How CISOs can build a high-impact Tier 1 SOC in three practical steps

A high-impact Tier 1 team does not start with more dashboards or more alerts. It starts with better visibility, faster context, and cleaner workflows. Tier 1 analysts make the first decisions that shape detection speed, escalation quality, and response cost, so when they lack context or face too much noise, the whole SOC slows down. CISA’s SIEM and SOAR guidance says these platforms improve visibility into network activity and help organizations detect and respond faster, while NIST’s incident handling guidance stresses rapid detection, analysis, and containment as core goals of incident response.
That is why Tier 1 matters so much. This is the layer that triages the most alerts, closes the most false positives, and decides what moves to Tier 2 or Tier 3. If Tier 1 works well, MTTR drops, escalation quality improves, and senior analysts spend more time on real incidents. If Tier 1 struggles, the SOC turns reactive fast.
The sample article gets the overall direction right, but it leans too hard into broad claims. A stronger version should separate what security leaders broadly agree on from what ANY.RUN officially says its products do. The best three-step framework is still useful: improve monitoring with fresh intelligence, enrich alerts at triage, and integrate those capabilities into the existing stack.
Why Tier 1 breaks down so often
Tier 1 analysts face the hardest combination in the SOC: high volume, low time, and limited context. That makes three problems show up again and again.
- Too many alerts with weak signal
- Too much manual research before escalation
- Too many tools that do not share context cleanly
CISA’s practitioner guidance on SIEM and SOAR exists for exactly this reason. The agency says better log prioritization, automation, and integrated workflows help teams identify and respond to threats faster. In plain language, good visibility and better enrichment reduce wasted time.
The three steps CISOs should focus on
| Step | Goal | Why it matters |
|---|---|---|
| 1. Improve monitoring | Feed fresher, verified indicators into detection | Reduces missed threats and cuts noise earlier |
| 2. Enrich alerts faster | Give Tier 1 analysts real context at triage time | Improves confidence and escalation quality |
| 3. Integrate the workflow | Push intelligence into SIEM, SOAR, firewalls, and analyst tools | Cuts manual effort and speeds response |
Step 1: Improve monitoring with live intelligence
The first step is not “write better rules” in isolation. It is giving your monitoring layer better data. Static rules age quickly. Attackers change infrastructure, malware changes delivery patterns, and yesterday’s clean domain becomes today’s malicious one.
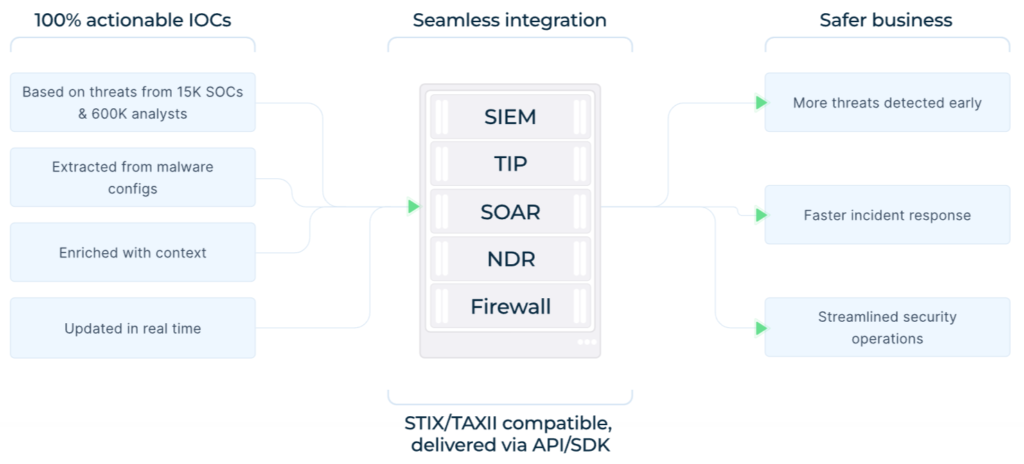
ANY.RUN says its Threat Intelligence Feeds deliver malicious IPs, domains, and URLs drawn from malware analysis and live investigations. The company also says the feeds support STIX/TAXII and MISP formats, which makes them easier to use in SIEM, SOAR, TIP, EDR/XDR, and firewall workflows.
That matters because detection improves when the monitoring layer gets fresher, behavior-linked indicators instead of relying only on old signatures or generic anomaly logic. ANY.RUN also says its feed objects include timestamps, threat labels, and links back to related sandbox sessions, so analysts can see not just the IOC, but also where it came from and what it is tied to.
A recent ANY.RUN release note adds a few more concrete points. The company says its feeds are ready for MISP, SIEM, or SOAR platforms, and that they deliver verified malicious network IOCs sourced from activity across 15,000+ organizations. That is a vendor claim, not an independent benchmark, but it does support the argument that the product is built for detection workflows rather than just ad hoc lookups.
Step 2: Enrich every alert with context Tier 1 can actually use
Better monitoring helps, but Tier 1 still needs a fast answer to the same question on almost every case: “Is this actually bad?”
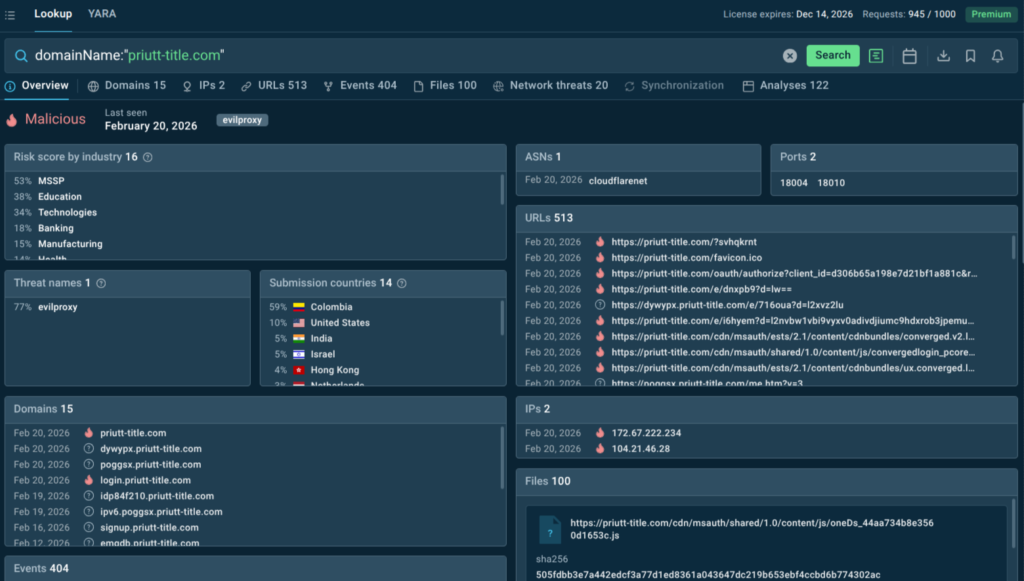
That is where enrichment matters. A raw domain, URL, IP, or hash is often not enough. Analysts need behavior, verdict, related infrastructure, malware family, and ATT&CK context if they want to make faster and cleaner decisions.
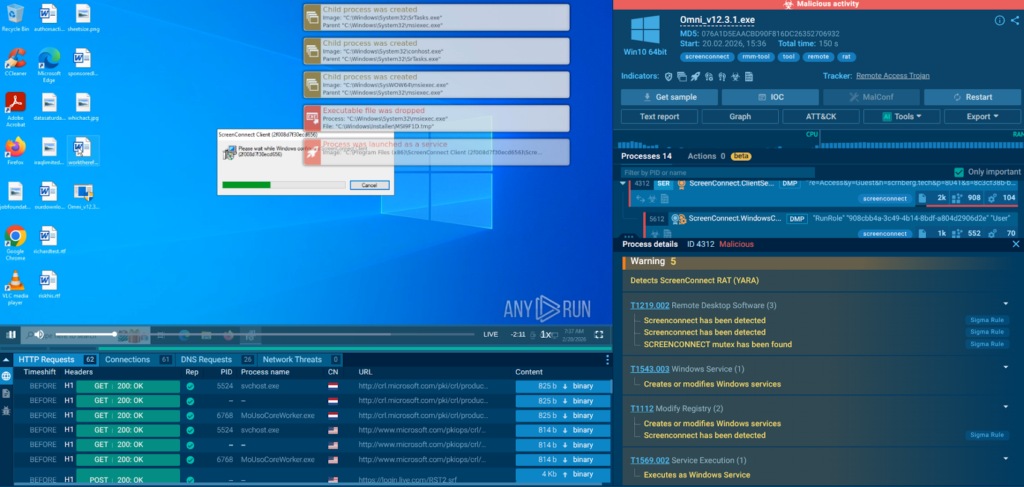
ANY.RUN says its TI Lookup product gives analysts searchable access to IOCs, events, and related analysis data, while the Interactive Sandbox lets teams submit files and URLs for behavior-based analysis and review the results in real time. Its SDK and product descriptions also say teams can submit artifacts programmatically and pull back reports, which supports use in triage and automation workflows.
The recent MISP integration note makes the value clearer. ANY.RUN says analysis results returned into MISP can include a verdict, risk assessment, extracted IOCs, a direct link to the sandbox session, an HTML report, and mapped MITRE ATT&CK techniques and tactics. That turns an alert into something closer to an evidence-backed finding.
For Tier 1, this changes the job in practical ways:
- Analysts spend less time guessing
- False positives close faster
- Escalation notes get stronger
- Tier 2 sees better handoffs
- MTTR improves because the first decision gets made faster
Those benefits come partly from logic and partly from the vendor’s own claims. The workflow improvement is a reasonable inference. The specific product capabilities come from ANY.RUN’s official materials.
Step 3: Integrate the intelligence into the stack you already own
The final step is where most security investments either compound or stall. Strong tools create limited value when they live in separate tabs and force analysts to copy data around manually.
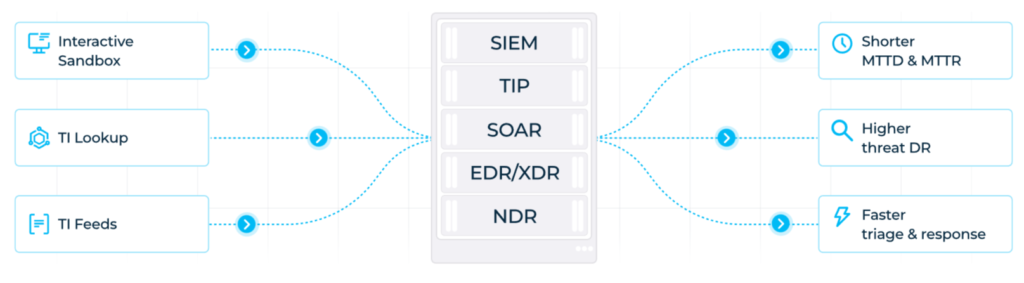
ANY.RUN’s official materials say its feeds integrate through STIX/TAXII, and that the company also offers API and SDK options. Its blog and SDK documentation also point to direct support for workflows involving MISP, custom scripts, and security operations tooling.
That makes the business case straightforward:
- SIEMs get fresher indicators
- MISP gets direct analysis results
- SOAR playbooks gain better input data
- Analysts can enrich cases without leaving their main tools
- Tier 1 spends less time on repetitive manual work
CISA’s guidance supports this broader architecture. The agency says SIEM and SOAR implementation helps organizations improve visibility and automate parts of detection and response. That is the exact kind of environment where integrated feeds, sandbox results, and IOC lookup tools create the most value.
What I would keep, and what I would soften from the sample
The sample article gets the structure right, but it should be more careful in a few places.
| Sample claim | Better way to present it |
|---|---|
| Tier 1 is the “least supported” layer everywhere | Say this is a common problem, not a universal fact |
| Intelligence feeds directly reduce MTTR | Say they can help reduce MTTR when integrated well |
| ANY.RUN solves Tier 1 fragility without added complexity | Say it can reduce manual work, depending on the stack and rollout |
| Product benefits are stated as facts | Label them as vendor capabilities or vendor-reported outcomes where needed |
That keeps the article credible. It also makes the sales angle feel less inflated.
A cleaner conclusion
Building a strong Tier 1 team is not just a staffing problem. It is a workflow and context problem. CISOs get the biggest return when they improve three things in order: monitoring quality, triage context, and integration depth.
ANY.RUN’s official materials support that positioning. The company offers Threat Intelligence Feeds in STIX/TAXII and MISP formats, an Interactive Sandbox for behavior-based analysis, and TI Lookup plus API/SDK options for enrichment and automation. CISA’s guidance supports the broader strategy behind that stack: better visibility, faster detection, and more efficient response through integrated security operations tooling.
The best Tier 1 teams do not win because they review more alerts. They win because they get better inputs, better context, and better workflows.
FAQ
Tier 1 handles first-line monitoring and triage, so it shapes what gets escalated, what gets closed, and how fast incidents move toward containment. CISA’s SIEM and SOAR guidance ties better visibility and faster response directly to stronger security operations.
Too much noise and not enough context. Analysts often face large alert volumes with limited time and incomplete enrichment, which slows decisions and increases fatigue.
ANY.RUN says it offers Threat Intelligence Feeds in STIX/TAXII and MISP formats, an Interactive Sandbox for live malware analysis, TI Lookup for IOC and event search, and API/SDK support for integration.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages