Operation Leak dismantles LeakBase cybercrime forum, authorities secure user data and IP logs
U.S. and international law enforcement agencies have seized LeakBase, a major cybercrime forum that sold and traded stolen data and hacking tools. The U.S. Department of Justice says investigators seized LeakBase’s infrastructure and user data as part of Operation Leak, a coordinated operation that involved multiple countries.
Visitors who try to reach LeakBase now see a seizure banner. Reporting and law enforcement statements say authorities also secured forum records that include accounts, posts, private messages, and IP logs for evidentiary purposes.
Europol says LeakBase had more than 142,000 registered users and operated as a marketplace for leaked databases and “stealer logs,” which attackers often use for account takeover and fraud.
What happened
The DOJ says the United States led the dismantlement effort, with support from international partners, and used court-authorized seizure procedures to take control of LeakBase’s infrastructure and data.
Europol describes LeakBase as a large forum that enabled criminals to buy and sell stolen credentials and data dumps, including infostealer-derived logs. Europol also says investigators ran coordinated actions across participating countries as part of the takedown.

Key facts
| Item | Details |
|---|---|
| Operation name | Operation Leak |
| Platform | LeakBase cybercrime forum |
| What authorities seized | Forum infrastructure and user data |
| Evidence preserved | Accounts, posts, private messages, IP logs (per law enforcement statement) |
| Scale | Europol says LeakBase had 142,000+ registered users |
| Primary focus | Stolen databases, credentials, stealer logs, and related illicit services |
Why this takedown matters
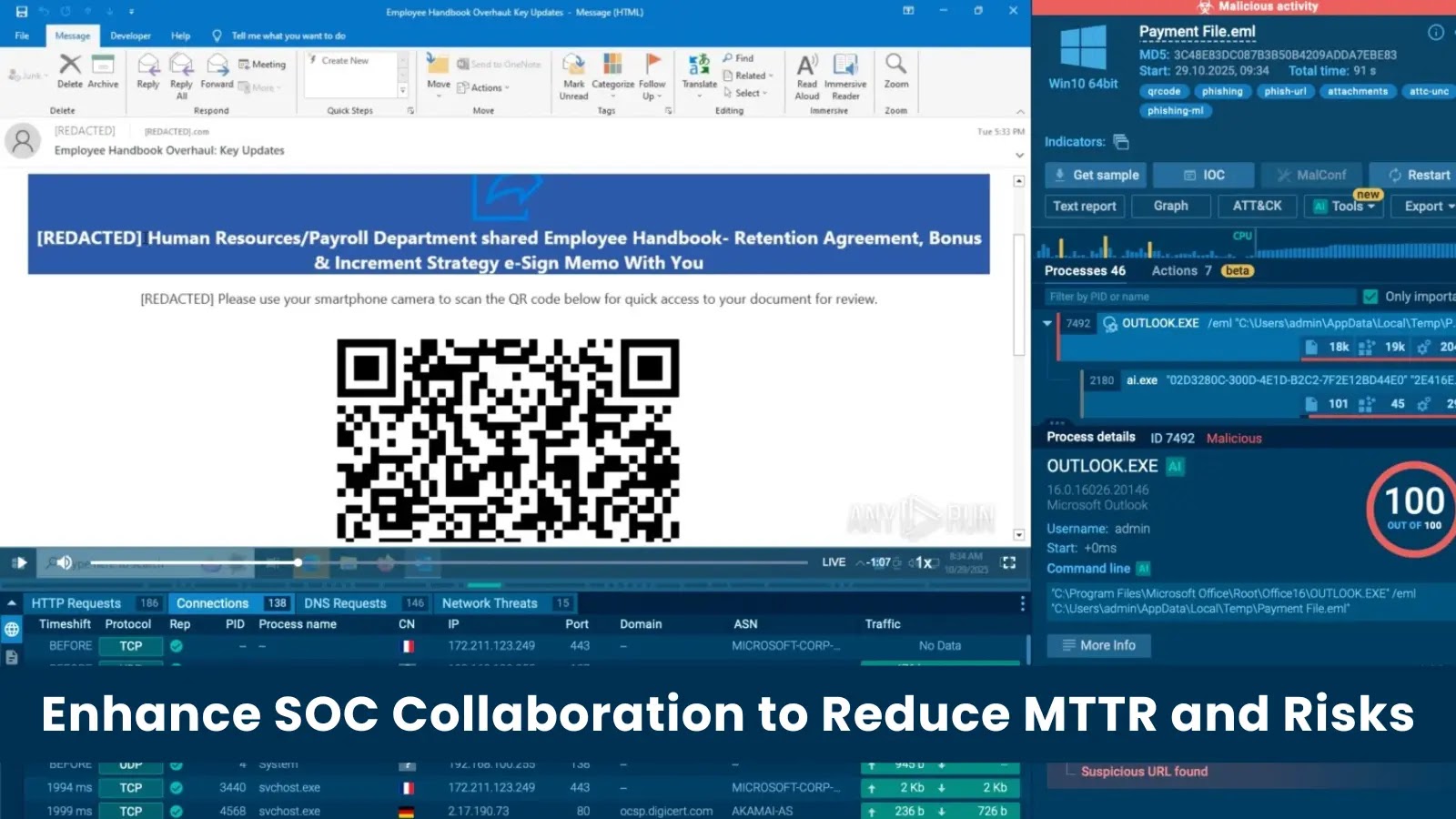
LeakBase sat on the open web and served an English-speaking audience, which lowered the barrier for buyers and sellers of stolen data. That kind of forum can speed up account takeover, business email compromise, fraud, and follow-on intrusions because criminals can shop for fresh credential sets and infostealer logs at scale.
The seizure also creates direct investigative risk for forum members. Law enforcement says it preserved core user records and communications for evidentiary purposes, which can help investigators map identities, infrastructure, and payment flows tied to cybercrime activity.
What defenders should do now
- Review recent credential stuffing and account takeover alerts for patterns that match infostealer log reuse.
- Rotate credentials for accounts that show signs of reuse, especially admin, VPN, email, and cloud accounts.
- Add controls that reduce credential replay, including MFA, conditional access, and device-based risk checks.
- Monitor for new credential leaks tied to your brand and run takedown and reset workflows quickly.
- Assume criminals will migrate to another marketplace and keep pressure on detection for stealer-driven fraud.
Europol’s description of LeakBase’s focus on stealer logs supports these steps because stealer logs often drive fast downstream abuse.
FAQ
LeakBase operated as a cybercrime forum that supported the sale and exchange of stolen data, including credentials and stealer logs, according to Europol and the DOJ.
Authorities seized LeakBase’s infrastructure and preserved user and forum data for evidentiary purposes, according to official statements and reporting.
Europol says the forum had more than 142,000 registered users.
Yes. Law enforcement statements say investigators preserved accounts, posts, messages, and IP logs as evidence.
No. Takedowns disrupt infrastructure and create pressure, but sellers often move to new forums. Defenders should keep hunting for infostealer-driven credential abuse.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages