Aeternum Botnet Turns Polygon Blockchain into Immune Command‑and‑Control
A new botnet loader, Aeternum C2, stores its commands on the Polygon blockchain instead of on a server or domain. Qrator Labs researchers uncovered the loader while tracking underground cybercrime forums, and their analysis shows a botnet designed to survive traditional takedowns.
Commands are written as transactions and smart‑contract calls on Polygon. Infected machines read them by querying public RPC endpoints rather than contacting a central C2 server. Since blockchain data is replicated across thousands of nodes worldwide, there is no single server, domain, or IP address that law enforcement or security teams can seize or suspend.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Qrator describes Aeternum as a native C++ loader available in both 32‑bit and 64‑bit builds for Windows. It behaves like a next‑generation botnet orchestrator, built as a commercial product for underground markets that want highly resilient infrastructure.
How the Aeternum C2 architecture works
Aeternum replaces classic C2 patterns with a blockchain‑based workflow:
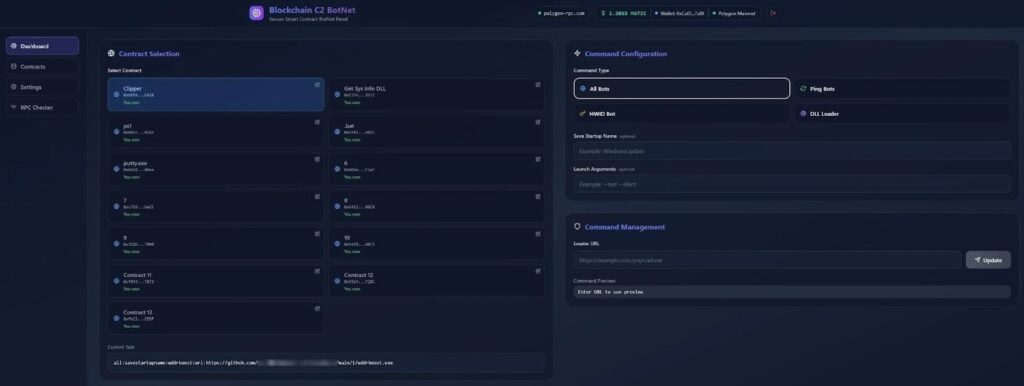
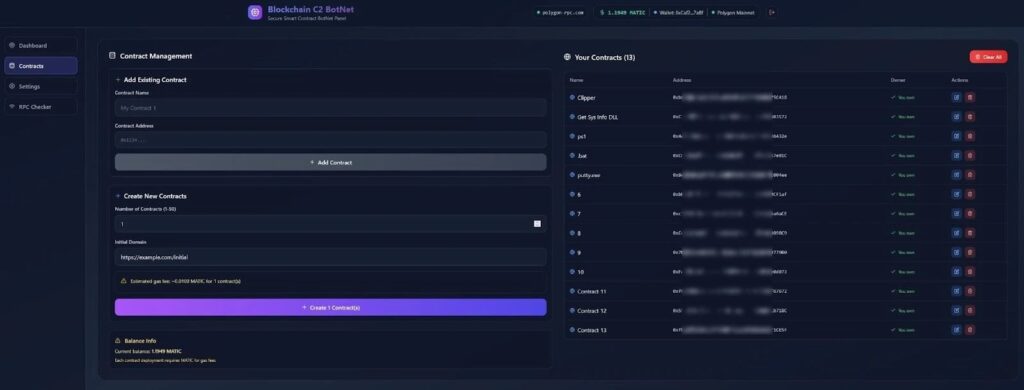
- The operator controls the botnet through a web‑based panel.
- From the panel, they choose a Polygon smart contract, pick a command type (for all bots, a specific HWID, or a payload push), and set a payload URL.
- The command is then written to the blockchain as a transaction or contract‑state update.
- Infected bots poll public RPC endpoints every few minutes to read the latest on‑chain instructions.
The malware author claims that commands reach active bots in roughly two to three minutes, which is faster and more reliable than many legacy peer‑to‑peer botnets.
Because blockchain transactions are immutable, nobody except the attacker’s wallet owner can change or delete them. This means:
- The botnet’s C2 logic stays online as long as Polygon itself is running.
- Even if all infected machines are cleaned, the attacker can redeploy new bots that immediately read the same contracts.
The cost side is also minimal. Around $1 worth of MATIC covers 100–150 command transactions, removing the need to rent servers, buy domains, or maintain hosting bills.
Persistence, evasion, and operator features
Aeternum is sold on underground forums as:
- A lifetime license with a preconfigured build, or
- Full C++ source code plus ongoing updates.
This makes it easy to customize for different payloads and attack patterns.
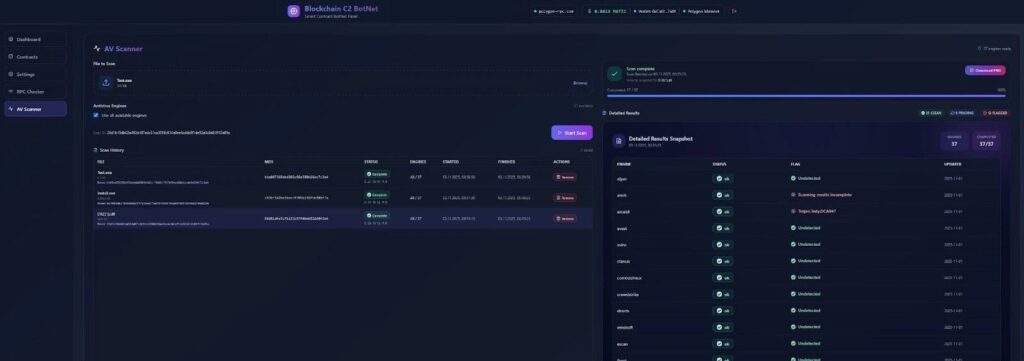
The loader’s anti‑analysis and persistence features include:
- Anti‑VM detection: Checks for virtualized environments typically used by AV vendors and malware researchers, blocking execution in those cases.
- Behavioral checks: Scans the host environment to avoid detection, similar to techniques seen in other advanced loaders.
- Scan‑time grading: The vendor bundles a built‑in scanner powered by Kleenscan‑like APIs that shows detection rates across roughly 37 engines. In tests, about 12 engines flagged the sample, while CrowdStrike, Avast, Avira, and ClamAV returned clean results.
The control panel allows operators to run multiple smart contracts simultaneously, each linked to a different function:
| Smart‑contract use case | Botnet function |
|---|---|
| Clipper modules | Alters crypto‑transaction addresses to steal funds. |
| Information‑stealing DLLs | Harvests credentials, cookies, and local files. |
| PowerShell / batch scripts | Executes arbitrary commands on the host. |
| Remote access tools (RAT) | Enables manual control of infected machines. |
| Cryptocurrency miners | Runs miners in the background for crypto profit. |
This modular design lets attackers rapidly pivot between data‑exfiltration, DDoS, click‑fraud, proxy‑as‑a‑service, and crypto‑mining campaigns using the same C2 structure.
What this means for defenders and law enforcement
Traditional botnet takedown tactics—finding a C2 server, seizing its domain, and blocking IPs—do not work against Aeternum. The infrastructure now resides inside a public, decentralized ledger.
Security teams and network defenders need to shift focus:
- Endpoint‑centric detection: Use EDR and host‑based tools to spot suspicious C++ loaders, unusual process‑creation chains, and anti‑VM or scanning activity.
- Network‑level filtering: Monitor and potentially restrict outbound traffic to public Polygon RPC endpoints if it is not needed by legitimate services.
- Threat‑intel integration: Share wallet addresses, contract hashes, and observed C2‑pattern IoCs with blockchain‑analytics providers and ISACs.
As long as the botnet’s code is not blocked at the host level, the attacker can keep pushing commands as long as the blockchain exists. This makes Aeternum a notable example of how cybercriminals are turning decentralized infrastructure into a “takedown‑resistant” weapon.
Quick‑reference table: Aeternum C2 characteristics
| Feature | Aeternum C2 behavior |
|---|---|
| Primary C2 medium | Polygon smart contracts and transaction data. |
| Language / platform | Native C++ loader for Windows (x32/x64). |
| Operator control | Web‑based panel, multiple smart contracts. |
| Evasion checks | Anti‑VM, behavioral checks, built‑in scan‑tool. |
| Distribution model | Lifetime license or full source code on forums. |
| Infrastructure cost | About $1 MATIC for 100–150 commands. |
How organizations can reduce risk from Aeternum‑style bots
- Block untrusted loaders: Use application‑control policies to block unsigned C++‑based loaders and suspicious executables from temporary folders.
- Harden endpoints: Enforce EDR, behavior‑based detection, and memory‑protection settings on Windows hosts.
- Segment network access: Limit outbound traffic to RPC‑style endpoints unless explicitly required for business.
- Scan for embedded code: Use static‑ and dynamic‑analysis tools to flag files with anti‑VM, C2‑like logic, or crypto‑related behaviors.
- Track blockchain‑related IoCs: If your SOC deals with crypto‑threats, build feeds for Polygon wallet addresses and contract hashes tied to malware.
Aeternum C2 shows how modern botnets borrow cloud and blockchain patterns for attack resilience. For security teams, it marks a point where domain‑based takedowns no longer guarantee disruption, and defense must move much earlier into the host and network‑edge layers.
FAQ
Aeternum C2 is a C++‑based botnet loader that uses Polygon‑chain smart contracts and transactions as its command‑and‑control channel, making it highly resistant to traditional takedowns.
The commands live on the Polygon blockchain, which is replicated across thousands of nodes. There is no single server, domain, or IP to seize.
Aeternum is a native C++ loader for 32‑bit and 64‑bit Windows systems.
It uses anti‑VM checks, obfuscated command‑delivery via smart‑contract data, and public RPC endpoints that blend with normal traffic.
Qrator and other analysts warn that Aeternum is likely the first commercially packaged example of a Polygon‑based C2, but it signals a broader trend of botnets moving toward decentralized, blockchain‑backed infrastructure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages