attackers tried 11 more infections until June 16, 2024.
| Spyware | Target | Method | Duration |
|---|---|---|---|
| Cellebrite | Kenyan activist | Police custody extraction | July 2025 |
| Predator | Angolan journalist | WhatsApp link | May 4, 2024 (1 day) |
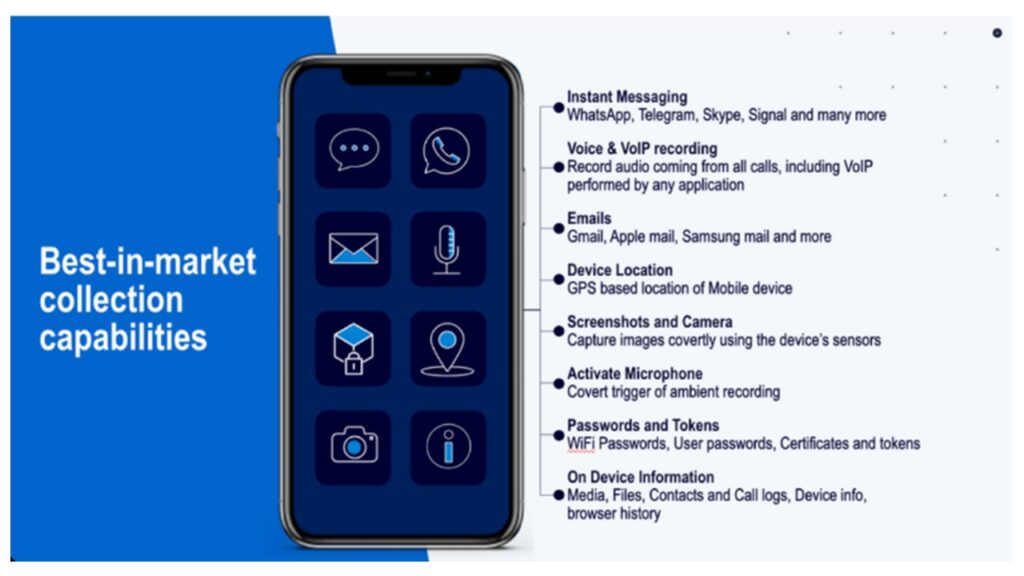
Predator uses surgical API hooking to hide recording indicators. Microphone and camera activate silently.
Predator Spyware Targets Angolan Journalist
Technical Capabilities
Cellebrite Forensic Tools:
- Full filesystem extraction
- Password bypass
- Message and app data recovery
- Deleted file reconstruction
Predator Features:
- Zero-click iMessage exploits
- SpringBoard sensor bypass
- Modular surveillance controls
- Anti-analysis crash reporting
Recorded Future confirms Predator infrastructure evolution with CDN hosting.
Pattern of Abuse
Governments increasingly use commercial spyware against civil society.
- Jordan: Gaza protest crackdown
- Kenya: Political activist targeting
- Angola: Press freedom suppression
- Iran: Protest supporter tracking
Protection Measures
- Never surrender devices to authorities
- Use full disk encryption
- Enable auto-lock with strong passcode
- Wipe devices before legal proceedings
- Document chain of custody for devices
FAQ
Used Cellebrite tools to bypass password and extract all data during custody.
July 20-21, 2025 per forensic traces.
Messages, files, passwords, financial records, private materials.
Yes, one-day infection on journalist’s iPhone via WhatsApp.
Claims legal due process required for client use.
API hooking suppresses recording indicators while spying.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages