Zyxel Patches Critical RCE Flaw Affecting 13+ CPE Router Models

Zyxel released firmware addressing CVE-2025-13942 unauthenticated RCE in UPnP function. Affects 4G LTE/5G NR CPE, DSL/Ethernet CPE, Fiber ONTs, wireless extenders. WAN access and UPnP must both enable for remote exploitation.
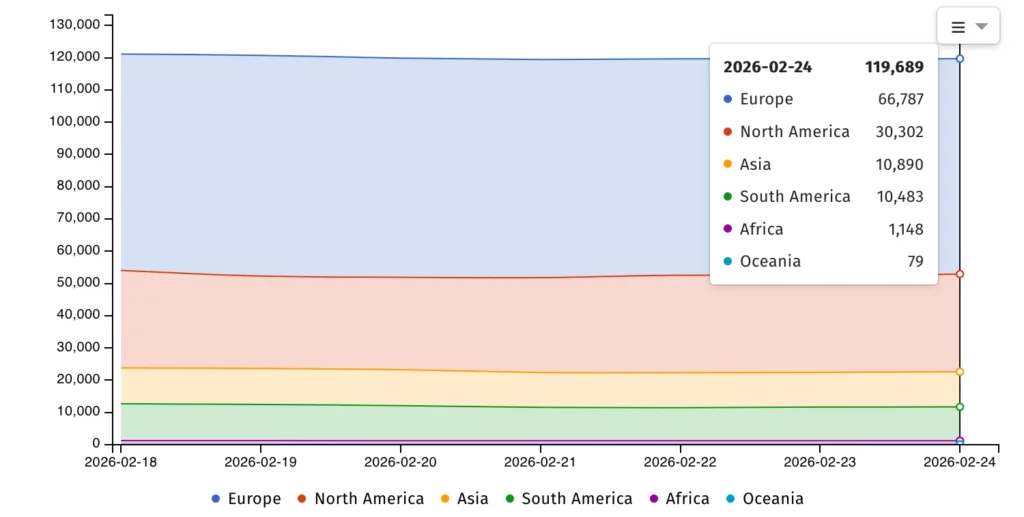
Malicious UPnP SOAP requests trigger OS command execution. WAN disabled by default limits attack surface significantly. Shadowserver tracks 120K internet-exposed Zyxel devices currently.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Two high-severity post-auth flaws patched simultaneously (CVE-2025-13943, CVE-2026-1459). Compromised credentials enable command injection. ISP-provided routers represent default gateway risk multiplier.
CISA catalogs 12 exploited Zyxel vulnerabilities in routers, firewalls, NAS. VMG1312, SBG3300, SBG3500 EOL models unpatched despite active exploits. Zyxel recommends replacement over firmware updates.
76K routers uniquely exposed per Shadowserver telemetry. 1M+ businesses deploy Zyxel across 150 markets. Enterprise CPE deployments require immediate patching priority.
Affected Product Table
| Category | Vulnerable Models |
|---|---|
| 4G/5G CPE | Multiple series |
| DSL CPE | VMG3926, VMG4325 |
| Fiber ONTs | Various models |
| Wireless Extenders | SBG3300, SBG3500 |
Attack Requirements
- WAN access enabled (disabled default)
- UPnP service active
- Malicious SOAP request delivery
- No authentication required
Default configurations block remote RCE inherently. ISP replacement cycles lag behind vulnerability disclosure.
Patching Priority
- Update firmware immediately
- Disable UPnP where possible
- Enable WAN access restrictions
- Replace EOL VMG series routers
- Monitor Shadowserver exposure
- Deploy CISA Known Exploited list
Gateway compromise enables full network access. SOHO deployments represent highest risk profile. Zyxel market dominance amplifies breach potential.
FAQ
UPnP SOAP command injection.
Must enable (disabled by default).
120K internet-facing Zyxel devices.
CVE-2025-13943, CVE-2026-1459 post-auth.
12 exploited vulnerabilities total.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages