Windows CVE-2026-2636 PoC Released: Low-Privileged BSOD Crash Exploit
A public proof-of-concept exploit now exists for CVE-2026-2636 in Windows Common Log File System (CLFS) driver. Any low-privileged user can trigger an unrecoverable Blue Screen of Death (BSOD) crash. Ricardo Narvaja of Fortra discovered this denial-of-service flaw during CLFS research.
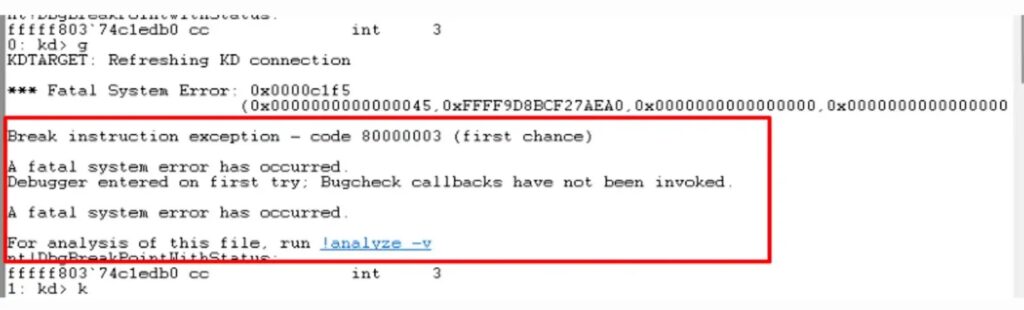
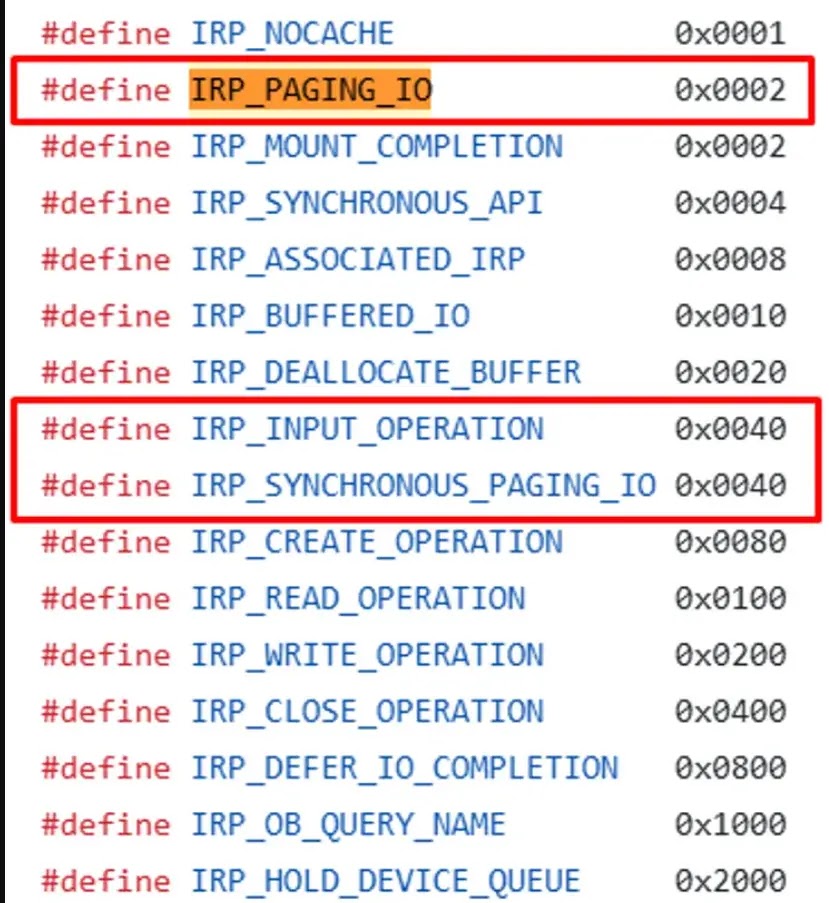
The issue lies in improper flag validation in CLFS!CClfsRequest::ReadLogPagingIo within CLFS.sys (version 10.0.22621.5037). Attackers craft an I/O Request Packet (IRP) with both IRP_PAGING_IO and IRP_INPUT_OPERATION flags disabled. This sends the driver down a faulty path straight to nt!KeBugCheckEx, the kernel panic handler.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Microsoft fixed it silently in the September 2025 cumulative update for Windows 11 2024 LTSC and Windows Server 2025. Windows 11 25H2 includes the patch from launch. Older versions like Windows 11 23H2 remain exposed.
Technical Breakdown
The PoC uses just two standard Windows API calls from user space. First, CreateLogFile grabs a valid .blf log file handle. Then, ReadFile targets that handle immediately. CLFS expects paging or input flags set for such reads. With flags off (AL=0x0), it mishandles the request.
This triggers a deterministic crash chain. KERNELBASE!ReadFile escalates to nt!NtReadFile, through CLFS dispatch routines, ending in KeBugCheckEx. No elevated privileges, binaries, or heap spraying needed. CVSS score sits at 5.5 due to local attack vector but high impact.
The flag value 0x42 lacks public Microsoft documentation. This gap aided the unexpected behavior. Core Security blog confirms reproducibility across tested setups.
Exploit Simplicity
Attackers need no special tools. A simple script runs the API sequence. Shared enterprise systems face high risk from untrusted local users. Kiosks and multi-user workstations become prime targets.
Fortra’s analysis shows the BSOD hits instantly. Systems enter unrecoverable state, halting all operations. Recovery demands full reboot.
CLFS vulnerabilities recur often. Past flaws include CVE-2022-37969, CVE-2023-28252, CVE-2024-6768, and ransomware-hit CVE-2025-29824. All trace to CLFS.sys.
Affected Versions and Fixes
| Windows Version | Status | Fix Details |
|---|---|---|
| Windows 11 23H2 | Vulnerable | Apply Sept 2025 update or later |
| Windows 11 2024 LTSC | Patched | September 2025 cumulative |
| Windows Server 2025 | Patched | September 2025 cumulative |
| Windows 11 25H2 | Patched | Ships with fix |
Mitigation Steps
- Deploy September 2025 or newer cumulative updates now.
- Upgrade supported systems to Windows 11 2024 LTSC or 25H2.
- Limit local logon rights on critical machines.
- Monitor ReadFile calls against CLFS log handles.
- Audit multi-user environments first.
FAQ
CLFS driver mishandles ReadFile on log handles with disabled paging/input flags.
Ricardo Narvaja from Fortra. PoC published via Core Security.
Windows 11 23H2 and earlier; fixed in Sept 2025 updates.
Two API calls from low-priv user space. No admin rights needed.
5.5 (Medium), local vector, high denial-of-service impact.
Install latest cumulative updates; prioritize unpatched 23H2 systems.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages