Diesel Vortex Russian Phishing Ring Steals 1,649 Logistics Credentials Across US and Europe

Diesel Vortex Russian cybercrime group ran phishing operation against freight platforms from September 2025 to February 2026. 1,649 unique credentials stolen from DAT Truckstop, Penske Logistics, EFS, Timocom users. Phishing-as-a-Service platform GlobalProfit exposed via leaked Git server.
Operators branded service “MC Profit Always” selling access to other criminals. Spearphishing emails and vishing calls targeted trucking Telegram groups. Attackers impersonated daily-used platforms capturing credentials and MFA codes live.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
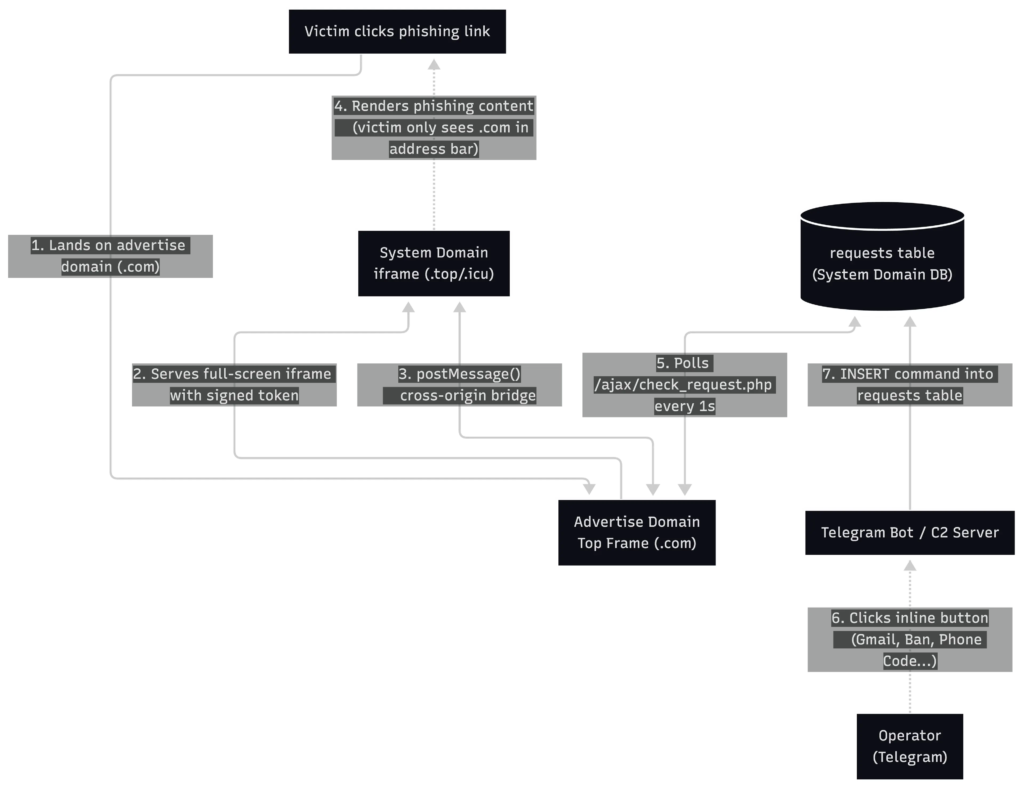
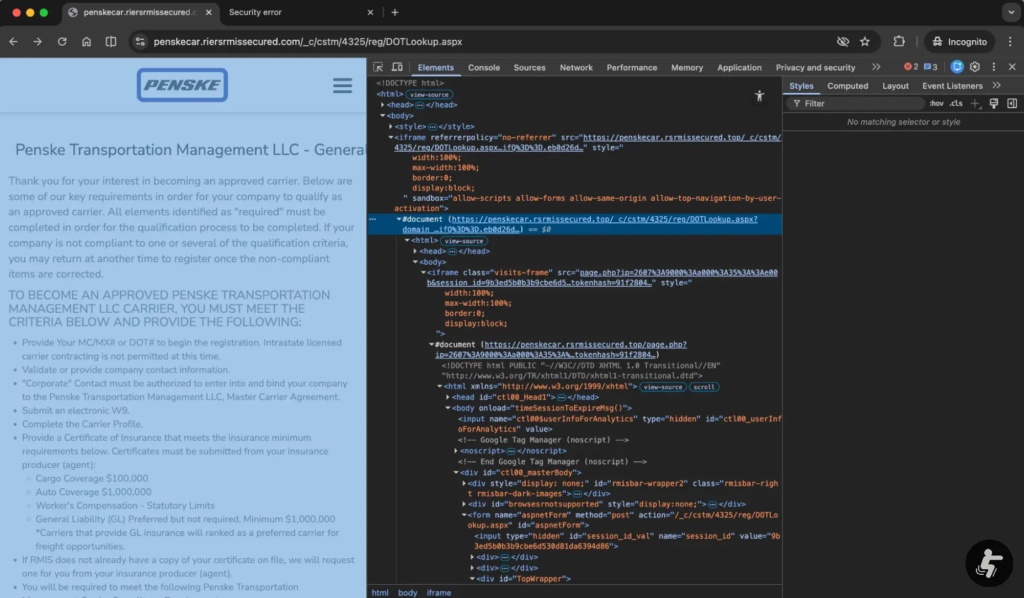
Dual-domain technique hid phishing pages in invisible iframes. Victims saw trusted advertise domains while system domains loaded malicious login forms silently. Address bar security bypassed completely.
36.6MB SQL dump revealed operational scope on February 4, 2026. 52 phishing domains deployed against 75,840 trucking emails. 35 EFS check fraud attempts confirmed alongside shipment invoice theft.
Compromised access enabled cargo redirection and double-brokering scams. Financial details fueled invoice fraud leaving original carriers unpaid. Telegram console provided real-time victim monitoring and command relay.
Exposed Git directory leaked source code, victim database, internal chat. Researchers discovered cryptocurrency payment processing for PhaaS customers. Russian-speaking buyer focus evident throughout infrastructure.
Campaign Statistics Table
| Metric | Count |
|---|---|
| Unique credentials | 1,649 |
| Credential pairs | 3,474 |
| Unique visitor IPs | 9,016 |
| Phishing domains | 52 |
| Target emails | 75,840 |
| EFS fraud attempts | 35 |
Browser security ignored iframe phishing content. Top-level trusted domains evaded warnings effectively.
Attack Infrastructure
- Advertise domains: Clean-looking legitimate mimics
- System domains: Hidden iframe phishing payloads
- Telegram C2: Real-time victim steering console
- SQL database: Victim tracking and credential storage
- Git exposure: Source code and opsec failures
FIDO2 hardware keys block real-time MFA interception. Passkeys bind authentication to devices defeating Telegram relays.
Logistics firms implement typosquatting detection. DNS filtering blocks dual-domain deception patterns. Cargo platforms push hardware token adoption rapidly.

Defensive Measures
- Deploy FIDO2 security keys universally
- Monitor logistics typosquatted domains
- Block iframe embedding from ad domains
- Hunt Telegram C2 traffic patterns
- Audit freight platform access logs
- Train staff against vishing lures
Check fraud hit EFS hardest with 35 confirmed cases. Double-brokering losses compound credential theft damage.
FAQ
DAT Truckstop, Penske Logistics, EFS, Timocom primarily.
September 2025 to February 2026, 1,649 unique credentials.
Trusted iframe hid phishing page from address bar warnings.
Leaked Git directory with source code and 36.6MB SQL dump.
EFS check fraud, cargo redirection, double-brokering.
FIDO2 hardware keys and device-bound passkeys.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages